Maximize Your Bandwidth: Proven Techniques for Optimal Utilization
Poor loading speeds and network outages frustrate users enough to abandon their business tools completely.
Organizations worldwide now find that outdated network infrastructure and inefficient bandwidth tools directly affect their profits through decreased productivity and poor user experience.
Networks have become more complex, making optimization a significant priority. Research indicates 43% of organizations manage WAN or SD-WAN networks.
Bandwidth optimization has become their top concern.
Your network performance plays a vital role in business success, whether you face challenges with old routers, incorrect cabling, or software problems.
This piece outlines proven methods and practical solutions to optimize your network’s bandwidth usage.
You will learn ways to spot performance bottlenecks, set up monitoring strategies, and select the right tools that keep your network running at its best.
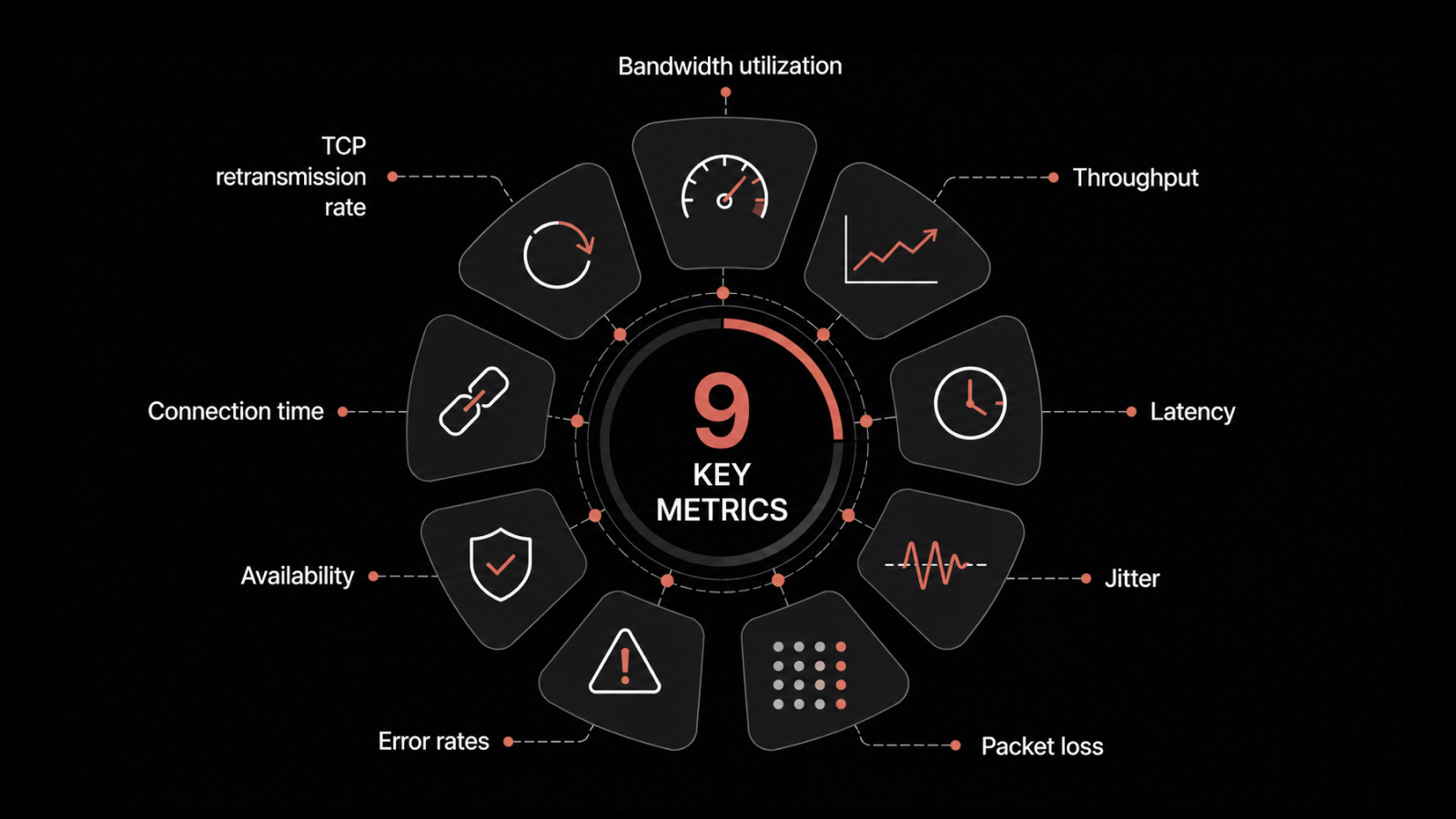
Key Metrics for Monitoring Bandwidth Utilization
Network managers need to track key performance indicators that show their network’s health and efficiency.
These metrics help you spot bottlenecks, plan upgrades, and optimize resources before users face any issues.
Let’s look at the essential bandwidth metrics you should track in your monitoring strategy.
Average Bandwidth Usage
Average bandwidth usage shows how much data moves through your network during a specific time period. This metric sets a baseline for normal operations and helps analyze trends.
Your network’s capacity usage during normal operations becomes clear when you measure average bandwidth.
The measurement units are bits per second (bps), kilobits per second (Kbps), or megabits per second (Mbps).
Regular monitoring of average bandwidth helps you:
- Spot patterns and unusual network traffic
- Set standards for normal operation
- Make smart choices about resource allocation
Network admins use this baseline data to estimate future bandwidth needs and decide the right time for upgrades.
A good grasp of usage patterns also helps create better traffic shaping policies that put critical applications first.
Peak Bandwidth Usage
Average metrics give you a baseline, but peak bandwidth usage shows the highest network demand at specific times.
This metric plays a vital role in capacity planning by revealing if your infrastructure can handle high-traffic situations.
Peak bandwidth shows the highest percentage of network bandwidth used during specific times, like busy hours.
This number matters because network issues usually pop up during these peak times rather than during average use.
SaaS providers and businesses that rely on cloud apps need to watch peak usage closely. It directly shapes how end users experience these platforms.
If peak usage often gets close to your maximum capacity, you’ll need to upgrade your infrastructure or find ways to optimize.
Bandwidth Utilization Percentage
This percentage shows how much data moves through your network compared to its total capacity. The calculation looks like this:
Bandwidth Utilization (%) = (Traffic Volume / Total Available Bandwidth) × 100
A network with 100 Mbps capacity that sends data at 50 Mbps has 50% bandwidth utilization. This percentage helps you:
- See if your network runs efficiently
- Know when you’re reaching capacity limits
- Get ready for future growth
Your network might need an upgrade if utilization stays above 70-80% of capacity. High rates can slow down links and applications, especially during important business operations.
Latency
Latency tells you how long data takes to travel between network points. Real-time applications like video calls, VoIP, and online gaming depend heavily on this metric.
Several things affect latency, which we measure in milliseconds (ms):
- Distance between connected devices
- Network hops between devices
- Network traffic volume
- Hardware processing time
SaaS apps and cloud services slow down with high latency, which leads to poor user experience. Networks with low latency feel quick, while high latency makes everything seem slow.
Tracking latency helps set performance standards and quickly finds delayed network paths.
You can also spot problems with security processes, router errors, or software issues that might hurt network performance.
Packet Loss
Data packets sometimes fail to reach their destination – that’s packet loss. Even small amounts can really hurt how well applications work.
Here’s what packet loss does:
- 1% packet loss cuts network throughput by 70.7%
- 2% packet loss reduces throughput by 80.5%
- Users notice voice and video problems when packet loss tops 0.5%
Network congestion, broken hardware, or weak signals usually cause packet loss. Businesses using SaaS apps might get corrupt data or no data at all when packet loss is high.
This leads to incomplete transfers, poor call quality, and slower connections.
Application performance drops when TCP retransmissions go above very low single-digit percentages.
Most applications work fine with packet loss under 1-2%, though critical systems might need even lower rates.
A good bandwidth monitoring tool that tracks these five key metrics will help you optimize your network, keep performance steady, and give users reliable service.
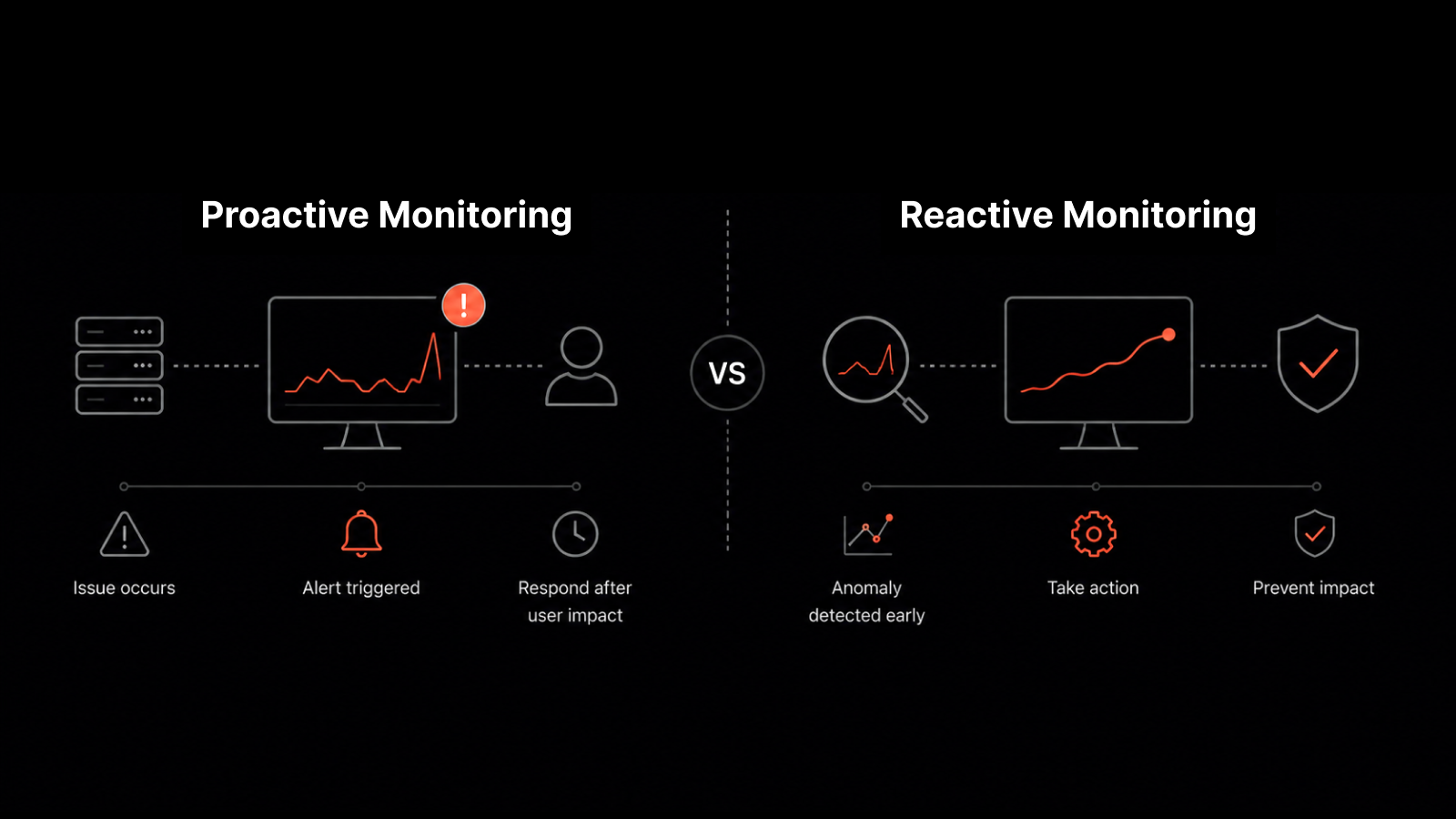
Watch these numbers regularly and set up alerts to catch problems early instead of fixing them after they cause trouble.
Bandwidth Utilization Technique: Prioritization and Optimization
Your next critical step comes after measuring your network’s performance metrics – implementing the right optimization techniques.
Network optimization requires smarter use of existing resources rather than just adding more bandwidth.
Here are four powerful techniques that will substantially improve your network bandwidth use.
Quality of Service: Prioritize Critical Traffic
Quality of Service (QoS) acts like a traffic controller for your network. It makes sure critical applications get the bandwidth they need exactly when they need it.
QoS classifies and prioritizes traffic throughout your network to improve control and throughput of important data.
QoS lets you:
- Give priority to time-sensitive applications like VoIP and video conferencing
- Change traffic priority from various servers up or down
- Set traffic priority from specific VLANs or applications
- Adapt priorities as business needs evolve
QoS technologies provide specialized handling and resource allocation to specific network traffic flows.
The system looks at packet headers to set priorities and then manages queuing and bandwidth based on preset rules.
QoS proves especially valuable with voice and video applications that can’t handle delays or jitter.
Rather than letting applications compete equally for resources, QoS creates a clear hierarchy that puts business-critical functions first.
Traffic Shaping: Control and Limit
Traffic shaping takes a different approach than QoS by actively controlling how fast data packets move across your network. This technique delays some or all datagrams to match a desired traffic profile.
Traffic shaping stands apart from policing in a key way: it keeps excess packets in a queue to send later, which smooths out the packet flow. Policing simply drops any extra packets.
Traffic shaping brings several key benefits:
- Better performance during busy times
- Lower latency for essential applications
- More usable bandwidth for priority traffic
- Prevention of network congestion
ISPs often use traffic shaping as part of their Internet Traffic Management Practices. They might limit resources used by peer-to-peer file-sharing.
Data centers also use traffic shaping to maintain service agreements when applications share the same network.
Compression: Reduce Data Size
Data compression helps optimize bandwidth by making transmitted data smaller.
The process uses algorithms to encode files efficiently while keeping essential information intact.
Compression offers clear advantages:
- Lower bandwidth use and infrastructure costs
- Faster data transmission with reduced latency
- Better data security during transfer
- Overall network performance boost
Cloud storage and backup solutions benefit greatly from compression since it cuts storage costs and speeds up data transfer.
Organizations save money and sync data faster by compressing it before cloud upload.
Different compression methods suit different needs. Lossless compression keeps all original data – perfect for business documents and text files.
Lossy compression makes files even smaller by removing some non-essential data, which works well for media files.
Caching: Store Frequently Accessed Data
Caching ranks among the most effective bandwidth optimization techniques. It stores frequently accessed data locally to avoid downloading the same things repeatedly.
The goal is quick data retrieval that reduces latency and load times.
Key aspects of caching include:
- Static resources like images and fonts work best for caching
- Dynamic content specific to users usually shouldn’t be cached
- TTL settings control how long content stays in cache
- Higher cache hit ratios show better effectiveness
CDN caching stores website files on proxy servers near visitors. This cuts content delivery time dramatically and creates a better user experience.
High-traffic websites and e-commerce platforms see huge benefits from caching during peak times.
Serving resources from cache helps these sites load pages faster and provide smooth browsing even under heavy load.
These four bandwidth optimization techniques work together to create an efficient network that performs better without increasing costs.
The right utilization tools will help you set up and track these methods effectively.
Bandwidth Utilization Techniques: Infrastructure and Network Design
Physical infrastructure plays a vital role in maximizing your network’s bandwidth utilization beyond software optimization.
The right configuration of these foundational elements creates a backbone that enables efficient data flow across your organization.
Here are three infrastructure techniques that can transform your network’s performance.
Network Segmentation (VLANs): Isolate Traffic
Network segmentation splits your computer network into smaller, manageable segments or subnets.
This strategic division has become a significant security strategy that exceeds performance improvements.
VLANs (Virtual Local Area Networks) let you group devices that don’t share the same physical network switch by creating distinct broadcast domains.
Network segmentation through VLANs offers substantial benefits:
- Reduced congestion: Network traffic broadcasts stay contained in a single segment instead of spreading across the entire network, which reduces congestion during peak hours
- Enhanced security: Network segmentation helps regulate security parameters that make critical data segments harder to breach
- Improved management: Micro-segmentation makes growing IT infrastructure easier by allowing team deployment to each segment
- Better scalability: Segments can expand individually with controlled resource allocation
VLANs work at Layer 2 (data link layer) of the OSI model, while subnets operate at Layer 3 (network layer). This difference matters when designing your segmentation strategy.
Networks that need higher speed and stability benefit from VLANs since endpoints don’t resolve IP addresses for each communication.
Careful planning remains essential for proper implementation. VLANs without appropriate network security controls could make multiple partitions vulnerable to malicious injection.
Load Balancing: Distribute Traffic Evenly
Load balancing spreads network traffic across multiple servers to improve application availability and user experiences.
This approach prevents server overload by routing requests intelligently across available resources.
Load balancing algorithms serve different needs:
- Round Robin: DNS sequentially assigns requests to servers in rotation
- Weighted Round Robin: Servers get different priorities based on capacity
- Least Connection: Servers with fewer active connections get priority
- Response Time: Combines connection count and average server response analysis
Load balancing provides increased fault tolerance by detecting server issues and redirecting traffic automatically.
The system enables smooth maintenance without downtime and offers automatic disaster recovery.
Load balancers come in several types to meet specific needs:
- Network load balancers optimize traffic using IP addresses and protocols
- Application load balancers route traffic based on URLs and HTTP headers
- Virtual load balancers handle traffic across servers, virtual machines, and containers
- Global server load balancers manage traffic between servers in different locations
Upgrading Network Infrastructure: Increase Capacity
Business requirements change and network infrastructure upgrades become necessary. Strategic improvement of your network’s foundation matters more than adding hardware.
Outdated networks create risks to security and business continuity. Research shows that obsolete devices have nearly twice the security vulnerabilities compared to supported solutions.
These devices lack support for automation, SD-WAN technology, and uninterrupted cloud connectivity.
Your infrastructure upgrade should focus on these key elements:
The industry sees a transformation from copper to fiber. Modern technologies need more than what copper cables provide.
Fiber delivers higher speeds, symmetrical connections, and greater capacity across longer distances.
10 Gigabit Ethernet (10 GbE) implementation offers a tenfold increase in speed and performance. This upgrade brings several advantages:
- Supports data-intensive applications and high-performance computing
- Increases network reliability and reduces downtime
- Enhances security through advanced protection features
- Provides room for future growth without frequent upgrades
Vendor-agnostic platforms are a great way to get flexibility during upgrades.
These solutions work with most network solutions, including legacy devices. Network administrators spend less time managing complexity and more time optimizing performance.
These infrastructure techniques combined with software optimization strategies create networks that maximize bandwidth utilization.
Your organization gets the performance, security, and reliability it needs.
Best Practices for Bandwidth Utilization
Network performance can improve dramatically with smart bandwidth optimization strategies. You don’t need expensive upgrades.
These five best practices will help you get the most from your existing resources and keep critical applications running smoothly.
1. Regularly monitor your network traffic
A performance baseline helps detect unusual network behavior. Modern hardware and software tools let you track, profile, and establish baselines for your current network traffic.
This shows how and when bandwidth gets used. Network administrators can predict future bandwidth needs more accurately by analyzing usage patterns across different times and business scenarios.
This forward-thinking approach spots potential network issues quickly, so you can fix problems before they affect business operations.
2. Prioritize critical applications and services
Quality of Service (QoS) policies improve bandwidth use by giving business-critical traffic priority over less important data.
To name just one example, see companies with global branch offices that need reliable bandwidth for VoIP calls.
They can prioritize these calls over file sharing or messaging apps. The next step is setting appropriate policies for time-sensitive and critical resources based on your business needs.
3. Implement traffic shaping to limit bandwidth usage for non-essential applications
Traffic shaping manages network congestion by delaying certain types of network packets while keeping critical applications running smoothly.
This works especially well during peak hours when network usage spikes.
Beyond controlling heavy users, traffic shaping protects networks from traffic surges and prevents attacks from draining resources.
4. Use caching to store frequently accessed data
Network caching keeps often-used files locally, which saves bandwidth and creates smoother connectivity.
This method works best with unchanging data or information that updates rarely, like reference materials or shared static resources that get pricey to build.
You can set up automatic updates through background processes that refresh cached data when needed.
5. Segment your network to isolate traffic
Organizations with many devices face a common issue – broadcast traffic floods all switch ports, leaving insufficient bandwidth for regular traffic.
Network segmentation splits your computer network into smaller sections, which boosts performance and security.
Routers can segment broadcast domains and block unwanted traffic. This saves bandwidth for other users without requiring new infrastructure.
Conclusion
You can’t afford not to maximize your speed anymore; it’s a must in today’s digital world.
The room for error gets smaller as companies depend more on real-time apps, cloud platforms, and infrastructure for remote work.
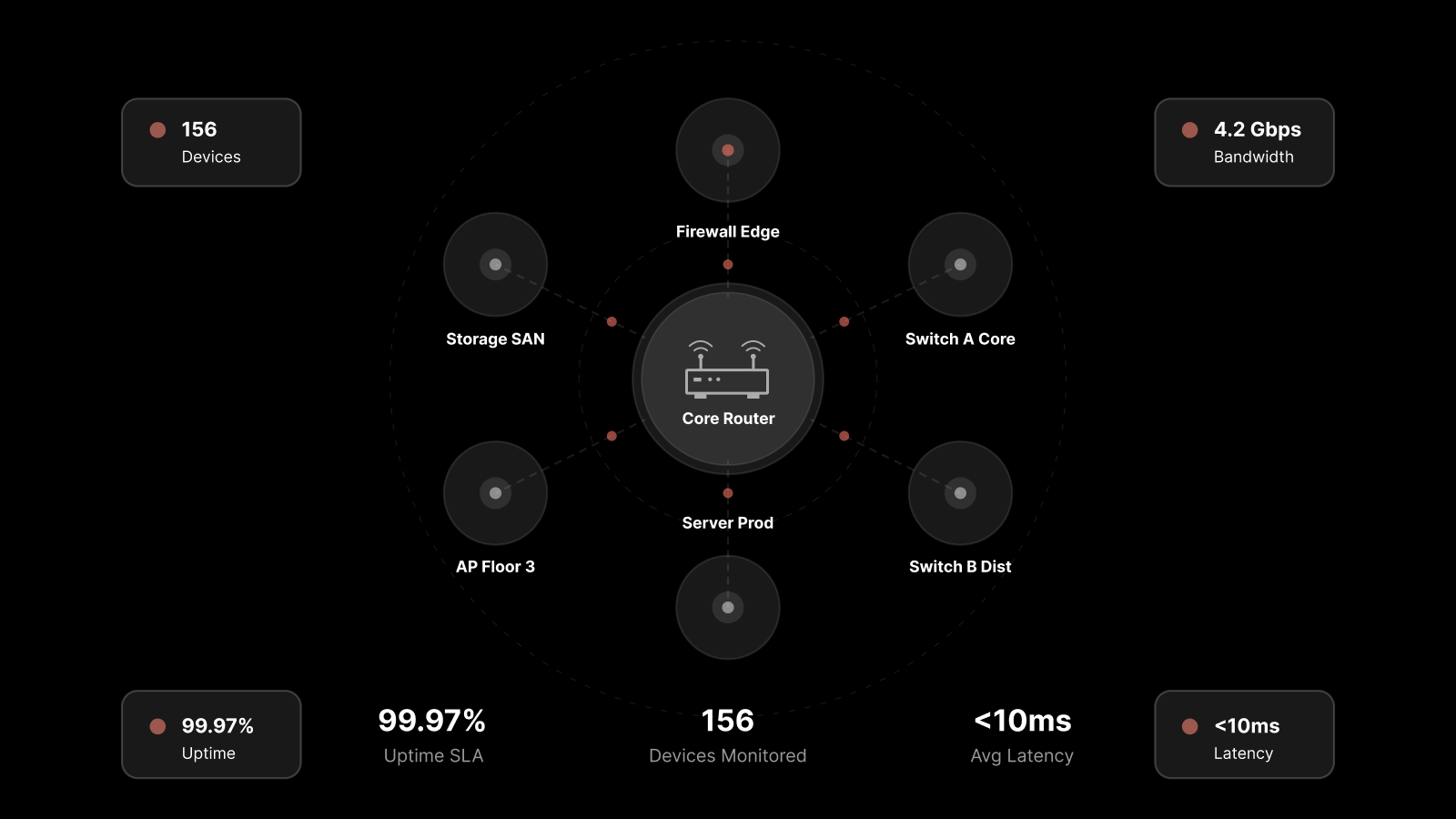
For proactive bandwidth management to start, key performance measures like average and peak usage, utilization percentage, latency, and packet loss must be constantly checked.
Your ability to spot oddities, avoid performance problems, and correctly predict future needs is improved by these insights.
Watching isn’t enough, though. Utilizing tried-and-true optimization methods like Quality of Service (QoS), traffic shaping, data compression, and intelligent caching guarantees that important apps get the performance they need without using up extra resources.
Strengthening your network’s infrastructure with VLAN-based segmentation, smart load balancing, and regular hardware upgrades will keep it flexible, scalable, and resilient.
Utilizing existing bandwidth more efficiently, these methods not only enhance the user experience and boost productivity, but they also save a lot of money by reducing waste.
Optimized bandwidth utilization becomes a strategic asset in a competitive business setting, ensuring performance, security, and scalability for long-term success.
Struggling to monitor bandwidth spikes or identify which applications consume most of your traffic? Motadata Network Observability gives you deep visibility into bandwidth usage, real-time alerts, and AI-powered insights to prevent congestion before it impacts users. Try it now!
FAQs
What are some effective techniques for optimizing bandwidth utilization?
Some effective techniques include implementing Quality of Service (QoS) to prioritize critical traffic, using traffic shaping to control data flow, compressing data to reduce size, and utilizing caching to store frequently accessed information locally.
How can I improve my network’s bandwidth performance?
To improve bandwidth performance, consider using an Ethernet connection instead of Wi-Fi, reducing the number of connected devices, updating your router firmware, and implementing network segmentation to isolate traffic.
What are the key metrics to monitor for bandwidth utilization?
Important metrics to monitor include average bandwidth usage, peak bandwidth usage, bandwidth utilization percentage, latency, and packet loss. These indicators help identify performance bottlenecks and guide optimization efforts.
How does network segmentation contribute to better bandwidth utilization?
Network segmentation divides your network into smaller, manageable parts, which reduces congestion, enhances security, and improves overall performance. It helps contain broadcast traffic within specific segments, saving bandwidth for other users without requiring infrastructure upgrades.
What role does caching play in optimizing bandwidth usage?
Caching stores frequently accessed data locally, reducing the need for repeated downloads and decreasing bandwidth consumption. This technique is particularly effective for static resources like images and fonts, significantly improving load times and overall network performance.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.