Next-Gen SIEM: Why Modern Cybersecurity Demands AI-Powered Threat Detection
Cyberattacks aren't waiting for your security team to finish reviewing yesterday's logs. The average time from initial compromise to data exfiltration has dropped to under 24 hours for many attack types, while the volume of security events most organizations generate has grown into the millions per day. Traditional SIEM tools -- built for a world of manual log review and static correlation rules -- can't keep up. Next-gen SIEM changes the equation by applying AI-driven analytics, automated response, and real-time threat intelligence to the same log data your legacy tools struggle to process.
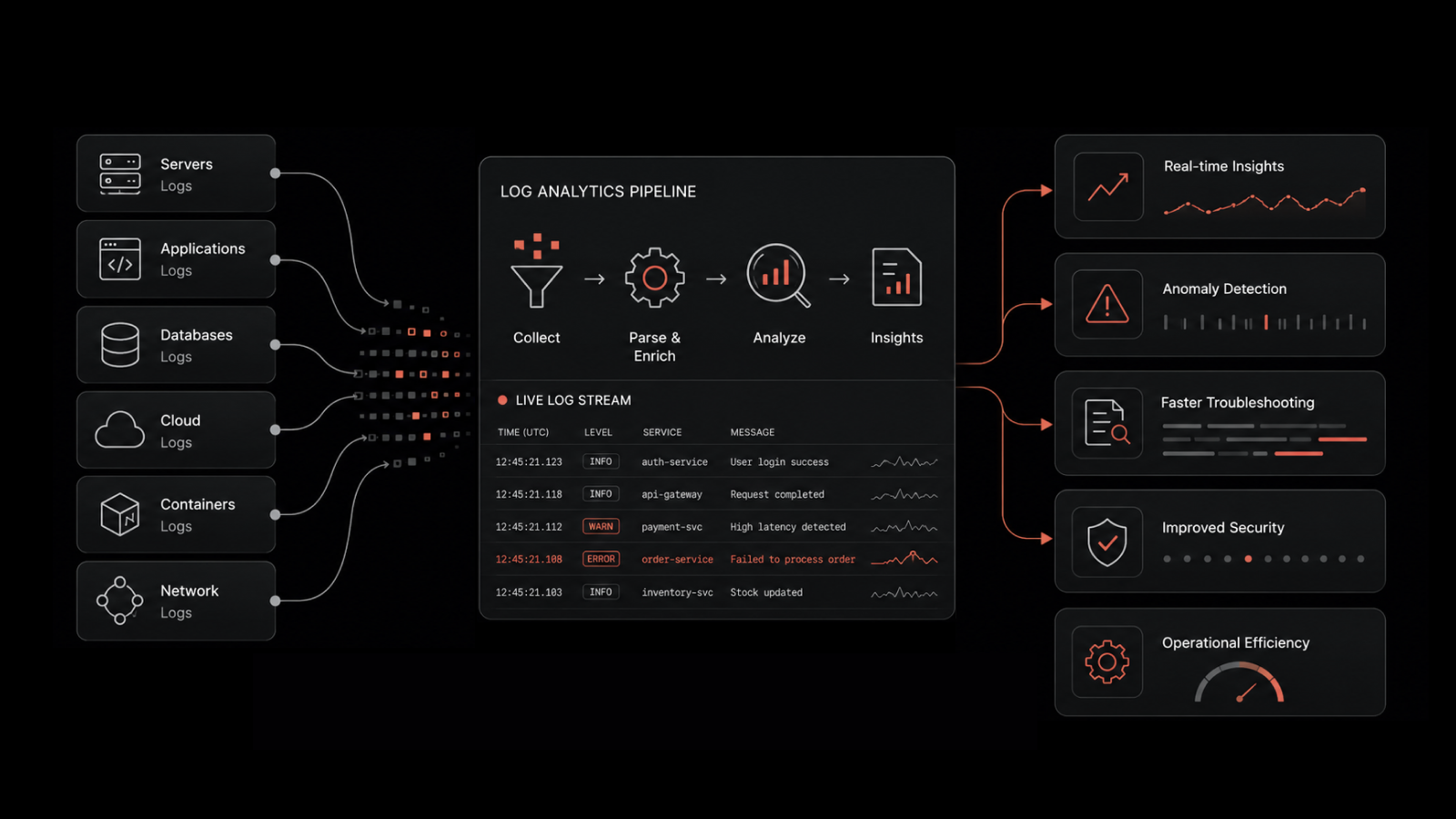
Next-generation SIEM (Security Information and Event Management) is an evolved security platform that combines real-time log aggregation, AI-powered behavioral analytics, automated threat detection, and orchestrated response capabilities. Unlike traditional SIEM, which relies on predefined correlation rules, next-gen SIEM uses machine learning to identify anomalous patterns, reduce false positives, and detect threats that rule-based systems miss entirely.
Why Traditional Security Approaches Fall Short
Antivirus updates, regular patching, and daily backups remain important hygiene practices. But they're reactive by design. Vulnerabilities get exploited before patches are available. Malware penetrates systems before signatures are discovered. Phishing campaigns use social engineering that no firewall can detect.
The numbers tell the story: cybercrime damages are projected to exceed $10.5 trillion annually by 2026, according to industry forecasts. Over 60% of small and mid-sized businesses have experienced a cyberattack in the past 12 months, and the average cost of a data breach now exceeds $4.5 million.
Traditional security tools generate data -- lots of it. Firewalls, intrusion detection systems, endpoint agents, and application logs all produce event streams. The problem isn't data collection. It's making sense of millions of events fast enough to catch threats before they cause damage.
What Makes Next-Gen SIEM Different
The gap between traditional and next-gen SIEM isn't cosmetic. It's architectural.
Capability | Traditional SIEM | Next-Gen SIEM |
|---|---|---|
Detection method | Static correlation rules | AI/ML behavioral analytics + rules |
Alert volume | High (thousands of raw alerts) | Reduced 60-80% through intelligent correlation |
Threat coverage | Known patterns only | Known + unknown (anomaly detection) |
Log processing | Batch or near-real-time | Real-time streaming analytics |
Compliance reporting | Manual report generation | Automated, continuous compliance dashboards |
Response capability | Alert and escalate | Alert + orchestrated automated response |
Scalability | Limited by on-premises hardware | Cloud-native, elastic scaling |
Tuning burden | Heavy (constant rule maintenance) | Self-tuning through ML model adaptation |
AI-Powered Behavioral Analytics
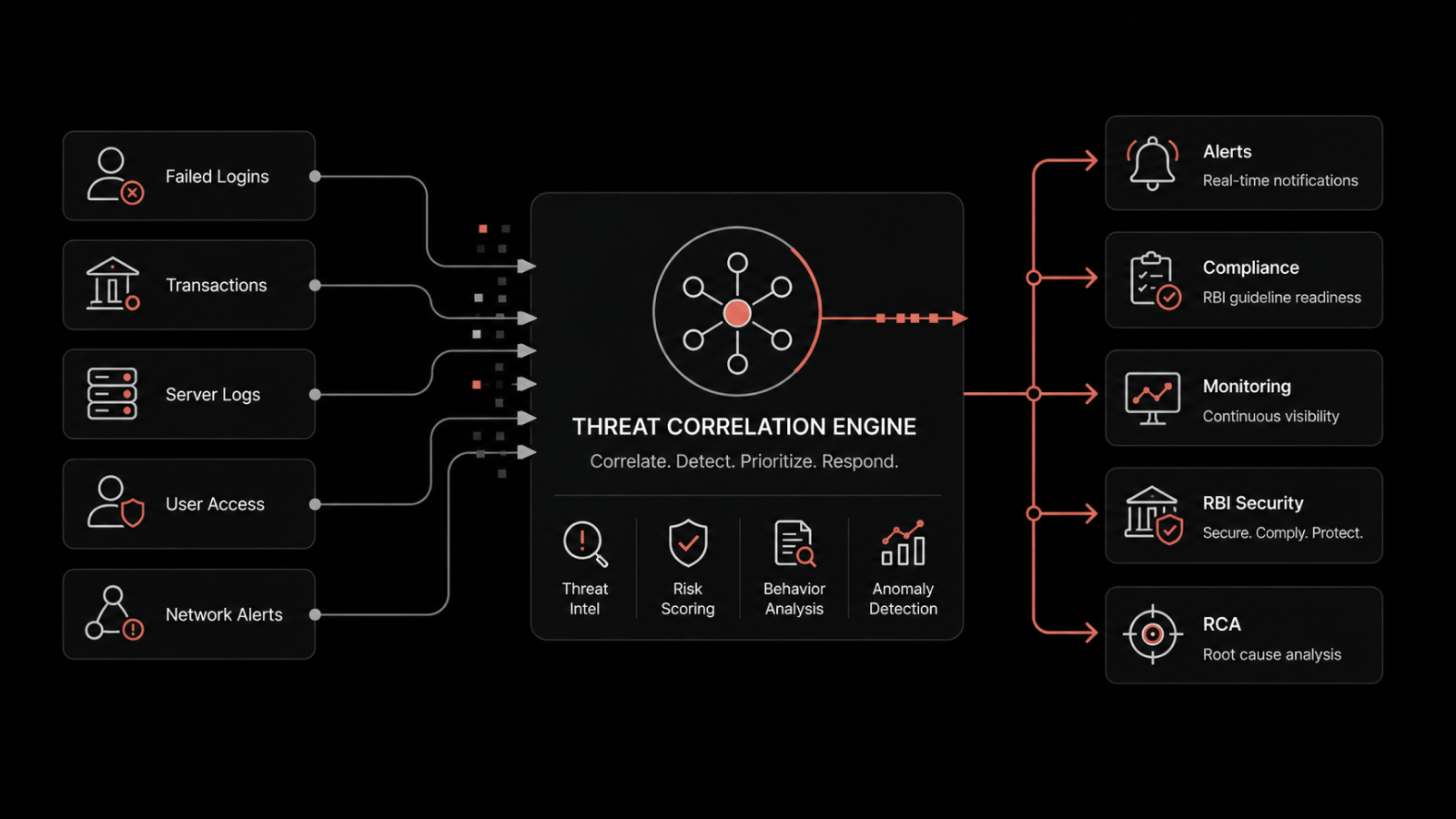
Traditional SIEM triggers alerts when events match predefined rules: "five failed logins from the same IP" or "file access outside business hours." These rules catch known attack patterns but miss everything else.
Next-gen SIEM establishes behavioral baselines for users, devices, and applications. When a user who normally accesses three systems suddenly queries 40 databases at 2 AM, the system flags the anomaly -- even if no rule exists for that specific pattern. This is how insider threats, compromised credentials, and lateral movement get detected before data leaves the network.
Intelligent Alert Correlation and Noise Reduction
Alert fatigue is one of the most dangerous problems in security operations. When analysts receive thousands of alerts daily, real threats get lost in the noise. Studies show that security teams investigate fewer than half of all alerts they receive.
Next-gen SIEM addresses this by correlating related events into unified incidents. Instead of 50 separate alerts for a single attack chain, the platform surfaces one high-confidence incident with full context: affected systems, timeline, user accounts involved, and recommended response actions.
Automated Response Orchestration
Detection without response is just expensive observation. Next-gen SIEM platforms integrate with security orchestration tools to trigger automated responses: isolating compromised endpoints, blocking malicious IPs, disabling compromised accounts, and initiating forensic data collection -- all within seconds of detection.
Core Benefits of Next-Gen SIEM
Comprehensive Threat Visibility
Next-gen SIEM aggregates and normalizes log data from every source in your environment: firewalls, endpoints, cloud platforms, applications, identity providers, email gateways, and network devices. This unified view eliminates the blind spots that attackers exploit when security tools operate in silos.
Faster Threat Detection and Response
By applying real-time analytics to streaming event data, next-gen SIEM reduces mean time to detect (MTTD) from days or weeks to minutes. Combined with automated response orchestration, mean time to respond (MTTR) drops proportionally -- containing threats before they escalate.
Simplified Compliance
Regulatory frameworks like SOC 2, GDPR, HIPAA, and PCI DSS require organizations to demonstrate continuous security monitoring, access control enforcement, and incident response capabilities. Next-gen SIEM platforms automate compliance evidence collection and generate audit-ready reports on demand -- turning what used to be a quarterly scramble into a continuous, automated process.
Reduced Operational Burden
Traditional SIEM platforms are notorious for requiring dedicated analysts just to maintain correlation rules, tune thresholds, and manage storage. Next-gen SIEM platforms with ML-based detection reduce this burden by self-tuning, automatically adapting to environmental changes, and escalating only the alerts that warrant human attention.
Where Next-Gen SIEM Fits in Your Security Stack
A SIEM isn't a standalone solution. It's a force multiplier that makes every other security tool more effective. Here's how it fits:
Threat intelligence integration - Next-gen SIEM ingests threat feeds and correlates them against your environment's activity. When a newly identified malicious IP appears in your firewall logs, the SIEM flags the connection immediately.
Endpoint detection and response (EDR) - SIEM correlates endpoint alerts with network and application events, providing the broader context that EDR tools alone can't deliver.
Patch management - SIEM identifies which unpatched systems are being actively targeted, helping security teams prioritize patching based on real threat exposure rather than CVSS scores alone.
Identity and access management (IAM) - SIEM monitors authentication patterns, privilege usage, and access anomalies across all identity providers, catching credential compromise that IAM tools might miss.
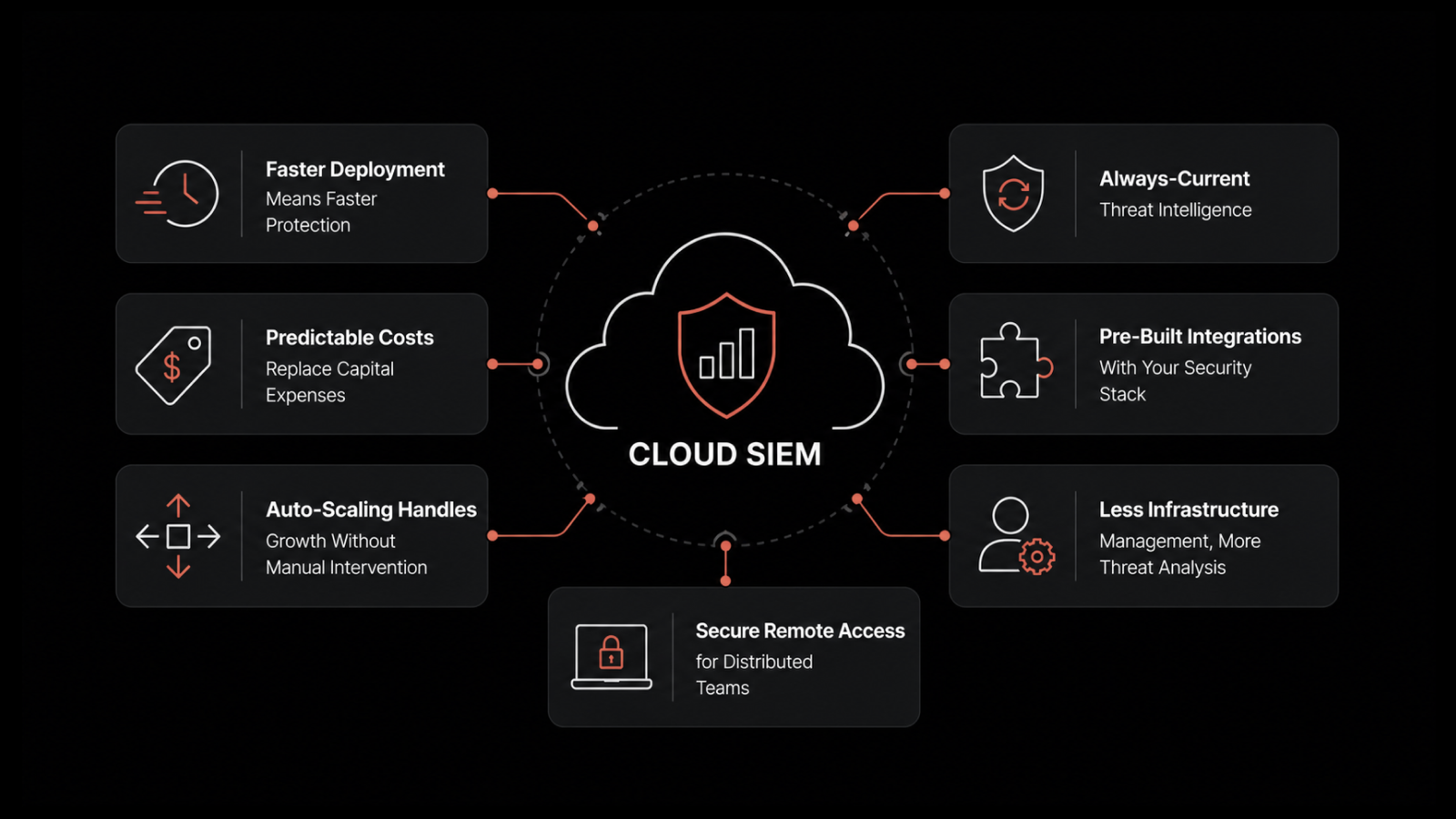
Cloud security - As organizations expand across AWS, Azure, and GCP, next-gen SIEM normalizes cloud-native logs alongside on-premises data, maintaining unified visibility across hybrid environments.
Choosing the Right Next-Gen SIEM
Not all SIEM platforms deliver on the "next-gen" promise. Here's what to evaluate:
Detection fidelity -- Does the platform use genuine ML-based anomaly detection, or is it traditional rules with an "AI" label?
Time to value -- How quickly can you onboard log sources and begin detecting threats? Months-long deployments defeat the purpose.
Alert quality -- Ask for alert-to-incident ratios. High-quality platforms produce fewer, higher-confidence alerts.
Compliance coverage -- Verify built-in support for your specific regulatory requirements.
Scalability -- Can the platform handle your current log volume and projected growth without performance degradation?
Integration depth -- Evaluate native integrations with your existing security tools, cloud providers, and identity systems.
Why Motadata's AI-Native Platform Delivers
Motadata's log analytics and SIEM capabilities are built on an AI-native architecture that processes and analyzes security events at scale. Here's what your security team gets:
Real-time log aggregation from on-premises, cloud, and hybrid sources with automated parsing and normalization
AI-powered anomaly detection that identifies threats static rules miss -- including insider threats and zero-day patterns
Intelligent alert correlation that reduces noise by 60-80% and surfaces actionable, contextualized incidents
Automated compliance reporting for SOC 2, GDPR, HIPAA, PCI DSS, and custom frameworks
Integrated threat intelligence with real-time correlation against global threat feeds
Scalable architecture that grows with your log volume without performance trade-offs
Start a free trial to see how Motadata's AI-native SIEM capabilities transform your security operations. Or schedule a demo to explore how unified log analytics and threat detection protect your organization.
FAQs
What is the difference between traditional SIEM and next-gen SIEM?
Traditional SIEM relies on predefined correlation rules to match known attack patterns, generating high alert volumes with significant false positives. Next-gen SIEM adds AI-powered behavioral analytics that detect unknown threats by identifying anomalous patterns, reduces alert noise through intelligent correlation, and integrates automated response capabilities. The result is faster detection, fewer false positives, and reduced operational burden.
How does AI improve SIEM threat detection?
AI improves SIEM by establishing behavioral baselines for users, devices, and applications, then detecting deviations from those baselines. This catches threats that static rules miss -- including insider threats, compromised credentials, lateral movement, and zero-day exploits. ML models also reduce false positives by learning which alerts represent genuine threats versus benign anomalies.
Is SIEM necessary for compliance?
While not always explicitly required, SIEM capabilities directly support compliance requirements across major frameworks. SOC 2, GDPR, HIPAA, and PCI DSS all require continuous monitoring, audit trails, access logging, and incident detection -- all core SIEM functions. Modern SIEM platforms automate compliance evidence collection and reporting, making audits significantly less burdensome.
How much does a next-gen SIEM cost?
SIEM pricing varies based on log volume (measured in events per second or gigabytes per day), number of log sources, retention requirements, and feature set. Cloud-native platforms like Motadata offer scalable pricing that grows with your needs. The real cost question is the total cost of ownership -- including staff time for rule maintenance and alert investigation, where next-gen platforms significantly reduce ongoing operational expenses.
Can a small business use SIEM effectively?
Yes. Next-gen SIEM platforms are more accessible than their predecessors. Cloud-based deployment eliminates hardware requirements, ML-based detection reduces the need for dedicated rule-writing expertise, and automated response handles routine threats without requiring a 24/7 SOC. Small businesses with regulatory obligations or valuable data assets benefit particularly from SIEM's automated compliance and threat detection capabilities.