Network Automation and Infrastructure Monitoring: A Complete Guide
Modern IT networks don't fail gracefully. One misconfigured router or an overlooked firmware update can cascade into hours of downtime — costing enterprises an average of $9,000 per minute according to recent industry estimates. That's why network automation and infrastructure monitoring aren't optional anymore. They're the foundation of every resilient IT operation.
This guide breaks down what network automation and infrastructure monitoring actually involve, why they matter, and how you can implement both to build a faster, more reliable, and more secure network.
Network automation is the practice of using software to automatically configure, manage, test, and operate network devices and services — eliminating manual, repetitive tasks. Infrastructure monitoring is the continuous process of observing, collecting, and analyzing data from IT systems (routers, servers, switches, firewalls) to ensure optimal performance, health, and security.
How Network Automation and Infrastructure Monitoring Work Together
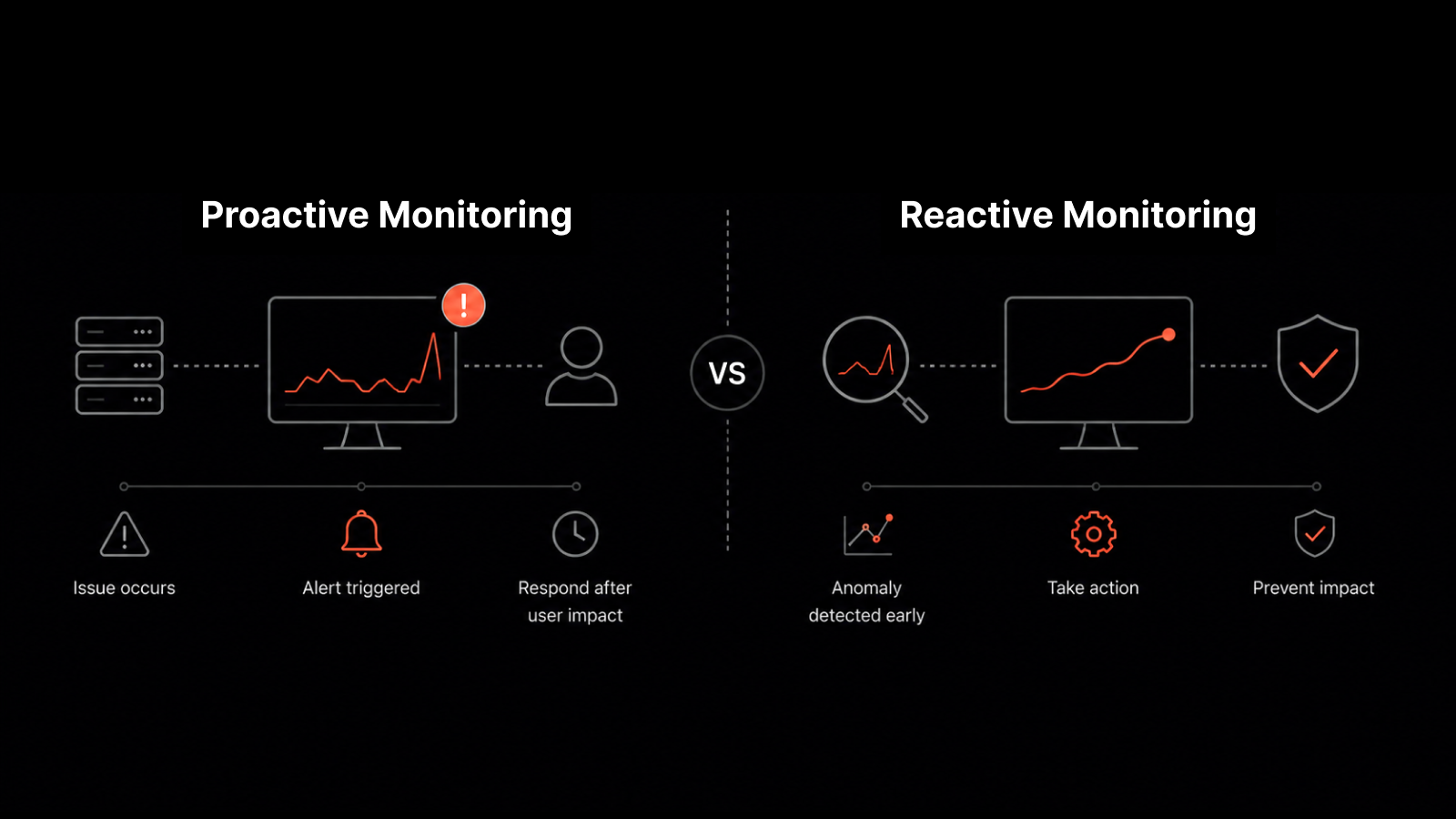
Network automation and infrastructure monitoring serve different but deeply complementary functions. Monitoring tells you what's happening across your network. Automation lets you act on that intelligence without waiting for a human to intervene.
Here's how they connect: infrastructure monitoring collects data from routers, servers, firewalls, switches, and wireless access points. It analyzes that data to detect anomalies, performance degradation, or security threats. When monitoring detects an issue, automation can trigger predefined responses — rerouting traffic, restarting services, or alerting the right team — in milliseconds rather than minutes.
This combination shifts IT teams from reactive firefighting to proactive management. Instead of scrambling after an outage, you're preventing one.
Why Network Automation Matters for Modern IT Teams
Managing a modern network manually is like trying to direct traffic at a hundred intersections simultaneously. It doesn't scale.
Network automation matters because it addresses three fundamental challenges:
Speed. Manual configuration changes take time. Automation executes provisioning, policy enforcement, and device configuration in seconds — not hours.
Accuracy. Human error accounts for a significant percentage of network outages. Automated workflows follow the same process every time, eliminating fat-finger mistakes and inconsistent configurations.
Scale. As your network grows — more offices, more cloud environments, more edge devices — automation ensures your team can manage it all without proportionally growing headcount.
IT teams that embrace automation free themselves to focus on strategic work: architecture planning, security improvements, and innovation projects that actually move the business forward.
Core Challenges in Infrastructure Monitoring and Automation
Implementing monitoring and automation isn't without hurdles. Here are the real challenges IT teams face — and how to address them:
Multi-Cloud and Multi-Vendor Complexity
Most enterprises operate across multiple cloud providers, on-premise data centers, and vendor ecosystems. Each comes with its own management interface, APIs, and monitoring protocols. The challenge is finding a monitoring platform that provides a unified view across all of them — without forcing you to toggle between six different dashboards.
Security Risks in Automation
Automation tools interact with critical network infrastructure. If they're not properly secured, they can become attack vectors. Improper access controls, unencrypted automation scripts, or unauthorized change management can introduce vulnerabilities. Mitigation requires strong access controls, encryption, regular security audits, and thorough employee training on automation tool usage.
Legacy System Integration
Not every device in your network was built for modern automation. Legacy systems often lack API support or compatibility with current automation frameworks. The solution isn't a rip-and-replace approach — it's a phased migration strategy that gradually brings legacy systems under automated management while maintaining operational stability.
Organizational Buy-In
Getting leadership to approve automation and monitoring investments requires speaking their language. That means framing proposals around business outcomes — reduced downtime costs, faster incident resolution, and improved compliance — rather than technical specifications.
Benefits of Network Automation
Automation delivers measurable improvements across four key areas:
Agile, scalable networks. Automation streamlines policy enforcement, device provisioning, and resource allocation. As your network grows, automation scales with it — no additional manual overhead required.
Faster, more accurate provisioning. Automated provisioning eliminates the delays and inconsistencies of manual configuration. New devices and services come online faster, with configurations that match your standards every time.
Fewer configuration errors. Manual tasks introduce human error. Automation executes the same process consistently, reducing misconfigurations that lead to outages and security gaps.
Improved operational efficiency. When your team isn't spending hours on repetitive configuration tasks, they're free to focus on higher-value work — troubleshooting complex issues, optimizing architecture, and driving innovation.
Benefits of Infrastructure Monitoring
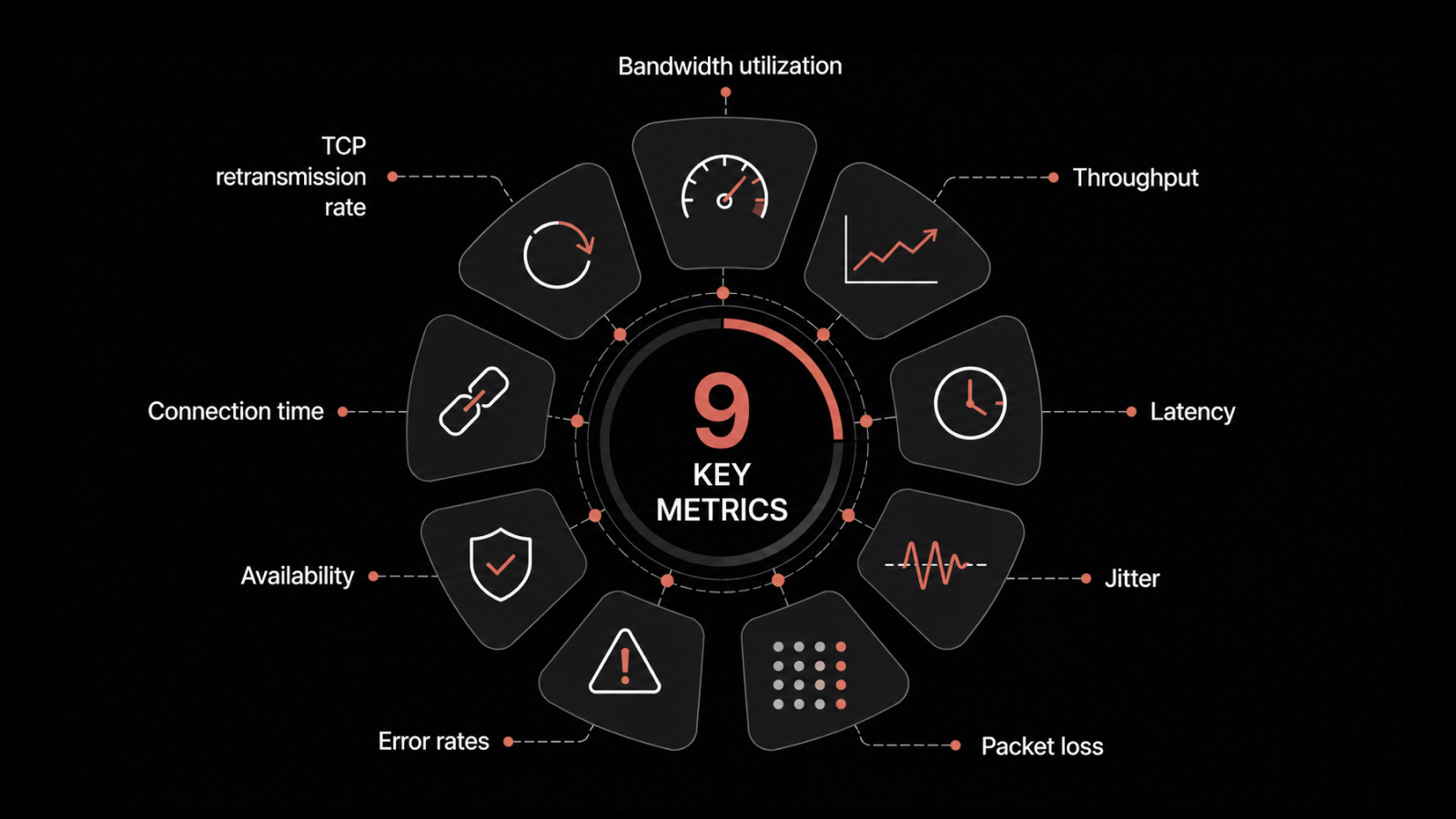
Monitoring provides the visibility that keeps your network healthy:
Proactive threat detection. Monitoring systems detect suspicious activity patterns, unauthorized access attempts, and anomalous traffic flows — alerting your security team before an attack succeeds.
Real-time issue resolution. Instead of discovering problems after users complain, monitoring surfaces issues as they emerge. Your team can respond immediately, often resolving problems before anyone notices.
Stronger business continuity. Network interruptions halt business operations. Monitoring identifies potential disruptions early, allowing your team to address root causes before they affect productivity.
Cloud resource optimization. Monitoring tracks cloud resource utilization in real time, helping you right-size instances, eliminate waste, and reduce cloud spending without sacrificing performance.
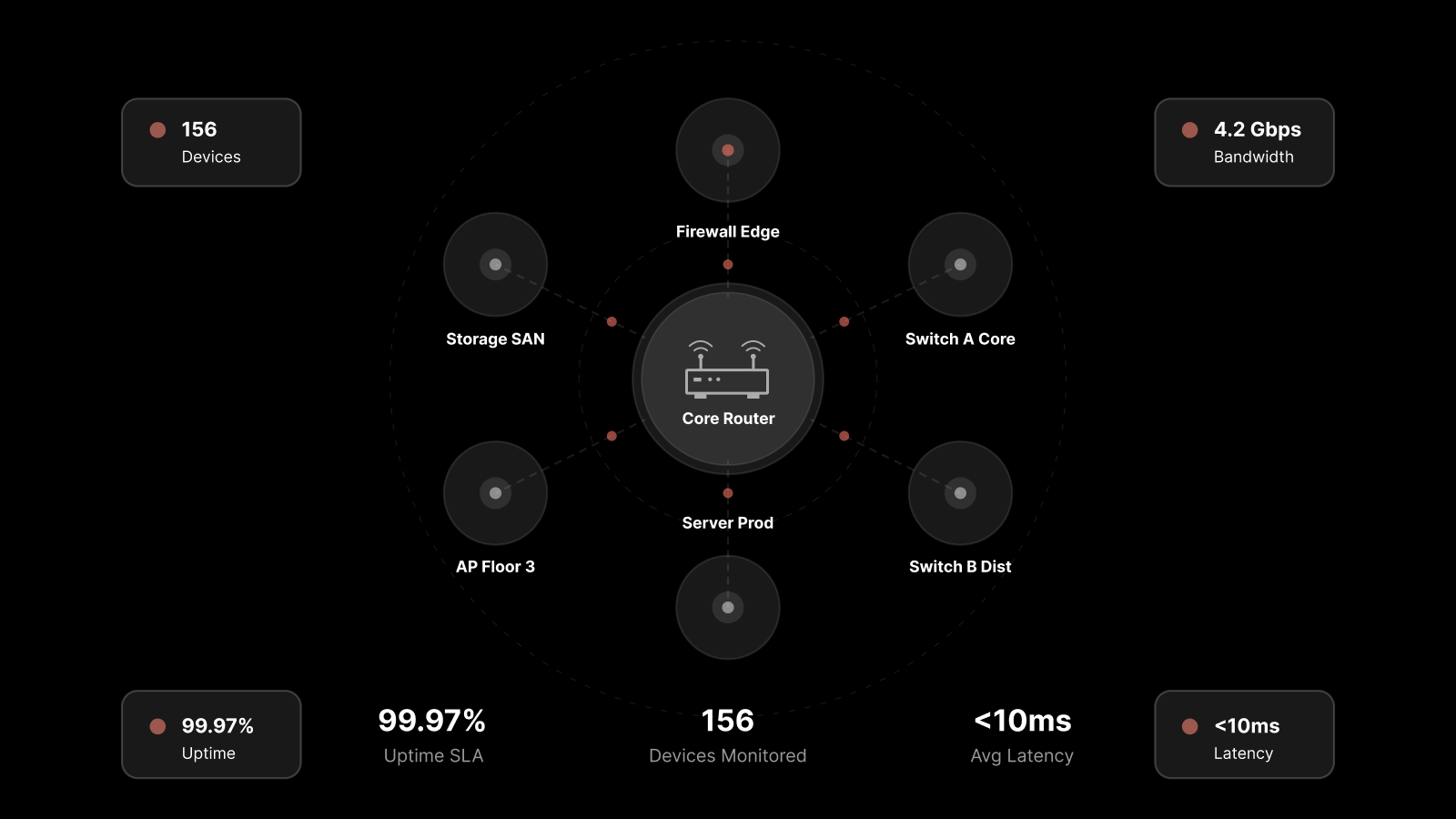
How Infrastructure Monitoring Works: The Four-Stage Process
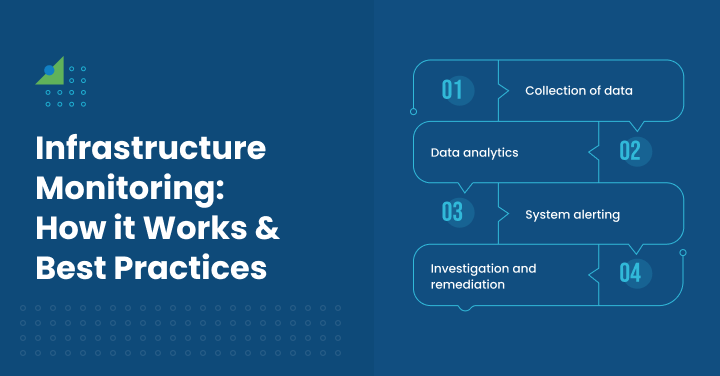
Infrastructure monitoring follows a consistent four-stage workflow:
Data collection. Agents or agentless protocols (SNMP, WMI, SSH) gather performance data from servers, network devices, applications, databases, and hypervisors across your environment.
Data analysis. Collected data is processed using statistical analysis, machine learning algorithms, and pattern recognition to identify anomalies, trends, and potential issues.
Alerting. When analysis detects a threshold breach or anomaly, the system generates alerts and routes them to the appropriate team via email, Slack, SMS, or integrated ticketing systems.
Investigation and remediation. Your team investigates the alert, determines root cause, and resolves the issue — or, with automation in place, the system remediates automatically.
Agent-Based vs. Agentless Monitoring
You'll encounter two monitoring approaches: agentless monitoring uses remote protocols (SNMP, WMI, SSH) to collect data without installing software on target systems. Agent-based monitoring deploys lightweight software agents on each monitored system for deeper visibility and more granular data collection. Most mature environments use a hybrid approach.
Key Components of a Network Automation Stack
Building an effective automation practice requires the right components:
Software-Defined Networking (SDN): Separates network control functions from physical hardware, enabling centralized, programmable management of your entire network fabric.
Orchestration Platforms: Centralize workflow management, policy enforcement, and task automation across your network — ensuring consistency at scale.
Network Configuration Management (NCM): Automates device configuration, software upgrades, and policy enforcement for switches, firewalls, and routers.
Network Virtualization: Abstracts physical network resources into virtual segments, enabling dynamic provisioning and faster deployment.
AI-Driven Analytics: Modern automation platforms use machine learning to predict failures, optimize performance, and trigger automated remediation before issues affect users.
Conclusion
As network systems and data grow and become increasingly complex, having an IT infrastructure that runs optimally is essential.
Combining network monitoring and automation tools into your processes can vastly improve your company’s ability to stay ahead of costly problems like downtime and security breaches.
No matter the size of your company, automation and monitoring should be the focus and foundation of your IT strategy.
FAQs
What is network automation?
Network automation uses software to configure, manage, and operate network devices without manual intervention. It covers tasks like device provisioning, policy enforcement, configuration management, and software upgrades.
Why is infrastructure monitoring important?
Infrastructure monitoring provides continuous visibility into network health, performance, and security. Without it, issues go undetected until they cause outages, security breaches, or performance degradation that affects users and revenue.
What tools do I need for network automation?
A comprehensive automation stack includes SDN controllers, orchestration platforms, network configuration management tools, and AI-driven analytics. Platforms like Motadata combine these capabilities into a unified, AI-native solution.
How do automation and monitoring reduce downtime?
Monitoring detects issues in real time. Automation executes predefined responses instantly — rerouting traffic, restarting services, or escalating alerts. Together, they shrink mean time to resolution from hours to minutes or seconds.
What's the ROI of network automation?
Organizations implementing network automation typically see 60-80% reduction in manual configuration time, 50%+ fewer configuration-related incidents, and significant improvements in mean time to resolution.
Build a Self-Healing Network with Motadata
Motadata's AI-native platform unifies network automation and infrastructure monitoring in a single solution. With intelligent discovery, real-time performance analytics, and automated remediation workflows, Motadata helps IT teams eliminate manual overhead, prevent outages, and scale their networks confidently.
Whether you're managing a hybrid cloud environment, a distributed enterprise network, or a complex multi-vendor infrastructure, Motadata gives you the visibility and automation you need — without the tool sprawl.
Start your free trial or schedule a demo to see how Motadata transforms network operations.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.