Enhancing IT Security with Log Data: A Practical Guide to Log-Driven Threat Detection
Security log management is the practice of collecting, centralizing, analyzing, and retaining log data from IT systems — including servers, network devices, applications, and security appliances — to detect threats, investigate incidents, and maintain regulatory compliance.
The Breach Was Happening for 207 Days. Nobody Noticed.
According to the 2025 IBM Cost of a Data Breach Report, the average time to identify a security breach is 207 days. That's nearly seven months of unauthorized access before anyone detects the intrusion. And the cost? An average of $4.88 million per breach.
Here's what makes that statistic especially frustrating: in almost every case, the evidence of the breach existed in the organization's log data. Failed authentication attempts. Unusual access patterns. Privilege escalations at odd hours. Configuration changes that nobody authorized. The signals were there. They just weren't being watched.
Log data is the most underutilized security resource in most organizations. Every system generates it. Few organizations analyze it effectively. And the gap between generating logs and acting on them is where breaches live.
What Is Security Log Data?
Every device, application, and service in your IT environment generates log entries. These entries record events — who did what, when, where, and what happened as a result. In a security context, log data includes:
Authentication logs — successful and failed login attempts, password changes, account lockouts
Authorization logs — access grants, privilege escalations, permission modifications
Network logs — connection attempts, firewall events, DNS queries, traffic flows
System logs — service starts and stops, configuration changes, error conditions
Application logs — user actions, API calls, transaction records, error messages
Security appliance logs — IDS/IPS alerts, antivirus detections, endpoint protection events
Individually, each log entry is a data point. Collectively, they tell the story of what's happening across your infrastructure — and they're often the first place that evidence of a security incident appears.
Why Log Data Matters for IT Security
Log data serves three fundamental security functions:
Threat Detection
Logs capture the footprints that attackers leave as they move through your environment. Brute-force login attempts, lateral movement between systems, data exfiltration patterns, and privilege escalation sequences all generate log entries. Effective log monitoring catches these patterns before they result in a full breach.
Incident Investigation
When a security incident occurs, log data is the primary source of forensic evidence. It answers the critical questions:
When did the breach begin?
Which systems were compromised?
What data was accessed or exfiltrated?
How did the attacker gain initial access?
What actions did they take after gaining entry?
Without centralized, time-stamped log data, incident response teams are working in the dark.
Compliance and Audit Readiness
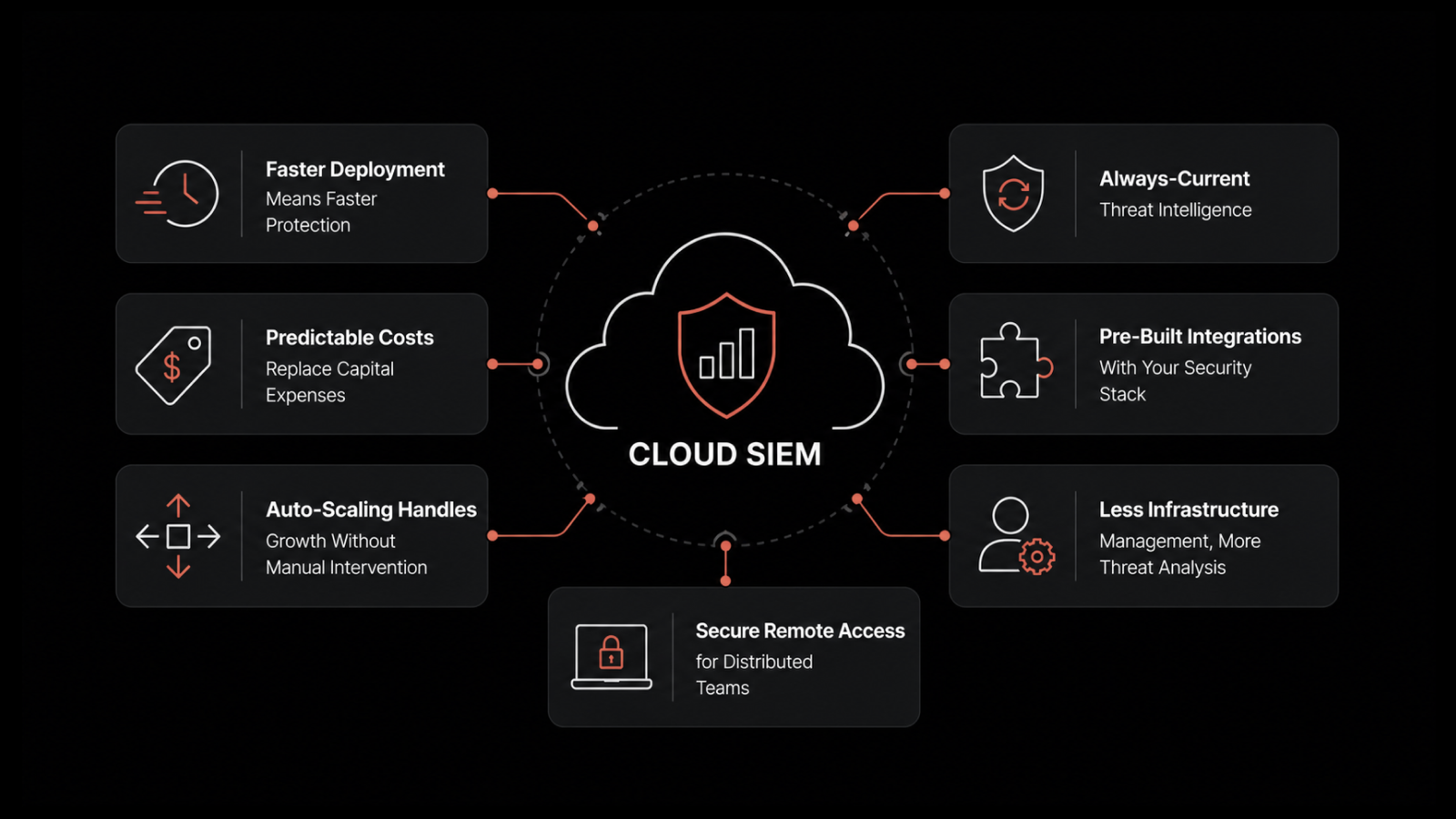
Regulatory frameworks mandate log retention and monitoring. SIEM (Security Information and Event Management) capabilities help organizations meet requirements under:
PCI-DSS — requires logging and monitoring of all access to network resources and cardholder data
HIPAA — mandates audit controls that record and examine access to electronic protected health information
SOC 2 — requires logging, monitoring, and alerting for security-relevant events
GDPR — requires organizations to detect and report data breaches within 72 hours
Meeting these requirements isn't optional — and manual log review doesn't scale.
The Challenge of Scale and Complexity
The volume of log data in modern IT environments is staggering. A mid-sized organization generates millions of log entries per day across servers, network devices, cloud services, applications, and security tools. Large enterprises produce billions.
This scale creates three core challenges:
Volume and Noise
When you're processing millions of events per hour, finding the meaningful signals requires automated filtering and correlation. The vast majority of log entries represent normal operations. The security-relevant events — a handful out of millions — need to be surfaced automatically, not discovered through manual search.
Timing and Freshness
Security log data loses value rapidly. A log entry that indicates an active intrusion is actionable right now. The same entry discovered a week later is forensic evidence. Real-time log processing is the difference between preventing damage and documenting it.
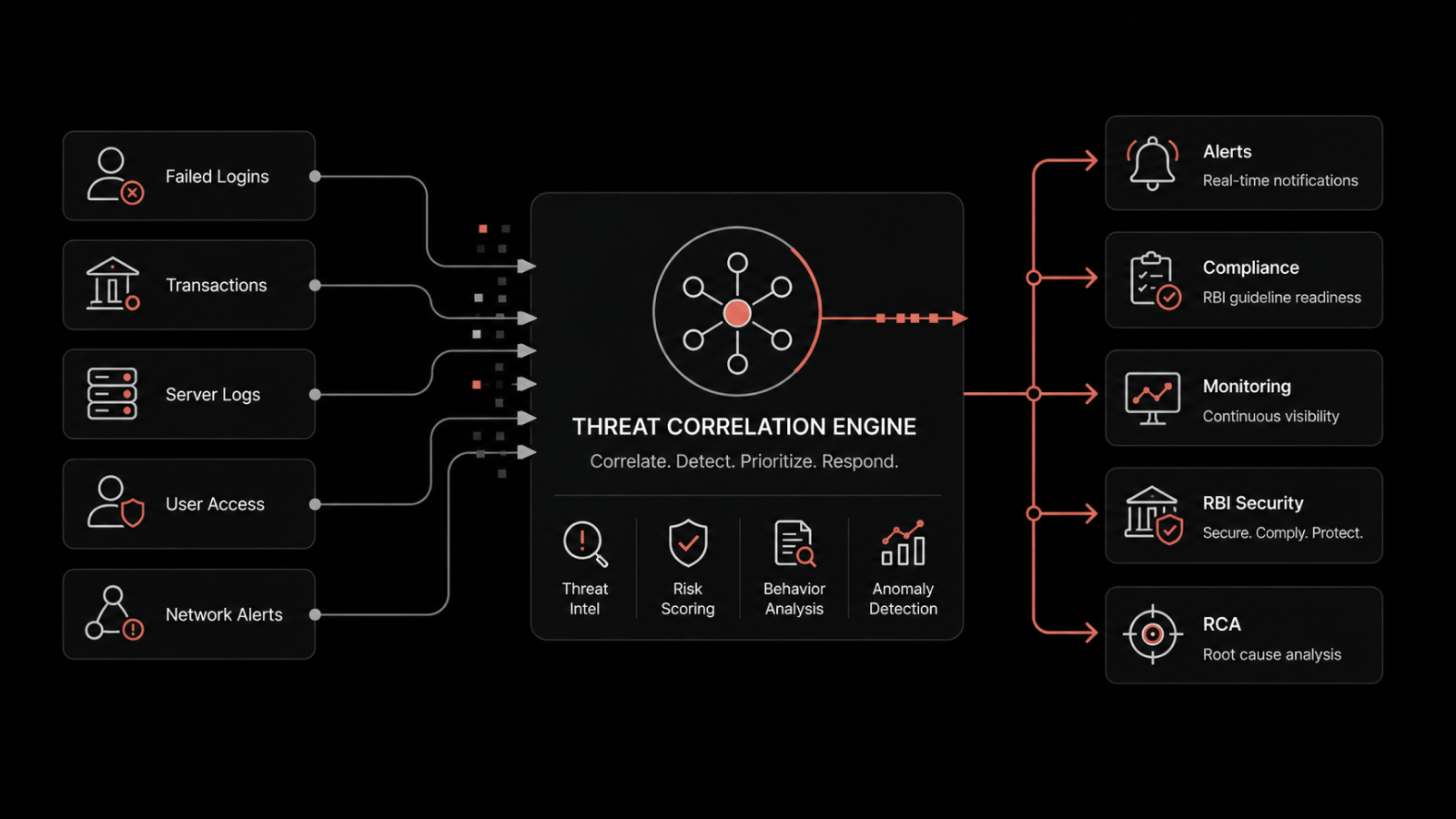
Correlation Across Sources
Individual log entries from isolated systems rarely tell the complete story. A failed login attempt on its own isn't alarming. But a failed login attempt followed by a successful login from a different IP, followed by a privilege escalation and a large data transfer — that's an attack chain. Detecting it requires correlating events across multiple systems in near real time.
How AI-Driven Log Analysis Transforms Security
Traditional log management relies on predefined rules and manual queries. Security teams write rules to catch known attack patterns, then review alerts manually. This approach catches known threats but misses novel attacks and generates high volumes of false positives.
AI-driven log analysis changes the equation:
Behavioral baseline learning — AI models learn what normal looks like for each user, system, and network segment. Deviations from these baselines trigger alerts automatically, catching threats that rule-based systems miss.
Automated correlation — AI connects related events across systems and time periods, identifying attack chains that would take human analysts hours to piece together.
Anomaly scoring — instead of binary alert/no-alert decisions, AI assigns risk scores to events based on context. This helps security teams prioritize their response to the highest-risk items first.
Adaptive detection — AI models update continuously as new data arrives, improving detection accuracy over time without requiring manual rule updates.
The result is faster detection, fewer false positives, and security teams that spend their time investigating real threats instead of chasing noise.
Building an Effective Log Security Strategy
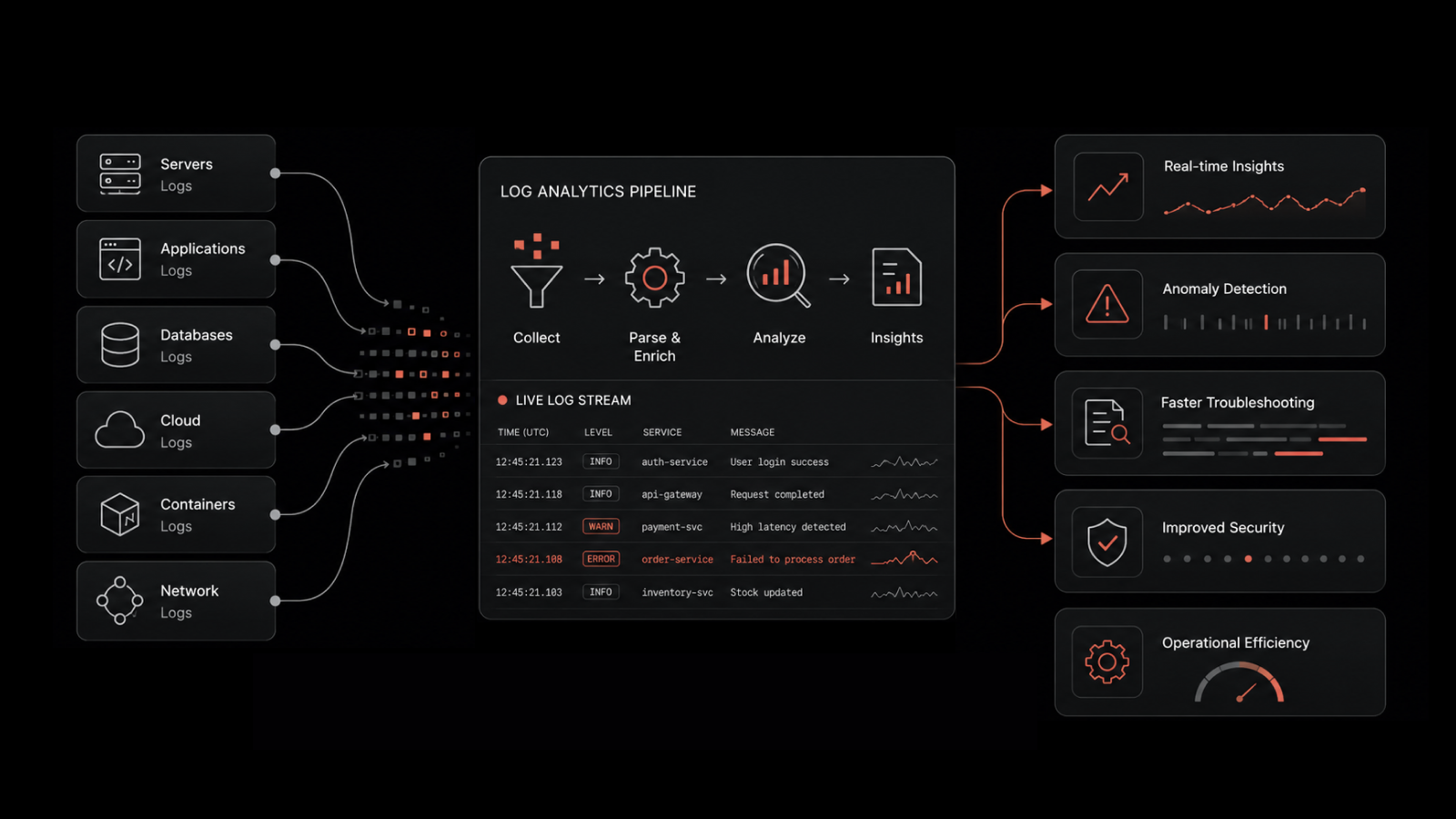
Step 1: Centralize Log Collection
Collect logs from every source — servers, network devices, cloud platforms, applications, security appliances, and endpoints — into a single log management platform. Centralization eliminates blind spots and provides the unified dataset that correlation and analysis require.
Step 2: Normalize and Enrich
Raw logs from different sources use different formats, timestamps, and field structures. Normalize them into a consistent format and enrich them with contextual data — asset ownership, geographic location, user role — to make correlation faster and more accurate.
Step 3: Implement Real-Time Monitoring
Configure real-time dashboards and alerts for security-relevant events. Focus initial monitoring on high-value targets: authentication systems, privileged accounts, network perimeters, and data repositories.
Step 4: Enable AI-Driven Analysis
Deploy AI-driven analytics to establish behavioral baselines, detect anomalies, and automate event correlation. This extends detection capability beyond what rule-based systems can achieve.
Step 5: Integrate with ITSM and Incident Response
Connect log management with your IT service management and incident response workflows. When a security event is detected, automated workflows should create incidents, notify responders, and initiate containment procedures without manual intervention.
Step 6: Establish Retention and Compliance Policies
Define log retention periods based on regulatory requirements and business needs. Automate retention management to ensure compliance without manual effort.
Strengthen Your Security with Motadata Log Management
Motadata's Log Analyzer provides centralized log collection, AI-driven analysis, and real-time monitoring across your entire IT infrastructure. It transforms raw log data into actionable security intelligence — helping your team detect threats faster, investigate incidents more effectively, and maintain compliance with confidence.
With Motadata, security teams get:
Centralized log collection from servers, network devices, cloud platforms, and applications
AI-driven anomaly detection that establishes behavioral baselines and flags deviations automatically
Real-time dashboards and alerts for security-relevant events across the entire environment
Compliance-ready retention with automated policies for PCI-DSS, HIPAA, SOC 2, and more
Seamless ITSM integration that connects security events to incident response workflows
Don't let threats hide in your log data. Start a free trial of Motadata and turn your logs into your strongest security advantage.
FAQs
What types of log data are most important for security?
Authentication logs, authorization and access control logs, network traffic logs, firewall and IDS/IPS logs, and system configuration change logs are the most security-relevant. These capture the events most likely to indicate unauthorized access, privilege escalation, or data exfiltration.
How does AI improve log-based threat detection?
AI learns baseline behavior patterns for users, systems, and network segments, then flags deviations automatically. It correlates events across sources to identify attack chains, assigns risk scores to prioritize response, and adapts continuously to new patterns — catching threats that static rules miss.
Why is centralized log management better than distributed logging?
Centralized logging eliminates blind spots by bringing all event data into a single platform. It enables cross-system correlation, simplifies search and investigation, ensures consistent retention policies, and provides the unified dataset that AI-driven analysis requires to be effective.
What compliance standards require log monitoring?
PCI-DSS, HIPAA, SOC 2, GDPR, FISMA, and GLBA all include requirements for log collection, monitoring, and retention. Most frameworks mandate that organizations detect and respond to security events promptly — which requires active log monitoring, not just storage.
How does Motadata support security log management?
Motadata provides centralized log collection from all infrastructure sources, AI-driven anomaly detection, real-time monitoring dashboards, automated compliance retention, and integration with ITSM workflows. It helps security teams detect threats faster, investigate incidents more effectively, and maintain regulatory compliance.