Engineer Intelligent Alerting for Efficient Network Monitoring
Amartya Gupta
Imagine a scenario where your Network Monitoring team has a group of very talented, organized, and focused technicians. Close to half of them are engaged in monitoring the system almost throughout the day.
They can take care of the issues and problems as soon as they arise, and you are never facing any downtime. This is an ideal case scenario, right?
The answer is a resounding ‘No.’ By having your Network Monitoring Technicians monitor the system all day long, you lose out on the person-hours and their skills, which could have been leveraged to produce more value.
These are some of the most technically apt people in your firm, and you use them only for problem resolution.
The reason why constant manual monitoring done by technicians is an inefficient use of resources is because a significant degree of issues coming in the network are statistically common and can be mitigated using simple mechanisms.
Alerts play a critical role in ensuring that your skilled technicians are attending issues only when it is the only option available.
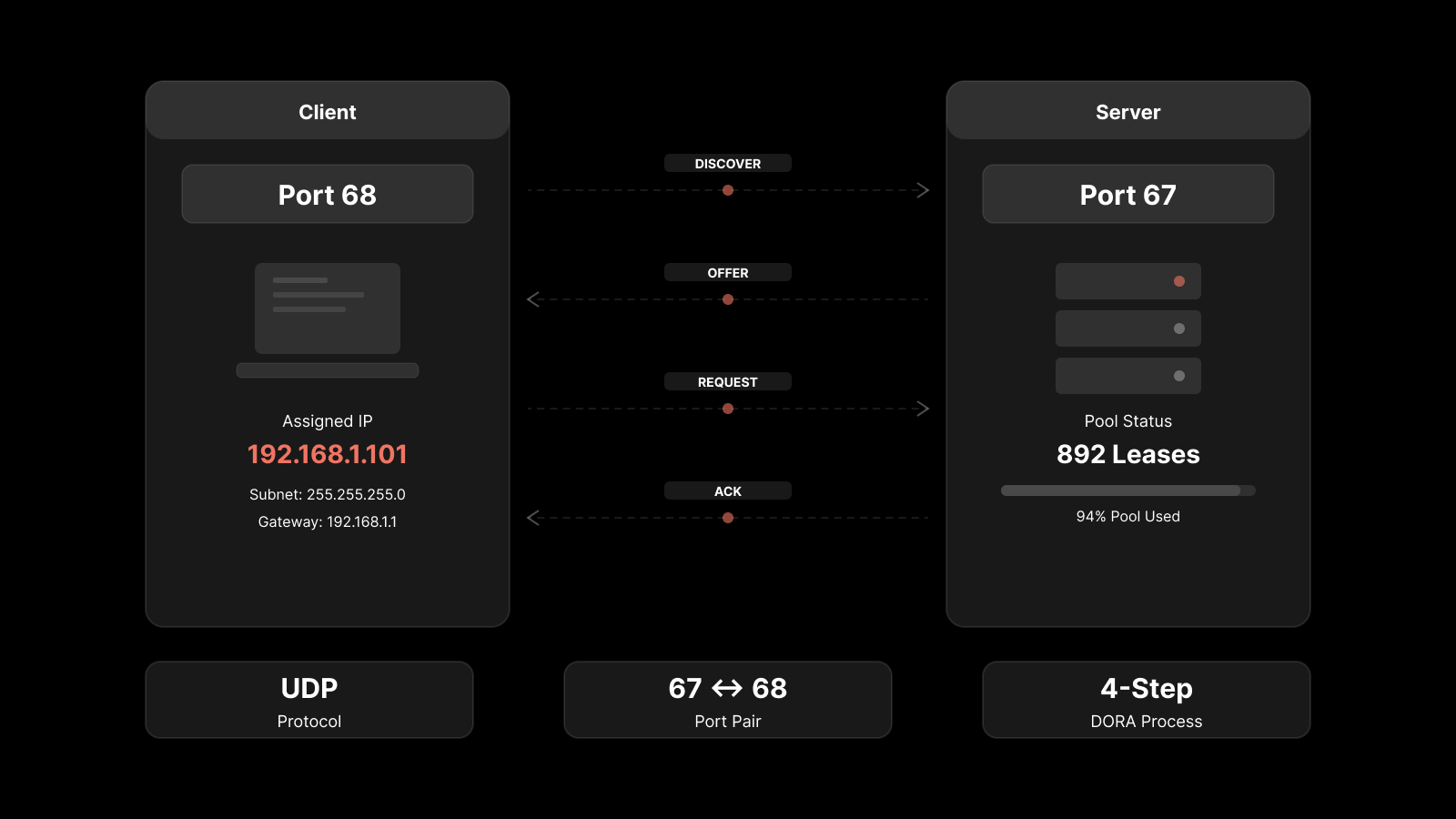
Alerts work as a simple notification system that lets your technicians know about an issue in the network and the right data points to get the context clear in one go and the log files to track the root cause.
In conjunction with the alerts, you can also use automated workflows to let the system resolve issues that can be resolved with simple scripts.
Giving authorized access to specific files, managing login ID or password, and dynamic use of CPU are generally such issues. With a conditional argument embedded in the code, you can program the trigger for these alerts.
To understand how alerts work on a system:
What Constitutes an Alert:
This would include the type of errors earlier logged in the system, statistical anomalies, and threshold limits.
Using quantitative and straightforward definitions for the steady-state system, you can create an alerting mechanism that pushes notification only when necessary.
The entire motive of installing an alerting system into the Network Monitoring platform is to ensure that human capital is optimally used.
Such a system puts you in a position to engineer the solution for each problem in the system using a simple rule-based approach.
Once you have an approach of this type in place, you will only engage human intelligence for matters that are urgent, important, and too complex for an algorithm to solve.
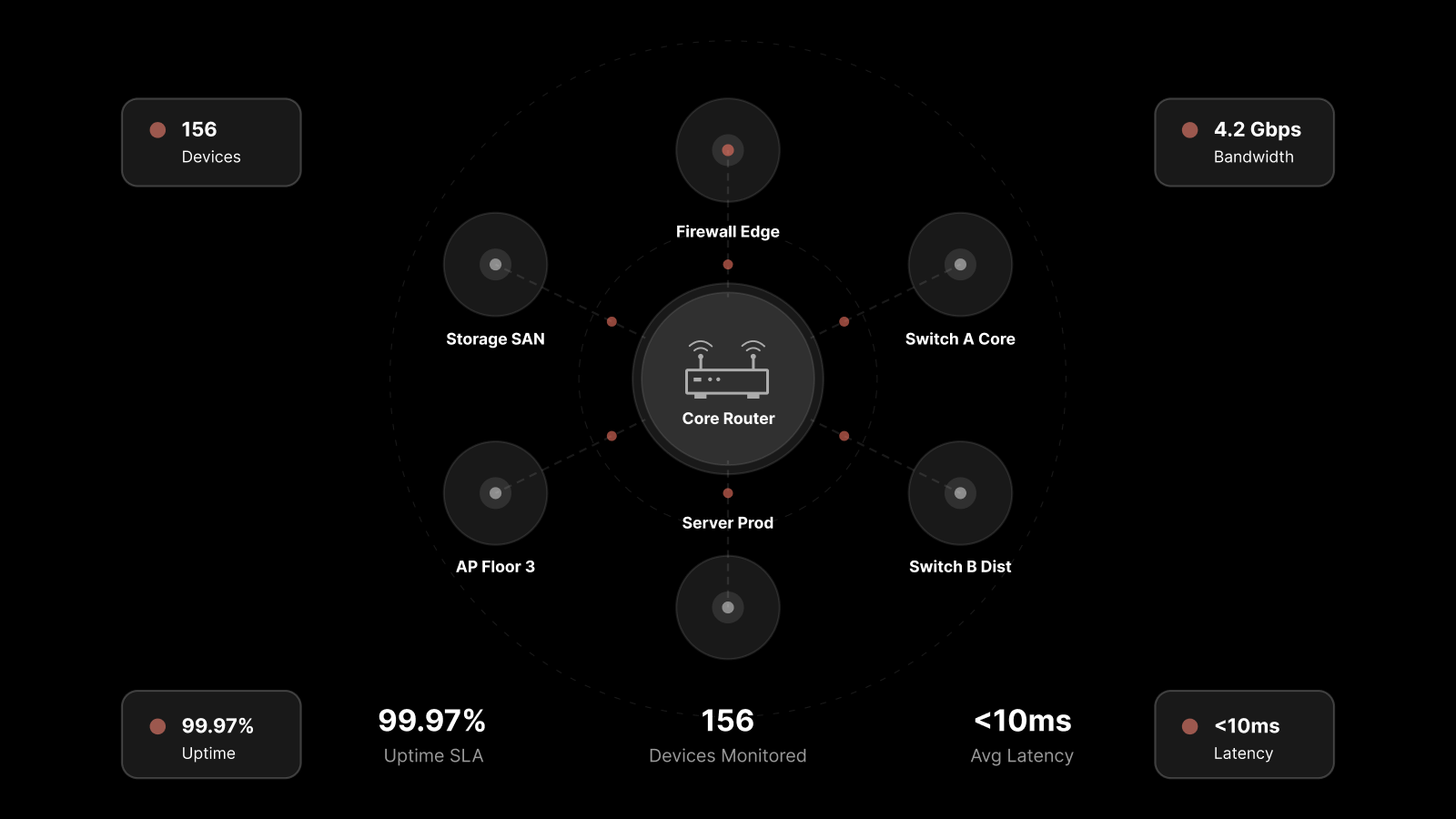
To engineer an effective alerting system, you will need a comprehensive network monitoring system that can automatically trigger workflows, measure the correlation between real-time issues, and give you intelligent insights on the system’s performance in real-time.
Once the alert rules have been triggered, the technicians should be notified on all mediums of communication, including but not limited to emails, text messages, and enterprise collaboration tools.
Understanding the Types of Alerts and Their Triggers
An effective alerting system can be engineered only based on understanding what type of alerts are generally prevalent in the network.
Here is an indicative list to help you create prospective workflows for consequent alerts:
1. Flooding Alerts
They are triggered when the network-layer is witnessing a statistically significant flooding attack across the DDoS layer.
2. Security Assessment & Breach Alerts
It ensures that your mandated security policies are followed across the system. You get alerts as soon as there is a breach of the security rules in place.
3. Configuration and Trap Alerts
They alert the team of technicians whenever the system is experiencing a noteworthy change in files configuration.
It works equally well across sensitive settings like that of a firewall, as well as ancillary configurations like the pathway of a file.
4. Detected Pattern Alert
As soon as your network logs detect a pattern that matches the precursory nature of historical system issues.
You can also configure these for quantitatively anomalous patterns that detect suspicious activity.
5. Inactivity Alerts
These alerts are triggered when a designated and necessary activity is not executed within a scheduled time or as per the mandated standard of operations.
6. Monitor Alerts
These are collections of alerts pertinent to each IP.
It can help you understand whether there are issues with the system or with the way the IP is being utilized.
7. Flow and Log Alerts
These are alerts sent out on specific triggers of a flow or suspicious logging activity recorded on the network.
Performance Metrics of Well-Functioning Alerting
After encompassing all the forms of alerts into your alerting system, you would want to test whether it is effective or not.
Here are the key properties of a well-engineered alerting system that is significantly bringing down the time spent by technicians in monitoring the dashboard:
1. Contextual Alerting:
A loud message that shows there is systemic error would be little help to the technician.
Each alert must establish a context that further plays into the root cause analysis and eventually, the solution engineering process.
2. Corrective Action Triggers:
If you cannot trigger corrective action to a certain type of systemic issue, you can integrate it with a certain form of a conditional alert.
As soon as the alert is the trigger, the system should run the patch to fix the issue.
This way, the technician just has to check whether the problem has been resolved or not.
It makes the process efficient by making the technician interfere only when it is critical.
3. Alert Footnotes:
Each alert should have its footnotes that help in the unique identification of the alert.
It should also help the Network Monitoring team work on the alert consequentially as soon as it is triggered and hence should serve as a starting point for the discussion.
4. Correlation Between Alerts:
This is a simple and yet sophisticated feature in the system which will allow you to expedite the RCA process.
By getting the correlation of two alerts showing different issues in the system, you can often find an underlying problem that would’ve proceeded as an unnoticed issue for long.
5. Alert Urgency and Frequency Control:
Your network monitoring platform should not be sending alerts at the first possible instance of an issue.
This would create fatigue among the technicians. Each alert should indicate the complexity of the issue and hence necessitate the technician’s involvement.
6. Communication Flexibility:
The alerting system should send out notifications across a broad spectrum of mediums.
Some alerting systems are engineered to take the help of APIs used for sending out notifications using third-party apps and platforms.
This can reduce the burden and scope of the alerting feature in the system and make it more efficient.
In Conclusion
The ability to aggregate data to monitor components, running it through necessary metrics and configuring alerts is critical to troubleshoot issues and problems and keep the production infrastructure’s performance consistent.
On top of this, if you can have a real-time understanding of which components are not performing as per the established benchmarks and what resources are necessary to get them back to running, you can mitigate all downtime with efficient resource allocation.
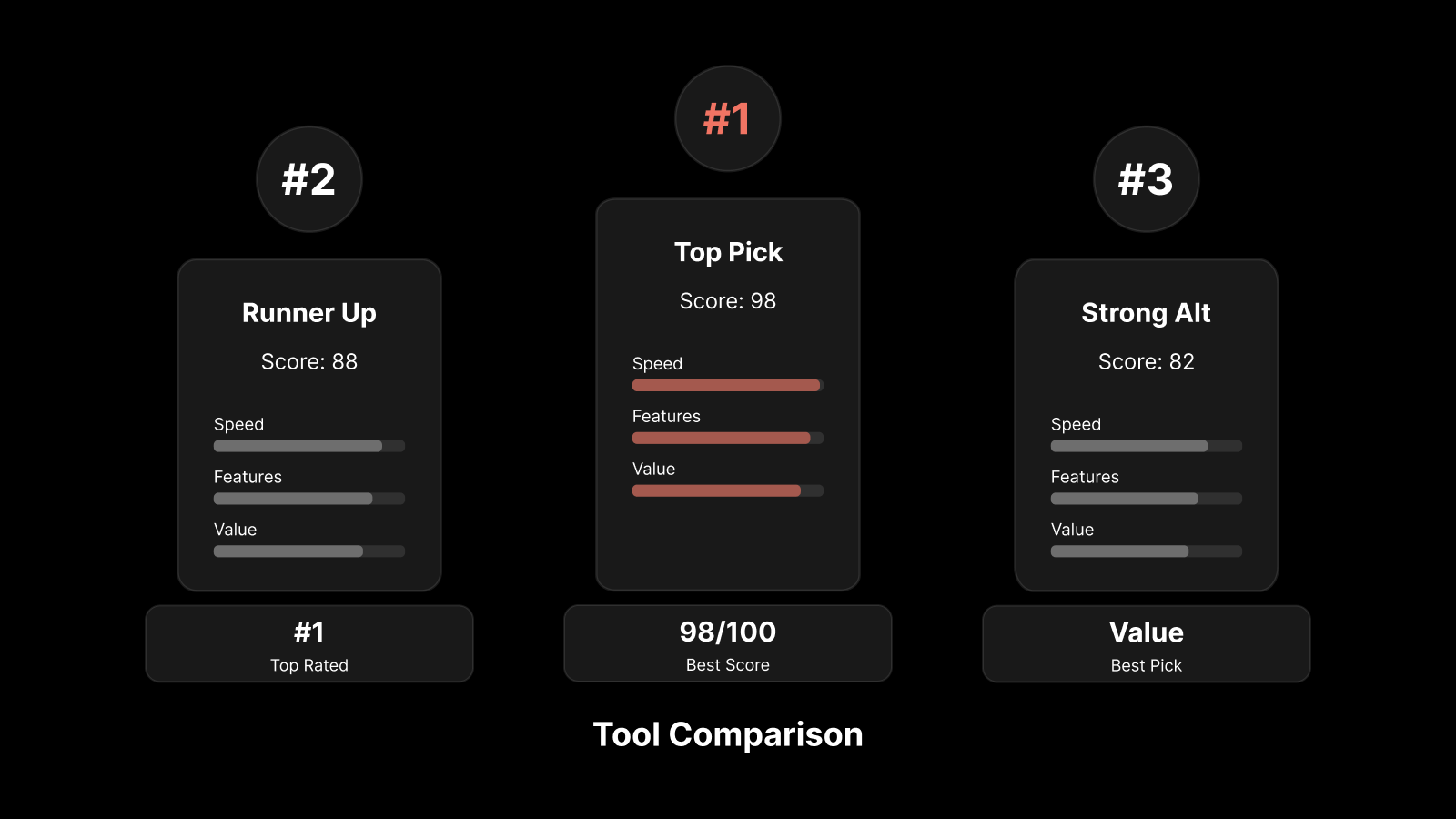
Monitoring tool such as Motadata are designed to give you granular control on tracking data at the monitor level.
The system automatically analyses historical performance and establishes statistical thresholds with conditional values.
As soon as these conditional values are breached, you are sent an instantaneous alert with the right context.
For more details write to sales@motadata.com