How to Prevent IT Outages: Building Resilience with Proactive Monitoring
Definition: IT resilience is an organization's ability to anticipate, withstand, recover from, and adapt to adverse conditions, disruptions, or cyberattacks that affect IT systems -- ensuring continuous business operations with minimal downtime.
The CrowdStrike outage of July 2024 knocked over 8.5 million Windows systems offline, cost Fortune 500 companies an estimated $5.4 billion, and grounded flights, froze banking systems, and disrupted hospitals worldwide. It wasn't a sophisticated cyberattack. It was a faulty software update that bypassed adequate testing.
That single incident proved what IT leaders already suspected: no organization is immune to outages, and the gap between "operational" and "offline" can be measured in seconds. The question isn't whether disruptions will happen - it's whether your infrastructure can detect them early, contain them fast, and recover before the damage compounds.
Why IT Outages Keep Getting Worse
The frequency and impact of IT outages have escalated for three interconnected reasons:
Growing infrastructure complexity. Hybrid and multi-cloud environments, containerized applications, microservices architectures, and distributed workforces create more potential failure points than ever. A single misconfiguration can cascade across interconnected systems in minutes.
Vendor concentration risk. Many organizations rely on a handful of platforms for critical functions. When the CrowdStrike update failed, it didn't just affect CrowdStrike customers -- it rippled through Microsoft Azure, Google Cloud, and every downstream service that depended on those endpoints.
Accelerated change velocity. Rapid deployment cycles mean more updates, more configuration changes, and more opportunities for errors to slip through. Without rigorous testing and staged rollouts, a single bad push can take down production environments globally.
Gartner recommends a multi-cloud strategy specifically to avoid total dependence on single points of failure and to select the right environments for each workload. But diversification alone isn't enough -- you need the monitoring and response capabilities to detect problems across all those environments in real time.
The Anatomy of IT Resilience
True IT resilience isn't a single tool or capability. It's a layered approach that spans five pillars:
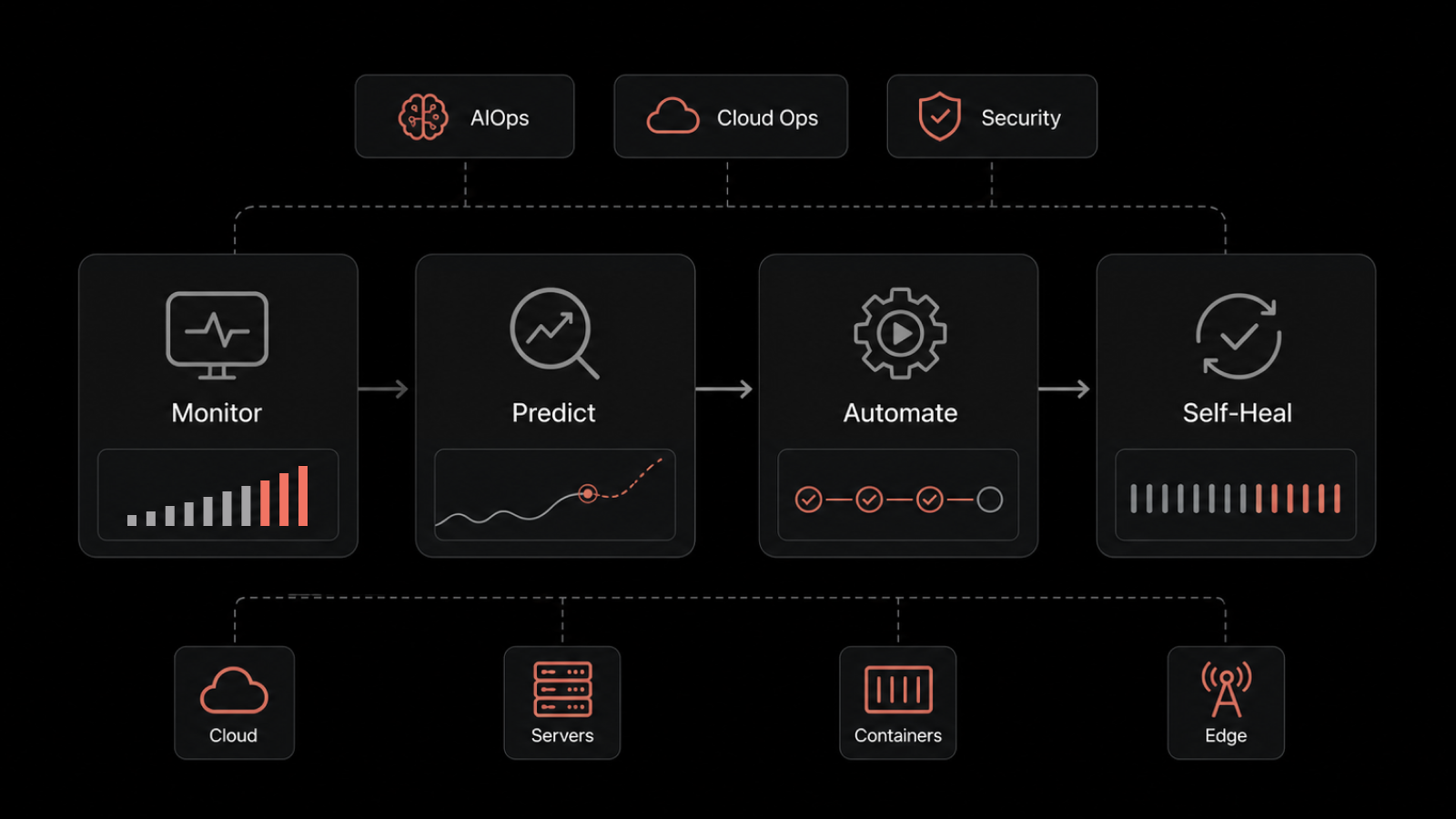
1. Proactive Monitoring and Early Detection
You can't fix what you can't see. Continuous monitoring of infrastructure, applications, and network components provides the visibility teams need to catch issues before users notice them.
Effective monitoring goes beyond simple uptime checks. It tracks CPU utilization, memory consumption, network latency, disk capacity trends, and application response times across every device and service in your environment. When any parameter drifts outside its normal range, the system triggers alerts so your team can investigate before performance degrades.
Event correlation takes this further by linking related data points across multiple systems. Instead of drowning in isolated alerts, teams see unified incident narratives that accelerate root cause identification.
2. Predictive Analytics and AI-Driven Intelligence
Historical data holds patterns that human analysts often miss. Machine learning algorithms analyze past performance trends to forecast potential disruptions before they materialize.
For example, if disk space consumption is trending upward at 5% daily, predictive analytics flags the capacity shortfall weeks in advance. If workload patterns indicate a server approaching resource exhaustion during peak hours, the system recommends load balancing or workload redistribution proactively.
AI-driven anomaly detection establishes behavioral baselines for your environment and identifies deviations that could signal emerging threats or impending failures. This shifts your posture from reactive firefighting to proactive prevention.
3. Automated Incident Response
When incidents do occur, response speed determines impact severity. Automation eliminates the delay between detection and action by executing predefined runbooks without waiting for human intervention.
If a server shows signs of overheating, automated workflows can initiate cooling procedures or redistribute workloads. If a network anomaly suggests an intrusion, containment protocols can isolate affected segments while alerting security teams. Network automation handles the repetitive, time-sensitive actions that manual processes can't match at scale.
Self-healing capabilities take this further. Systems designed with automated recovery can detect faults and restore normal operations independently -- rerouting traffic, failover to backup resources, and restarting services without operator involvement. This reduces mean time to resolution (MTTR) from hours to minutes.
Building Your Outage Prevention Strategy
A resilient IT infrastructure requires deliberate planning across four operational domains:
Log Analytics for Threat Discovery
Your logs contain the early warning signals that dashboards often miss. Log analytics gathers, categorizes, and examines log data from network devices, servers, and applications to uncover unusual patterns or indicators of security issues.
Real-time log ingestion captures events as they happen, providing a dynamic view of your IT landscape. Advanced search and filtering let teams define specific criteria -- timeframes, source locations, severity levels -- to pinpoint critical information without being overwhelmed by volume. When correlated with threat intelligence feeds, log data reveals risks that isolated monitoring tools would miss.
Service Desk as Your Resilience Hub
Your service desk isn't just a ticket queue -- it's the operational hub where resilience meets execution. Effective incident management means logging issues as they arrive, prioritizing by business impact, and driving resolution without wasted time.
Problem management goes deeper, identifying root causes of recurring incidents and implementing preventive measures. A well-maintained knowledge base gives technicians instant access to troubleshooting guides, standard procedures, and lessons learned from previous incidents, accelerating resolution and reducing escalations.
ITIL-aligned processes ensure that service delivery remains consistent, measurable, and continuously improving -- even when the unexpected happens.
IT Asset Management and Visibility
You can't protect assets you don't know about. Comprehensive asset discovery and management catalogs every piece of hardware and software in your environment, from servers and desktops to software licenses and cloud subscriptions.
Automated network scans maintain an accurate, up-to-date inventory that eliminates the blind spots where vulnerabilities hide. This visibility supports capacity planning, ensures license compliance, and identifies outdated or unsupported technology before it becomes a reliability risk.
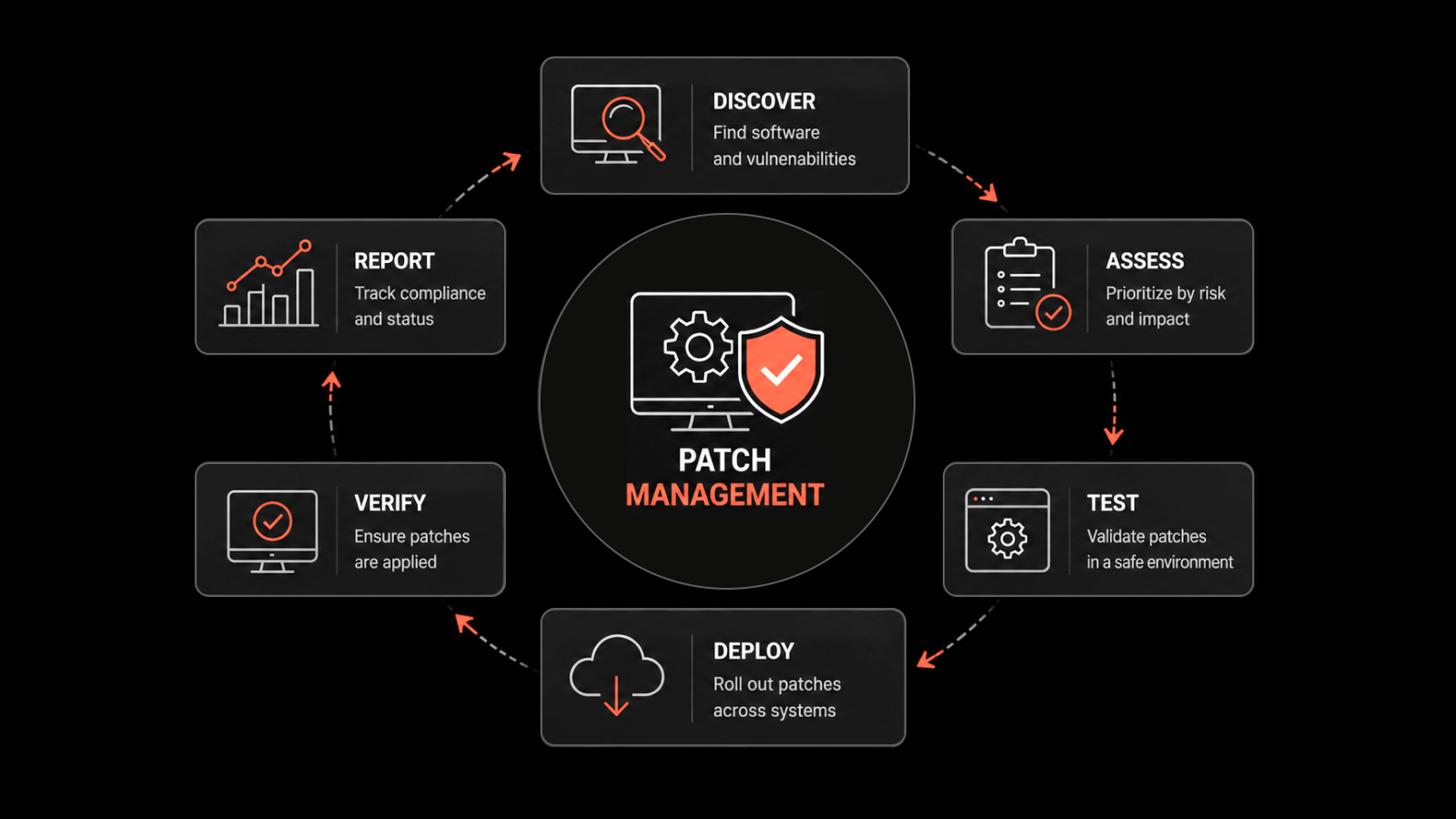
Patch Management as a Defense Layer
Unpatched systems are open invitations for exploitation. Proactive patch management identifies, assesses, and deploys security updates across your infrastructure before vulnerabilities can be exploited.
Automated patch deployment eliminates the delays and errors inherent in manual processes. Vulnerability assessments continuously scan for weaknesses, prioritize remediation by risk level, and verify that patches are applied successfully. This discipline closes the window between vulnerability disclosure and protection.
Lessons from the CrowdStrike Outage
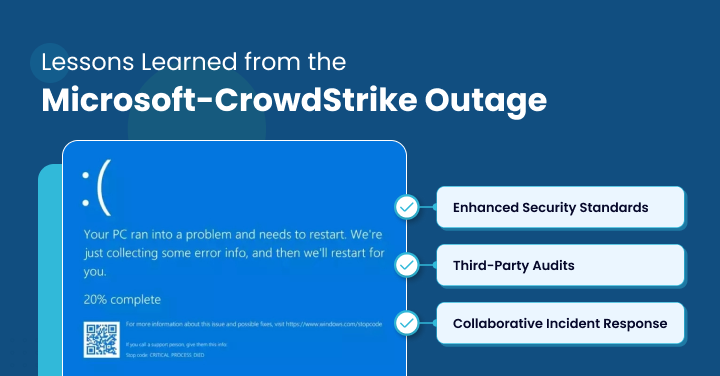
The July 2024 CrowdStrike incident offers concrete lessons for every organization building IT resilience:
Test rigorously and deploy incrementally. The root cause was a faulty test that slipped past quality assurance. Staged rollouts -- deploying updates to a small percentage of systems before full release -- would have contained the blast radius.
Diversify your vendor ecosystem. Organizations that relied on a single endpoint security vendor had no fallback when that vendor's update failed. Multi-vendor strategies for critical security functions reduce single-point-of-failure risk.
Invest in independent monitoring. When your security tool itself is the source of the outage, you need monitoring capabilities that operate independently. Third-party observability and network monitoring provide the external perspective needed to detect issues regardless of their source.
Build collaborative incident response. Cross-vendor collaboration, shared threat intelligence, and coordinated response plans accelerate recovery when large-scale incidents affect multiple organizations simultaneously.
Measuring IT Resilience: Metrics That Matter
Building resilience without measuring it is guesswork. Track these metrics to assess and improve your resilience posture:
Mean Time to Detect (MTTD): How quickly your monitoring identifies an issue after it begins
Mean Time to Resolve (MTTR): Total time from detection to full resolution
Recovery Point Objective (RPO): Maximum acceptable data loss measured in time
Recovery Time Objective (RTO): Maximum acceptable downtime before business impact becomes critical
Change failure rate: Percentage of deployments that cause incidents
System availability: Uptime percentage across critical services (target: 99.9%+)
Regular testing -- including disaster recovery drills, failover exercises, and chaos engineering -- validates these metrics under realistic conditions and reveals gaps before real incidents expose them.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.