Network Automation for Multi-Cloud: How to Manage Complex Cloud Networks at Scale
Network automation for multi-cloud is the practice of using software to provision, configure, monitor, and manage network resources across multiple cloud providers — without manual, CLI-by-CLI intervention. It turns fragmented, provider-specific workflows into a unified, policy-driven process.
When your infrastructure spans AWS, Azure, and GCP, every manual configuration change is a risk. One engineer sets up a security group in AWS. Another configures an NSG in Azure with slightly different rules. A third provisions a firewall rule in GCP that contradicts both. Three clouds, three networking models, zero consistency.
That's the reality for most multi-cloud teams today. And it's exactly the problem network automation solves.
81% of enterprises now use two or more cloud providers. Each provider brings its own networking model, security framework, and management console. Without automation, your network team is managing three different ecosystems with manual processes — and every inconsistency is a potential outage, security gap, or compliance violation.
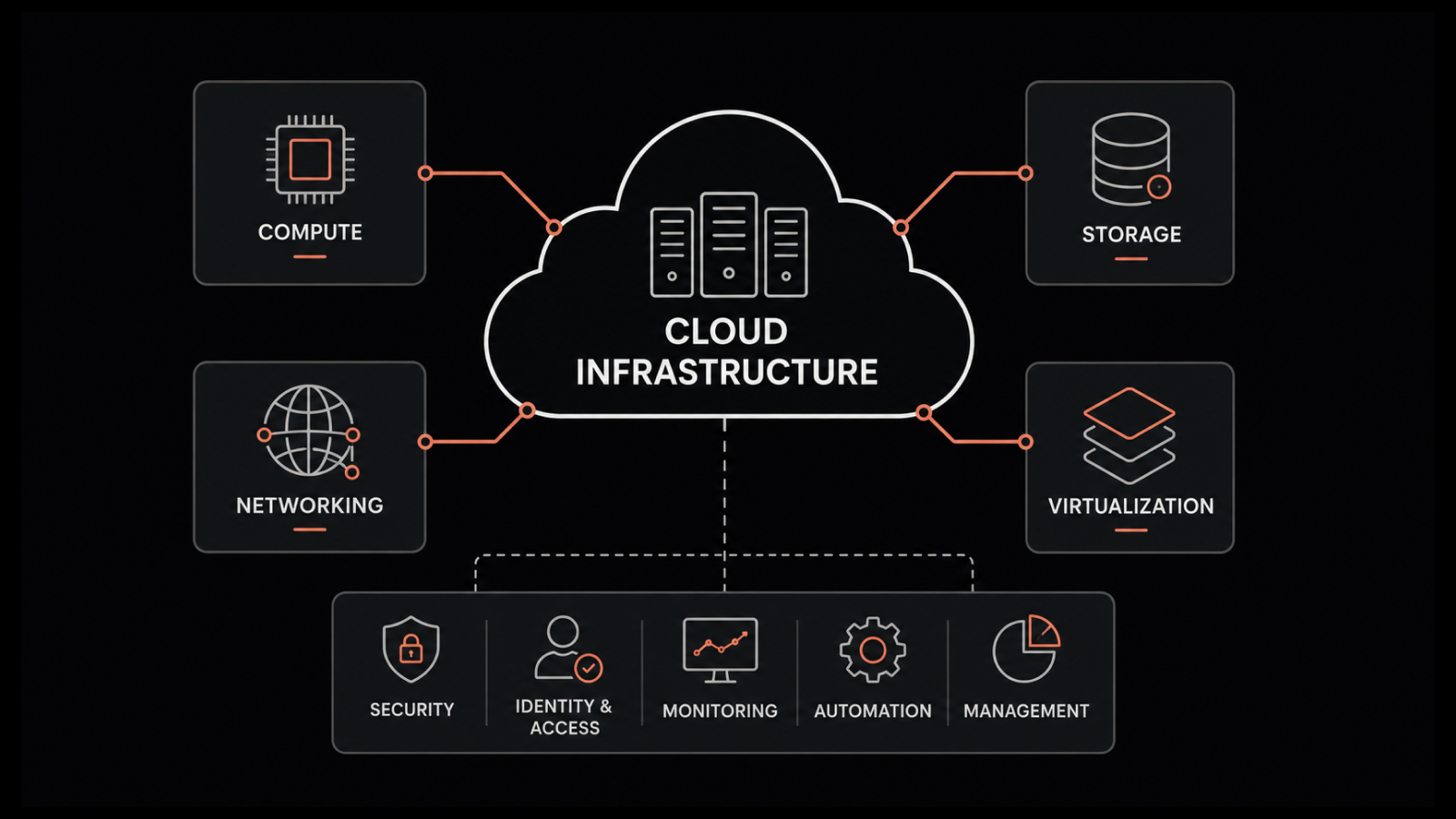
What Is Network Automation for Multi-Cloud?
Network automation for multi-cloud applies software-driven processes to manage network resources across two or more cloud providers. Instead of logging into each cloud's console to configure VPCs, subnets, routing tables, and security rules individually, automation handles these tasks programmatically.
Here's what that looks like in practice. A typical enterprise might run:
AWS for data storage and customer-facing workloads
Microsoft Azure for disaster recovery and enterprise applications
Google Cloud Platform for development, testing, and AI/ML workloads
Each platform structures its networking differently. AWS uses VPCs with security groups. Azure uses VNets with network security groups (NSGs). GCP uses VPC networks with firewall rules. The terminology differs. The configuration methods differ. The APIs differ.
Network automation abstracts these differences. You define your network policies once — "all production workloads must use encrypted east-west traffic" — and the automation platform translates that intent into provider-specific configurations across every cloud.
Why Multi-Cloud Networks Demand Automation
Up to 95% of network changes are still performed manually, according to industry research. In a single-cloud environment, that's manageable. In multi-cloud, it's a recipe for failure.
The Scale Problem
Every cloud provider you add multiplies the management burden. It's not additive — it's multiplicative. Two clouds don't mean double the work. They mean double the networking models, double the security frameworks, double the monitoring tools, and exponentially more potential for misconfigurations between them.
The Consistency Problem
When different engineers configure network resources in different clouds using different tools, configuration drift is inevitable. Drift leads to security gaps, compliance violations, and outages that are extremely difficult to diagnose because no single tool shows you the full picture.
The Speed Problem
Business teams expect new environments provisioned in hours, not weeks. Manual network configuration across multiple clouds can't keep pace with DevOps velocity. Automation is the only way to match network provisioning speed with application deployment speed.
The Cost Problem
Cloud network spending is notoriously difficult to control. 94% of enterprises overspend on cloud resources, and about 30% of cloud spend is wasted. Network-specific waste includes over-provisioned bandwidth, idle VPN tunnels, and redundant transit gateway connections that nobody tracks because visibility is fragmented.
Key Challenges of Managing Multi-Cloud Networks Without Automation
Navigating Divergent Cloud Networking Models
AWS relies on a service-oriented architecture with over 200 services. Azure is structured around resource groups and subscription models. GCP organizes resources into projects and folders. These aren't minor differences — they fundamentally change how you think about network design, segmentation, and access control.
This divergence adds substantial cognitive load for IT teams. An engineer who's an expert in AWS networking may struggle with Azure's networking model, and vice versa. Manual management means your team needs deep expertise in every platform — a hiring challenge that automation sidesteps entirely.
Visibility Gaps Across Clouds
Each cloud offers its own monitoring tools — AWS CloudWatch, Azure Monitor, Google Cloud Monitoring — but they don't integrate natively. You end up with three dashboards showing three partial views of one interconnected network.
87% of technology leaders say multi-cloud complexity makes it harder to deliver outstanding customer experiences. 84% say it makes applications harder to protect. These numbers aren't surprising when your visibility is fundamentally fragmented.
Security Inconsistencies
27% of organizations experienced a security incident in their public cloud infrastructure in the past 12 months. A major contributor: inconsistent security policies across clouds.
AWS IAM, Azure Active Directory, and Google Cloud IAM use different permission models, different policy syntax, and different enforcement mechanisms. Keeping security policies consistent across all three without automation requires heroic manual effort — and heroes make mistakes.
Financial Unpredictability
84% of businesses cite cloud spend management as their top cloud challenge. Most overspending traces back to idle resources, over-provisioned infrastructure, and missed reserved instance opportunities — problems that automation detects and resolves automatically.
How Network Automation Solves Multi-Cloud Complexity
Consistent Configuration Across Providers
Automation enforces the same policies across every cloud provider. Define a security baseline once, and the automation platform translates it into AWS security groups, Azure NSGs, and GCP firewall rules — all with the same effective permissions. No drift. No inconsistencies. No "we thought that port was closed" surprises.
Faster Provisioning and Change Management
What takes a network engineer hours of manual work — provisioning a new VPC, configuring routing, setting up peering connections — automation handles in minutes. Configuration changes deploy simultaneously across all affected environments, with automatic validation and rollback if something fails.
Reduced Human Error
Manual network configuration is error-prone by nature. A single typo in a routing table can take down an entire region. Automation removes the opportunity for these errors by using tested, version-controlled templates for every change.
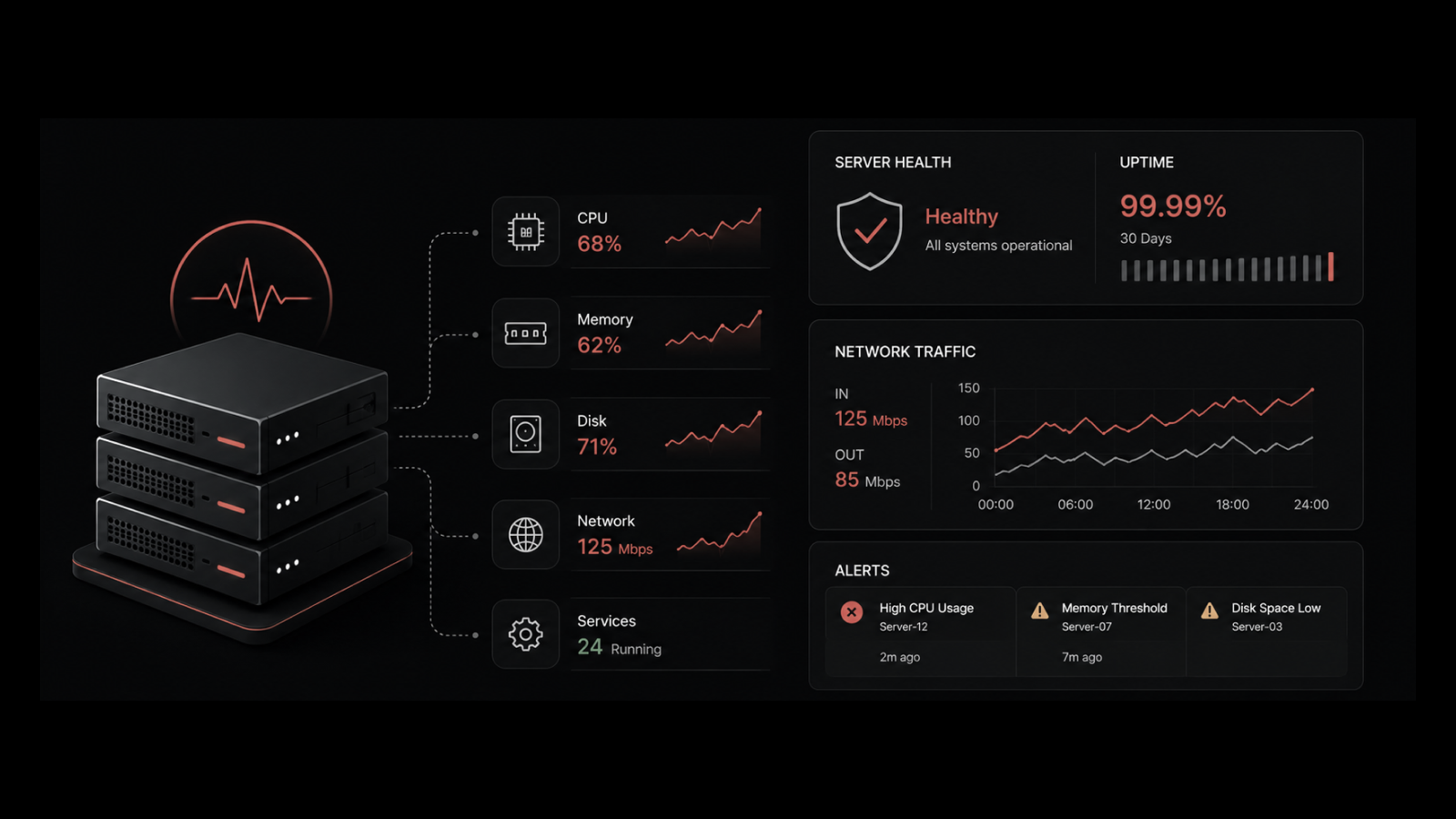
Unified Visibility and Monitoring
Network automation platforms provide a single pane of glass across all cloud providers. Instead of checking three separate consoles, your team sees the full network topology — cross-cloud dependencies, traffic patterns, and security posture — in one view.
Automated Compliance and Security
Compliance requirements (SOC 2, HIPAA, PCI-DSS) don't care which cloud you're using. Automation continuously validates that network configurations meet compliance standards across every environment. When something drifts out of compliance, automated remediation brings it back — before an auditor finds it.
Core Technologies Powering Multi-Cloud Network Automation
Infrastructure as Code (IaC)
Infrastructure as Code lets you define network resources — VPCs, subnets, routing tables, security groups — in declarative configuration files. Tools like Terraform and Pulumi support multi-cloud deployments from a single codebase.
The advantage for multi-cloud networking: you version-control your network configurations the same way you version-control application code. Every change is tracked, reviewable, and rollbackable. Teams can use GitOps workflows to approve and deploy network changes through the same CI/CD pipelines they use for applications.
Software-Defined Networking (SDN)
Software-defined networking separates the control plane (where traffic decisions are made) from the data plane (where traffic flows). This separation is what makes centralized, cross-cloud network management possible.
With SDN, you manage network behavior through software policies rather than device-by-device hardware configuration. In a multi-cloud context, SDN lets you create consistent overlay networks that span multiple cloud providers — giving your applications a unified network fabric regardless of where they run.
API-Driven Network Management
Every major cloud provider exposes its networking capabilities through APIs. Network automation platforms use these APIs to provision, configure, and monitor network resources programmatically. APIs make it possible to integrate network operations into broader automation workflows — triggering network changes based on application deployments, scaling events, or security alerts.
Network Configuration Management (NCM)
NCM tools automate the management of device configurations — both in the cloud and on-premises. They handle config backups, change tracking, compliance validation, and bulk updates. In multi-cloud environments, NCM ensures that configuration changes are documented, authorized, and reversible.
Intent-Based Networking (IBN)
IBN represents the next evolution of network automation. Instead of telling the network how to configure itself, you tell it what outcome you want. "All production workloads must be isolated from development workloads across all clouds." The IBN system figures out the specific configurations needed on each cloud provider to achieve that intent. AI and ML continuously verify that the network's actual state matches the declared intent — and automatically remediate any deviations.
How to Implement Network Automation Across Cloud Providers
Step 1: Audit Your Current State
Before automating anything, map your existing multi-cloud network. Document every VPC, subnet, peering connection, VPN tunnel, and security rule across all providers. Identify inconsistencies, redundancies, and gaps. This audit becomes your automation baseline.
Step 2: Start with One High-Impact Use Case
Don't try to automate everything at once. Pick one use case that delivers immediate, measurable value:
Configuration backup and compliance: Automatically back up network configs and check them against compliance baselines
Security policy enforcement: Ensure consistent security groups and firewall rules across all clouds
Provisioning: Automate the creation of new environments with standardized network templates
Step 3: Standardize on IaC and Version Control
Move your network configurations into code. Use Terraform modules or Pulumi programs to define reusable network blueprints for each cloud provider. Store everything in version control. Require code reviews for network changes — the same way you require them for application changes.
Step 4: Build Cross-Cloud Visibility
Deploy a unified network monitoring platform that aggregates data from all cloud providers. You can't automate what you can't see. Cross-cloud visibility lets you validate that automation is working correctly and catch issues before they escalate.
Step 5: Invest in Team Skills
Network automation requires skills that traditional network engineers may not have — Python scripting, IaC tools, API integration, CI/CD pipelines. Invest in training. The payoff is enormous: engineers who can write automation scripts instead of manually configuring devices are 10x more productive.
Step 6: Continuously Monitor and Optimize
Network automation isn't a one-time project. Cloud providers release new networking features constantly. Business requirements evolve. Your automation must evolve with them. Build feedback loops: monitor automation outcomes, measure error rates and provisioning times, and refine your playbooks based on real-world results.
Multi-Cloud Network Security and Compliance Automation
Security deserves special attention in multi-cloud environments because the attack surface is significantly larger than in single-cloud setups.
Unified Security Policy Management
Define security policies as code and enforce them across every cloud provider. This means consistent:
Access controls: Who can access what, across all clouds
Encryption policies: In-transit and at-rest encryption standards applied uniformly
Network segmentation: Consistent micro-segmentation across cloud boundaries
Audit logging: Centralized logging of all network changes for compliance
Automated Vulnerability Assessment
Use automation to continuously scan your multi-cloud network for vulnerabilities — exposed ports, misconfigured security groups, overly permissive access rules. Vulnerability assessment that runs automatically catches issues that periodic manual audits miss.
Compliance as Code
Encode compliance requirements (SOC 2 controls, PCI-DSS requirements, HIPAA safeguards) as automated checks. Run them continuously against your multi-cloud network. Generate compliance reports automatically. When a configuration drifts out of compliance, automated remediation fixes it before it becomes an audit finding.
What IT Teams Should Also Know About Multi-Cloud Network Automation
How does network automation handle failover across cloud providers?
Network automation platforms can configure automated failover policies that detect outages in one cloud and reroute traffic to another. This includes updating DNS records, adjusting load balancer configurations, and activating standby environments — all without manual intervention. The key requirement is cross-cloud visibility to detect the failure in the first place.
Can I automate networking for hybrid environments (cloud + on-premises)?
Yes. Modern network automation tools handle both cloud and on-premises infrastructure. IaC tools like Terraform support on-premises providers alongside AWS, Azure, and GCP. The automation platform treats all environments as part of one network fabric, applying consistent policies everywhere.
What's the relationship between NetOps and network automation?
NetOps is the operational practice. Network automation is the enabling technology. NetOps teams use automation to shift from reactive troubleshooting to proactive management — spending less time on repetitive tasks and more time on strategic network design and optimization.
How do I measure ROI on network automation?
Track these metrics: mean time to provision new environments (should drop 80%+), configuration-related outages (should approach zero), compliance violation count (should decrease), and network engineer time spent on manual tasks (should drop significantly). Most organizations see positive ROI within 6-12 months of deploying network automation.
How Motadata Simplifies Multi-Cloud Network Automation
Motadata's AI-native platform unifies network automation and monitoring across multi-cloud and hybrid environments. Instead of managing separate tools for each cloud provider, your team gets a single console with auto-discovery, network configuration management, and policy-driven automation across your entire network fabric.
What makes it practical: AI-powered anomaly detection that identifies configuration drift and security gaps across clouds, automated compliance validation against industry standards, and real-time topology mapping that shows cross-cloud dependencies. Teams typically see 70%+ reduction in manual network tasks and significantly faster incident resolution.
If your multi-cloud network management is consuming more engineering hours than it should, request a demo to see how Motadata changes the equation.
Frequently Asked Questions
Q: What is network automation for multi-cloud?
A: Network automation for multi-cloud uses software to provision, configure, monitor, and manage network resources across multiple cloud providers (AWS, Azure, GCP) without manual intervention. Instead of logging into each cloud's console separately, automation platforms handle these tasks programmatically using APIs, Infrastructure as Code, and policy-driven workflows. The goal is consistent, repeatable network management regardless of which clouds you use.
Q: Why is network automation necessary for multi-cloud environments?
A: Each cloud provider uses different networking models, security frameworks, and management tools. Managing them manually creates configuration drift, security inconsistencies, and compliance gaps. At scale — with hundreds of VPCs, subnets, and security rules across multiple clouds — manual management is simply too slow and error-prone. Automation ensures consistency and speed that manual processes can't match.
Q: What tools are used for multi-cloud network automation?
A: The core technology stack includes Infrastructure as Code tools (Terraform, Pulumi), Software-Defined Networking platforms, API-driven management interfaces, and Network Configuration Management tools. Many organizations also adopt intent-based networking systems that translate business goals into specific network configurations across all cloud providers.
Q: How long does it take to implement multi-cloud network automation?
A: A focused initial deployment — automating one use case like configuration backup or security policy enforcement — typically takes 4-8 weeks. Full multi-cloud network automation maturity, covering provisioning, compliance, monitoring, and remediation across all providers, usually takes 6-12 months. The key is starting small and expanding incrementally.
Q: Is network automation secure?
A: Network automation actually improves security when implemented correctly. It eliminates manual configuration errors (a leading cause of breaches), enforces consistent security policies across all clouds, and enables continuous compliance monitoring. The security risk isn't automation itself — it's poorly designed automation. Use role-based access controls, encrypt automation credentials, and audit all automated changes.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.