8 Network Security Monitoring Best Practices Every IT Team Should Follow
Arpit Sharma
Network security monitoring is the continuous process of collecting, analyzing, and acting on network data to detect threats, identify vulnerabilities, and protect infrastructure from unauthorized access, malware, and data breaches. It combines real-time visibility, automated detection, and incident response to keep networks secure.
Security attacks continue to rise year over year, and most organizations still aren't ready. The gap isn't usually a lack of security tools — it's a lack of continuous monitoring, clear practices, and operational discipline. Whether your organization is running 50 devices or 50,000, network security monitoring is what stands between your infrastructure and the next breach. A single intrusion can cause significant financial damage and erode customer trust. These eight best practices give your team a practical framework for building and maintaining a network security monitoring program that actually works.
Why Network Security Monitoring Matters
Network security covers technologies, devices, processes, and systems designed to protect your network and data. The goal is straightforward: let the organization achieve its business objectives without getting disrupted by security incidents.
Network intrusions — whether DDoS attacks, malware infections, or insider threats — can do serious damage. A single breach can compromise sensitive data, disrupt operations, and damage your organization's reputation for years. Network security monitoring provides the continuous visibility and automated detection needed to catch threats early and respond fast.
Finding actionable guidance on this topic can be difficult. Here are eight best practices that network and security teams can implement regardless of organizational size, industry, or infrastructure complexity.
8 Network Security Monitoring Best Practices for 2026
1. Conduct a Comprehensive Network Security Audit
A thorough network audit is the starting point for identifying weaknesses and security gaps in your infrastructure. Before you can monitor effectively, you need to know what you're protecting and where the vulnerabilities are.
A comprehensive network audit should identify and assess:
Security vulnerabilities in network architecture, device configurations, and application settings.
Unnecessary applications and services running on network devices that expand your attack surface.
Anti-virus and anti-malware coverage — verify all endpoints have current protection and that no suspicious software is present.
Third-party application and vendor risks — assess the security posture of every integration and external dependency.
Policy compliance gaps — check configurations against your security policies and industry standards.
Run these audits on a regular cadence — quarterly at minimum, and immediately after any significant infrastructure change. The audit results become your roadmap for strengthening monitoring coverage and closing security gaps.
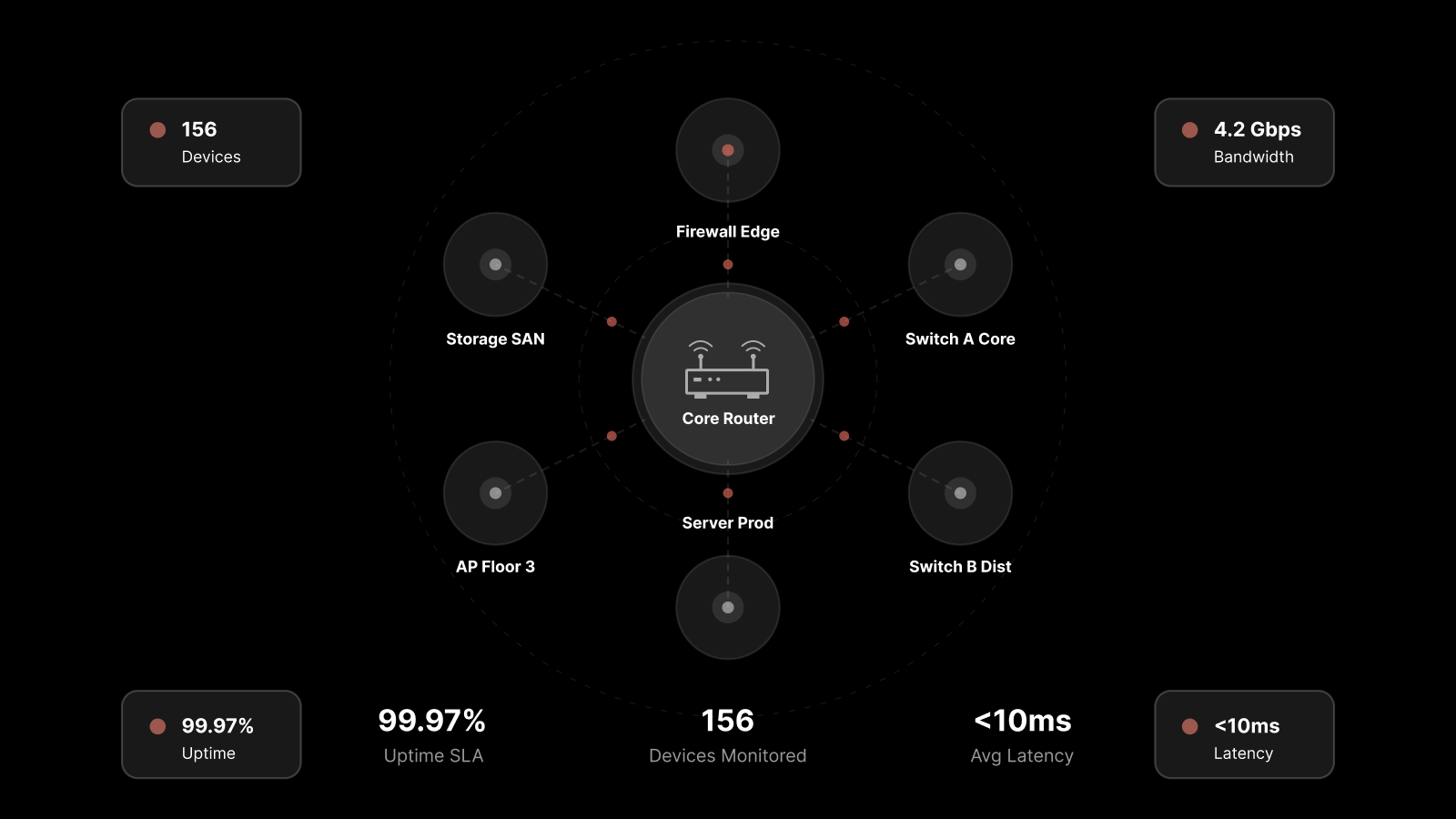
2. Deploy Tools That Deliver Full Network Visibility
In interconnected environments, you need to see everything that's happening on your network. Without monitoring your network traffic, you won't spot threats, vulnerabilities, or misconfigurations until they cause real damage.
A good network monitoring tool should provide:
Real-time traffic analysis to detect unusual patterns and potential threats.
Device discovery and inventory to maintain an accurate map of everything on your network.
Alert correlation to group related events and reduce noise.
Historical data retention for forensic analysis and trend identification.
Integration with SIEM and ITSM platforms for automated incident workflows.
The tool you choose should match your network's complexity and scale. Look for platforms that combine network monitoring with security analytics — so your team gets both performance and security visibility from a single pane of glass.
3. Strengthen Router and Network Device Security
Network devices like routers and switches are high-value targets. An attacker who gains access to a router can intercept traffic, redirect communications, or pivot deeper into your network.
Common attack vectors include:
Default credentials — Many devices ship with well-known default usernames and passwords. Change them immediately upon deployment.
Physical access — A router reset can wipe custom configurations and restore defaults. Keep network devices in secured, locked locations.
Outdated firmware — Unpatched devices are vulnerable to known exploits. Maintain a firmware update schedule for all network equipment.
Additional hardening steps:
Disable unused ports and services on all network devices.
Enable logging on routers and switches and forward logs to your monitoring platform.
Implement network segmentation to limit the blast radius if a device is compromised.
Use SNMPv3 instead of SNMPv1/v2c for secure device management.
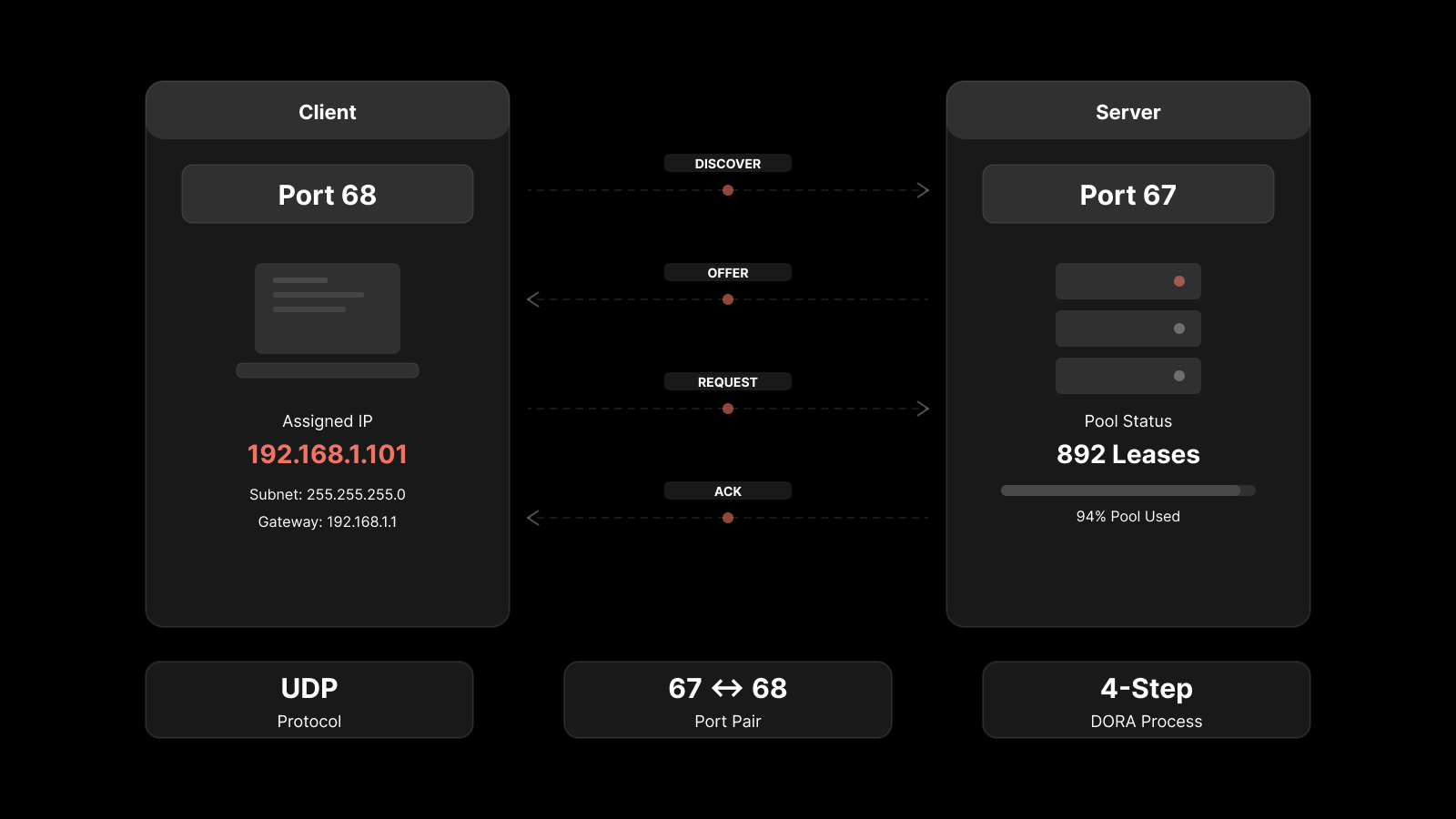
4. Protect Infrastructure with Private IP Addressing
Servers and critical infrastructure exposed with public IP addresses are directly reachable from the internet — and directly targetable by attackers. Using private IP addressing for internal resources reduces your attack surface significantly.
Private IP addresses are only visible within your LAN or VPN. They can't be reached directly from the internet, which means attackers can't target them without first gaining access to your internal network.
Implementation guidelines:
Place all internal servers, databases, and management interfaces behind private IP ranges.
Use NAT (Network Address Translation) for any internal resources that need internet access.
Deploy VPN solutions for remote access to internal resources rather than exposing services publicly.
Use firewall rules to strictly control traffic between public-facing and private network segments.
This approach also helps with compliance — private addresses can't be tracked via IP geolocation, adding a layer of obscurity to your infrastructure's physical location.
5. Secure or Disable Unencrypted File Sharing
File sharing protocols that transmit data in plain text are an easy target for attackers. Any unencrypted file transfer can be intercepted, read, and modified by anyone with access to the network path.
Best practices for file sharing security:
Disable default file-sharing services (SMBv1, FTP) on all devices where they're not explicitly needed.
Use encrypted alternatives — SFTP, SCP, or enterprise file-sharing platforms with end-to-end encryption.
Monitor file-sharing activity through your network monitoring tools to detect unauthorized transfers.
Apply access controls to shared folders and resources — restrict access to only the users and groups that need it.
Audit file-sharing configurations regularly as part of your security review cycle.
6. Encrypt Data in Transit Across Your Network
Encryption protects data from being intercepted or modified while it travels across your network. In-transit encryption is essential — not just for external traffic, but for internal communications too.
Key encryption practices:
Deploy HTTPS everywhere — Use TLS encryption for all web traffic, including intranet sites and internal APIs. While internal HTTPS is more complex to manage, the security benefits are significant on larger networks.
Encrypt management traffic — SSH instead of Telnet, SNMPv3 instead of SNMPv1/v2, and encrypted syslog where supported.
Use VPN tunnels for site-to-site connections and remote access.
Monitor certificate expiration — Expired certificates can cause outages and create security gaps. Automate certificate lifecycle management where possible.
Don't assume that devices on your internal network are trustworthy. Lateral movement is a common attack technique — once an attacker gets past your perimeter, encrypted internal traffic limits what they can intercept.
7. Categorize Devices and Enforce Access Controls
Different devices serve different purposes and carry different risk levels. Classifying devices based on function and data sensitivity helps you apply the right security controls to each category.
Device categories to define:
Critical infrastructure — Servers, databases, domain controllers (strictest access controls).
Network equipment — Routers, switches, firewalls (management access restricted to network admins).
Workstations — Employee devices (access controls based on role and department).
IoT devices — Sensors, cameras, smart devices (isolated on separate VLANs with limited network access).
Guest devices — Visitor and contractor devices (restricted to internet access only, no internal network access).
Once categorized, enforce access controls:
Apply the principle of least privilege — devices and users get only the access they need.
Use network segmentation (VLANs) to isolate device categories from each other.
Implement 802.1X port-based authentication to prevent unauthorized devices from connecting.
Monitor access patterns through your security monitoring platform to detect policy violations.
Network administrators gain better insight into potential vulnerabilities when every device type is clearly identified and access-controlled.
8. Maintain Patch Compliance Across All Endpoints
Security vulnerabilities are inevitable — every device in your IT infrastructure will have them at some point. Keeping everything updated is one of the most effective defenses against known exploits.
Attackers actively scan for unpatched systems because they're easy targets. A fully patched network dramatically reduces your exposure to known vulnerabilities.
Patch management best practices:
Establish a patching cadence — Critical patches within 48 hours, non-critical patches within 30 days.
Use automated patch management tools to deploy updates across endpoints without manual intervention.
Test patches in staging before deploying to production to prevent compatibility issues.
Track patch compliance through your monitoring platform — generate reports showing which devices are current and which are behind.
Include network devices in your patch program — routers, switches, and firewalls need firmware updates too.
Monitor for zero-day vulnerabilities and have an emergency patching process ready for critical exploits.
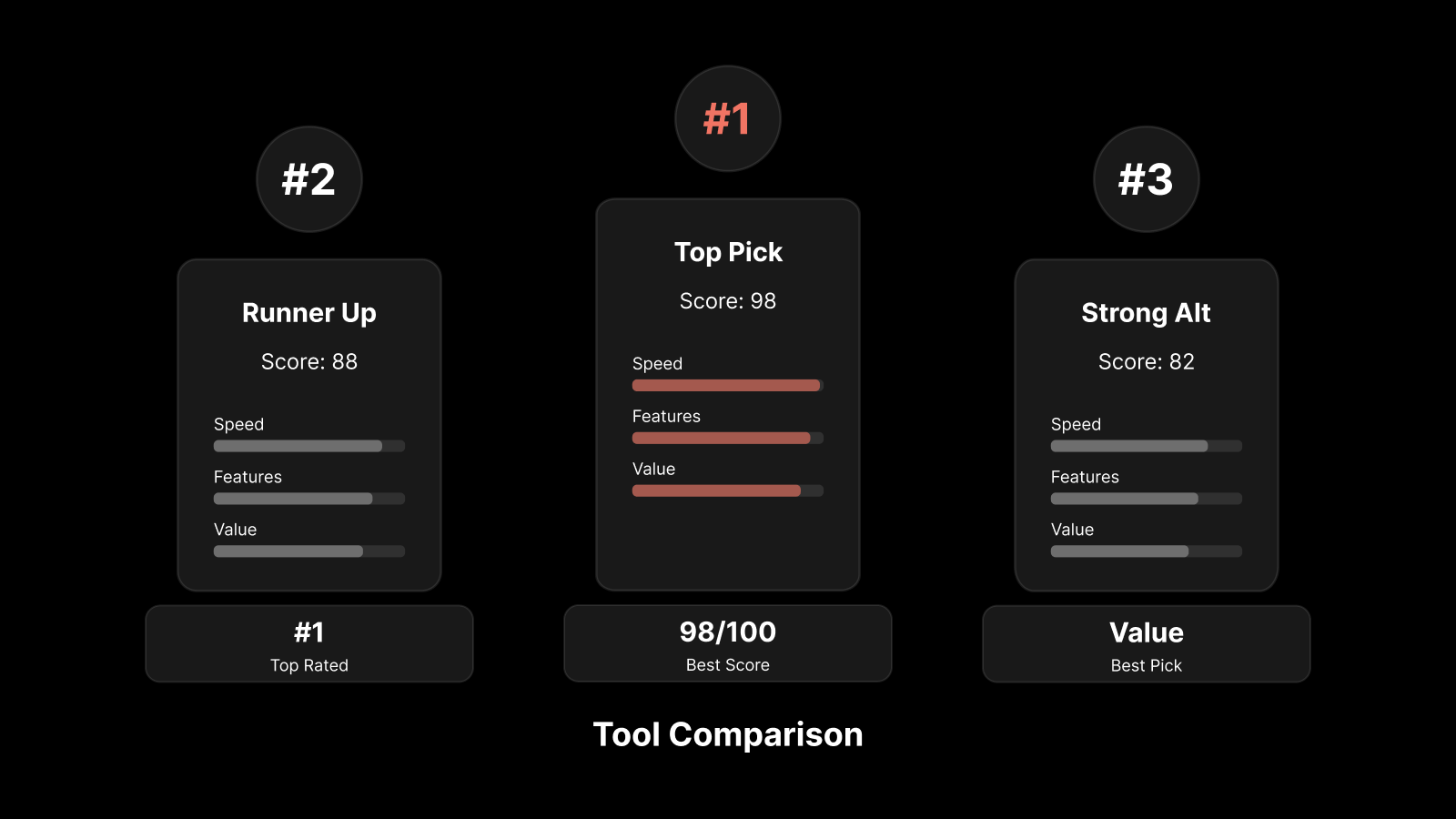
Why Motadata for Network Security Monitoring
Motadata's AI-native network monitoring platform gives your team the real-time visibility and automated detection capabilities that effective security monitoring demands. It combines network traffic analysis, device discovery, anomaly detection, and alert correlation in a single platform — with built-in integration to Motadata ServiceOps for automated incident workflows. Whether you're monitoring for performance, security, or compliance, Motadata provides the unified visibility your team needs to detect threats early and respond fast. Start a free trial and see how AI-powered monitoring strengthens your security posture.
FAQs
How does network security monitoring help protect my network?
Network security monitoring provides real-time visibility into network activities — detecting and responding to threats like unauthorized access, malware, and data breaches. It catches suspicious behavior early so your team can respond before incidents escalate.
What are the essential components of network security monitoring?
Essential components include intrusion detection/prevention systems (IDS/IPS), firewalls with logging, log management and SIEM platforms, vulnerability scanners, network traffic analysis tools, and endpoint detection and response (EDR) solutions.
How can I improve user behavior monitoring?
Implement User Activity Monitoring (UAM) tools, establish behavioral baselines for normal activity, use anomaly detection to flag deviations, and provide regular security awareness training to employees.
What is the role of threat intelligence in network security monitoring?
Threat intelligence provides insights into emerging threats and attack techniques, enabling proactive detection and response. It helps your monitoring tools recognize indicators of compromise (IoCs) and adjust detection rules based on current threat activity.
How can I raise security awareness among employees?
Conduct regular security awareness training sessions, distribute educational materials about current threats, run simulated phishing exercises, establish clear reporting procedures for suspicious activity, and recognize employees who demonstrate strong security practices.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.