How to Balance Cloud Efficiency and Security in 2026
Arpit Sharma
Balancing cloud efficiency and security means designing IT infrastructure practices that let teams move fast — scaling resources, deploying updates, adopting new tools — without creating security gaps that attackers can exploit.
What You'll Learn
Why cloud efficiency and security are complementary, not competing goals
Five strategies that protect your infrastructure without slowing your teams down
How Zero Trust, IaC, AI automation, multi-cloud strategies, and IAM work together
Where most organizations get this balance wrong
How Motadata helps teams stay productive and protected
Speed Without Safety Is Just Risk
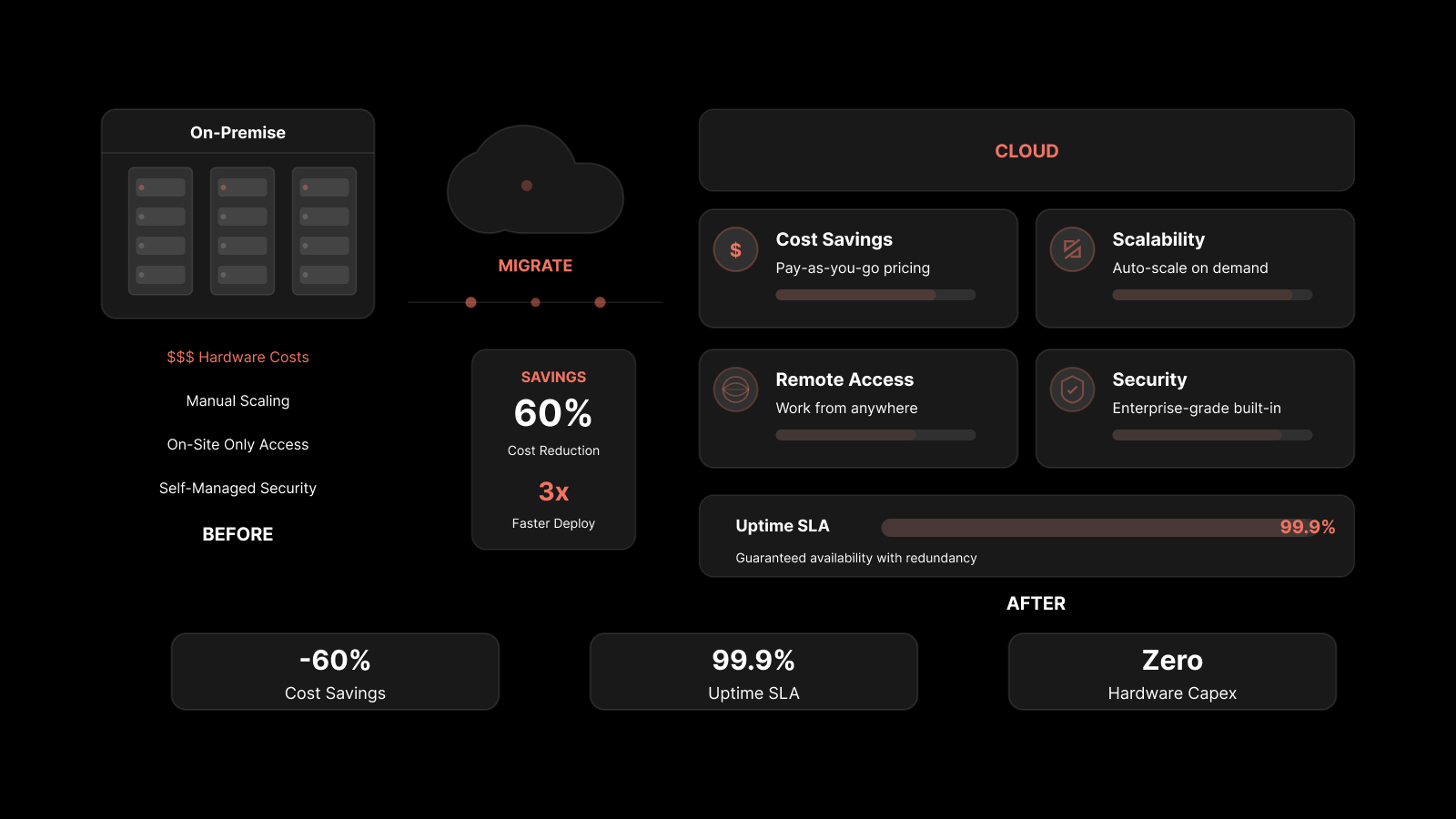
Cloud computing has fundamentally changed how IT teams operate. The scalability, flexibility, and pay-as-you-go economics of cloud platforms mean teams can spin up resources in minutes, scale on demand, and avoid the capital costs of maintaining physical hardware.
But there's a tradeoff that most organizations feel every day: the faster you move, the more access points you create. Every new cloud application, SaaS integration, and API connection is a potential entry point for attackers. As your tech stack grows, so does your attack surface.
The answer isn't to slow down. It's to build security into the way you work so that protection happens automatically — not as an afterthought that blocks progress. The organizations that get this right treat efficiency and security as two sides of the same coin.
Here are five strategies that make it work.
1. Zero Trust Security Models
Zero Trust is a security framework built on one principle: never trust, always verify. The system treats every IT request as a potential threat until it's verified. No user, device, or application is trusted by default — even if it's inside your network perimeter.
How It Works
Companies implement Zero Trust by:
Verifying every request through identity authentication and device checks
Enforcing least-privilege access — users can only interact with the resources they need for their specific task
Continuously validating sessions, not just at login
Why It Helps Both Security and Efficiency
Consider a team member who accidentally downloads malware. Without Zero Trust, that malware could spread across the network and shut down operations. With Zero Trust, the system examines every file transfer request before executing it. The threat gets contained to a single device or network segment, protecting everything else.
Zero Trust also reduces the operational burden of manual policy enforcement. By automating identity verification and centralizing access controls, it frees teams from administrative tasks so they can focus on strategic work.
In cloud environments — where users and devices change frequently — Zero Trust provides consistent protection while keeping professionals productive. The verification happens in the background, not in the way.
2. Infrastructure as Code (IaC)
Traditionally, defining servers, networks, and other resources required manual processes — technicians managing changes at data centers and company mainframes. Infrastructure as Code (IaC) replaces that manual work with code.
Teams write templates that describe their desired infrastructure state. Those templates are versioned, tested, and deployed automatically. Tools like Terraform, AWS CloudFormation, and Ansible make this possible at scale.
Efficiency Gains
IaC eliminates manual configuration. Teams can deploy infrastructure in minutes instead of days. Human error drops because machines handle the provisioning. And because everything is defined in code, setups are repeatable and consistent across environments.
Security Benefits
Every infrastructure change is tracked through version control, making rollbacks and audits straightforward. Security policies — firewall rules, access controls, encryption requirements — can be embedded directly into the code and validated during deployment.
This eliminates configuration drift: the gradual accumulation of ad hoc changes that create security gaps over time. With IaC, every deployment follows the same approved standards, keeping environments compliant and consistent.
3. AI Automation for IT Management
A typical IT infrastructure management workflow is full of repetitive tasks: handling user accounts, tracking hardware and software inventory, monitoring network performance, and reporting on compliance. AI-powered tools can handle these tasks faster and more consistently than manual processes.
What AI Automation Does
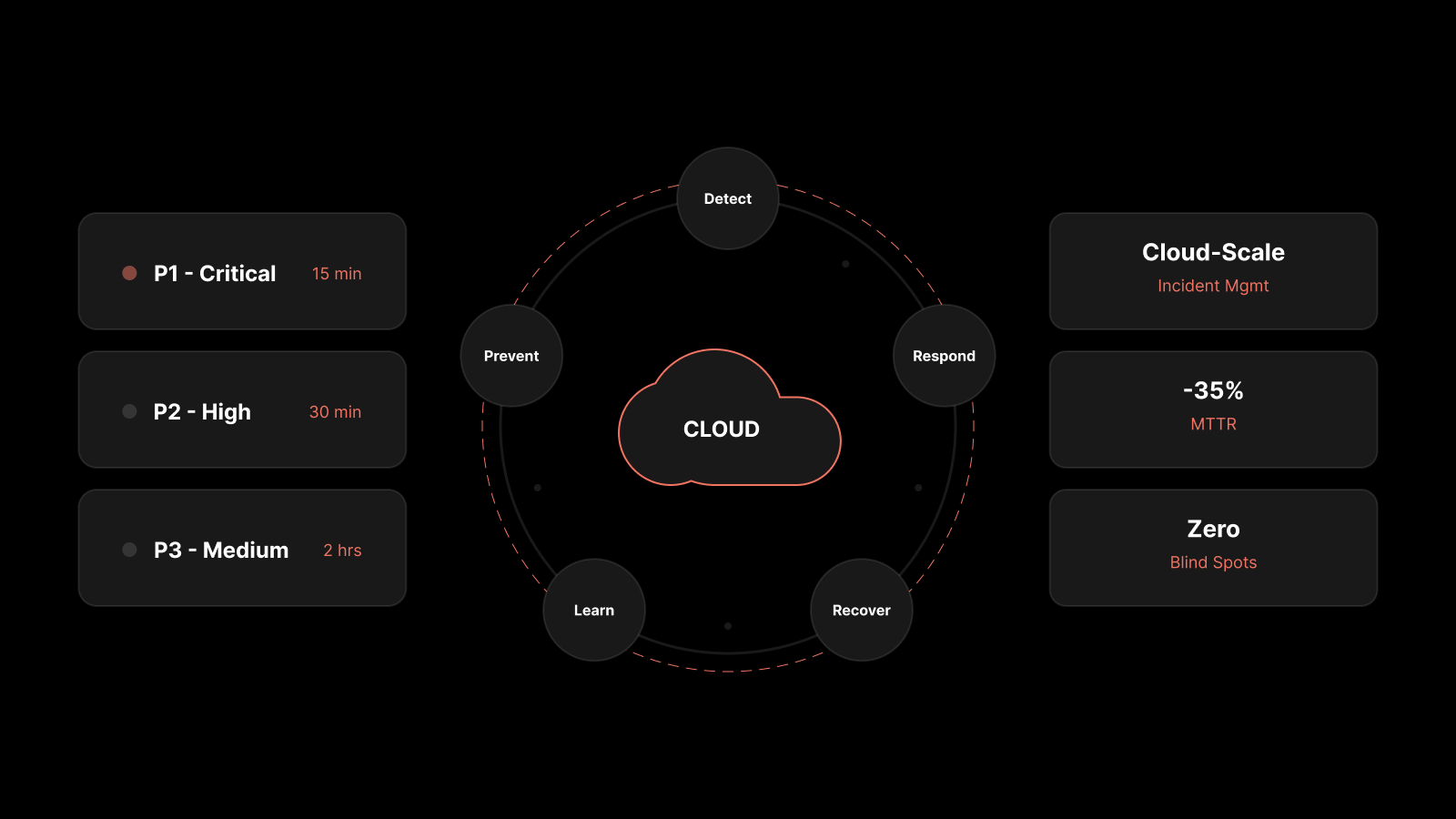
These tools analyze system logs, performance metrics, and user behavior to detect anomalies, forecast resource needs, and trigger automated remediation. For example, an AI system can identify a CPU overload, predict an impending failure, and spin up additional resources or reroute traffic — all without manual input.
The Efficiency-Security Payoff
AI automation reduces response times, minimizes downtime, and eliminates errors in routine activities. When tasks like scaling, performance tuning, and patch management are handled automatically, your team can focus on strategic priorities like architecture improvements and workflow optimization.
From a security standpoint, AI automation detects threats faster, flags suspicious activity, isolates compromised systems, and initiates response workflows instantly. And the models improve over time through continuous learning.
In complex, distributed cloud environments where manual monitoring is impractical, AI delivers both the speed and precision you need to stay efficient and protected.
4. Hybrid and Multi-Cloud Strategies
Hybrid and multi-cloud strategies combine on-premise, private, and public cloud infrastructure to power your digital workflows. This approach offers two major advantages.
Flexibility Without Lock-In
First, it lets teams pick the best tool for each job. Some applications run better on local devices; others work best through cloud-based platforms. This flexibility helps teams build the most efficient workflows possible.
Second, it prevents vendor lock-in. Instead of committing to a single provider's ecosystem, you can customize your tech stack by choosing the best option for each function. Cherry-picking tools to create a tailored stack is often more affordable than licensing a comprehensive but inflexible suite.
Security Through Distribution
A multi-cloud approach improves security because there's no single point of failure. If one provider or service is compromised, the rest of your infrastructure stays intact. Teams can quickly contain breaches by isolating the affected component and replacing it without disrupting the broader system.
This approach also helps IT teams spot anomalies faster. When you're actively managing resources across multiple providers, you develop better visibility into how each environment behaves — making unusual activity easier to identify.
The tradeoff is complexity. Managing security policies, access controls, and compliance across multiple environments requires discipline and good tooling. But the resilience and flexibility gains are worth the effort for most organizations.
5. Identity and Access Management (IAM)
Modern organizations have dozens or hundreds of users, each with multiple devices. Making sure the right people access the right resources — and nothing more — is foundational to both efficiency and security.
How IAM Works
IAM systems perform two functions: verify identity and enforce access rules.
For identity verification, they check credentials — passwords, biometrics, and multi-factor authentication (MFA) — to confirm that the person requesting access is who they claim to be.
For access enforcement, they integrate with your cloud platforms to grant each user appropriate permissions based on their role and responsibilities. Modern IAM platforms support both Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC), giving you the granularity to set policies based on roles, location, time, and device type.
Efficiency and Security Benefits
IAM automates user provisioning so new employees get access immediately, and role changes reflect instantly across all environments. This reduces friction and eliminates the manual errors that come with managing access by hand.
From a security perspective, IAM minimizes unauthorized access and monitors user activity continuously. It detects abnormal login patterns, flags suspicious behavior, and can trigger real-time alerts or account lockouts. Detailed access logs also make compliance audits faster and more reliable.
In cloud-first environments — where users access resources from various devices and locations — IAM provides the control you need without sacrificing agility or productivity.
People Also Ask
How do you balance speed and security in cloud environments?
Build security into your workflows instead of treating it as a separate process. Use Zero Trust for access control, Infrastructure as Code for consistent deployments, AI for automated threat detection, and IAM for identity management. When security is automated and embedded, it doesn't slow teams down.
What is the biggest risk of prioritizing cloud efficiency over security?
The most common result is expanded attack surface with insufficient protection. Organizations that focus only on speed tend to accumulate misconfigurations, over-privileged accounts, and unmonitored integrations — all of which are common entry points for attackers.
Is Zero Trust practical for small and mid-size businesses?
Yes. Modern Zero Trust solutions are available as cloud-based services with subscription pricing. You don't need to build the framework from scratch. Many cloud providers offer Zero Trust capabilities as part of their security packages, making it accessible for organizations of any size.
How does Infrastructure as Code improve security?
IaC embeds security policies directly into your deployment templates. Every resource is provisioned according to approved standards, and all changes are tracked through version control. This eliminates configuration drift and ensures that security requirements are enforced consistently across every environment.
Keep Your Teams Fast. Keep Your Data Safe.
Motadata's AI-native platform is built to deliver both efficiency and security in a single solution. With infrastructure monitoring for full-stack visibility, log analytics for real-time threat detection, and ServiceOps for automated patch management and workflow orchestration, your team gets the tools to move fast without cutting corners on security. No tradeoffs — just smarter operations.
See How Motadata Balances Efficiency and Security →
FAQs
Why is it hard to balance cloud efficiency and security?
Cloud environments change constantly — new resources, new integrations, new users. Each change can introduce vulnerabilities if security isn't built into the process. The challenge is maintaining protection without adding friction that slows teams down.
What role does AI play in cloud security efficiency?
AI automates repetitive security tasks like log analysis, anomaly detection, and incident response. This reduces the manual burden on IT teams while improving detection speed and accuracy — letting your team focus on strategic work instead of routine monitoring.
How does multi-cloud improve security?
Multi-cloud eliminates single points of failure. If one provider is compromised, your other environments remain protected. It also gives you flexibility to choose the most secure option for each workload and avoid vendor lock-in.
What are the first steps to balance cloud efficiency and security?
Start with an audit of your current cloud environment. Identify who has access, what's configured correctly, and where monitoring gaps exist. Then implement IAM with least-privilege access, enable MFA, and set up centralized logging. These foundational steps create the base for a balanced approach.
How does IAM support both efficiency and security?
IAM automates user provisioning and access management, reducing manual work. At the same time, it enforces least-privilege access, monitors for suspicious activity, and maintains audit logs. This combination keeps teams productive while maintaining strong controls.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.