Passwordless Authentication in ITSM & Observability: Why It Matters
Definition: Passwordless authentication is an identity verification method that replaces traditional passwords with more secure alternatives -- biometrics, hardware security keys, magic links, or device-based credentials -- to grant access to IT systems and applications.
Password resets account for 20-50% of all IT help desk tickets. Every forgotten credential burns time, drains productivity, and opens the door to social engineering attacks. Now imagine your ITSM platform and observability dashboards -- the nerve centers of your IT operations -- protected by those same fragile passwords. That's a risk most enterprises can't afford in 2026.
Passwordless authentication changes the equation. It removes the weakest link in your security chain while making life easier for IT teams and end users alike. Here's how it transforms ITSM workflows and observability security from the ground up.
What Is Passwordless Authentication and How Does It Work?
Passwordless authentication verifies user identity without requiring a memorized secret. Instead, it relies on one or more of these factors:
Biometrics: Fingerprint scanning, facial recognition, or iris scanning tied to the user's physical identity
Hardware security keys: Physical tokens (like YubiKeys) that use cryptographic challenges for verification
Device-based authentication: Certificates or keys stored on a trusted device that prove possession
Magic links and one-time codes: Time-limited tokens sent to a verified email or phone
Unlike traditional passwords, these methods resist phishing, credential stuffing, and brute-force attacks. The FIDO2/WebAuthn standard -- backed by Microsoft, Google, and Apple -- has made passwordless authentication interoperable across platforms and browsers, accelerating enterprise adoption.
The shift isn't theoretical. Microsoft reported that over 400 million accounts use passwordless sign-in options, and Gartner projects that 60% of large enterprises will implement passwordless methods across most use cases by 2027. For IT teams evaluating a transition, exploring the best passwordless authentication solutions available today can help narrow down the right approach for your enterprise environment.
Why Passwords Are Failing ITSM and Observability Teams
Traditional password-based authentication creates three persistent problems for IT operations:
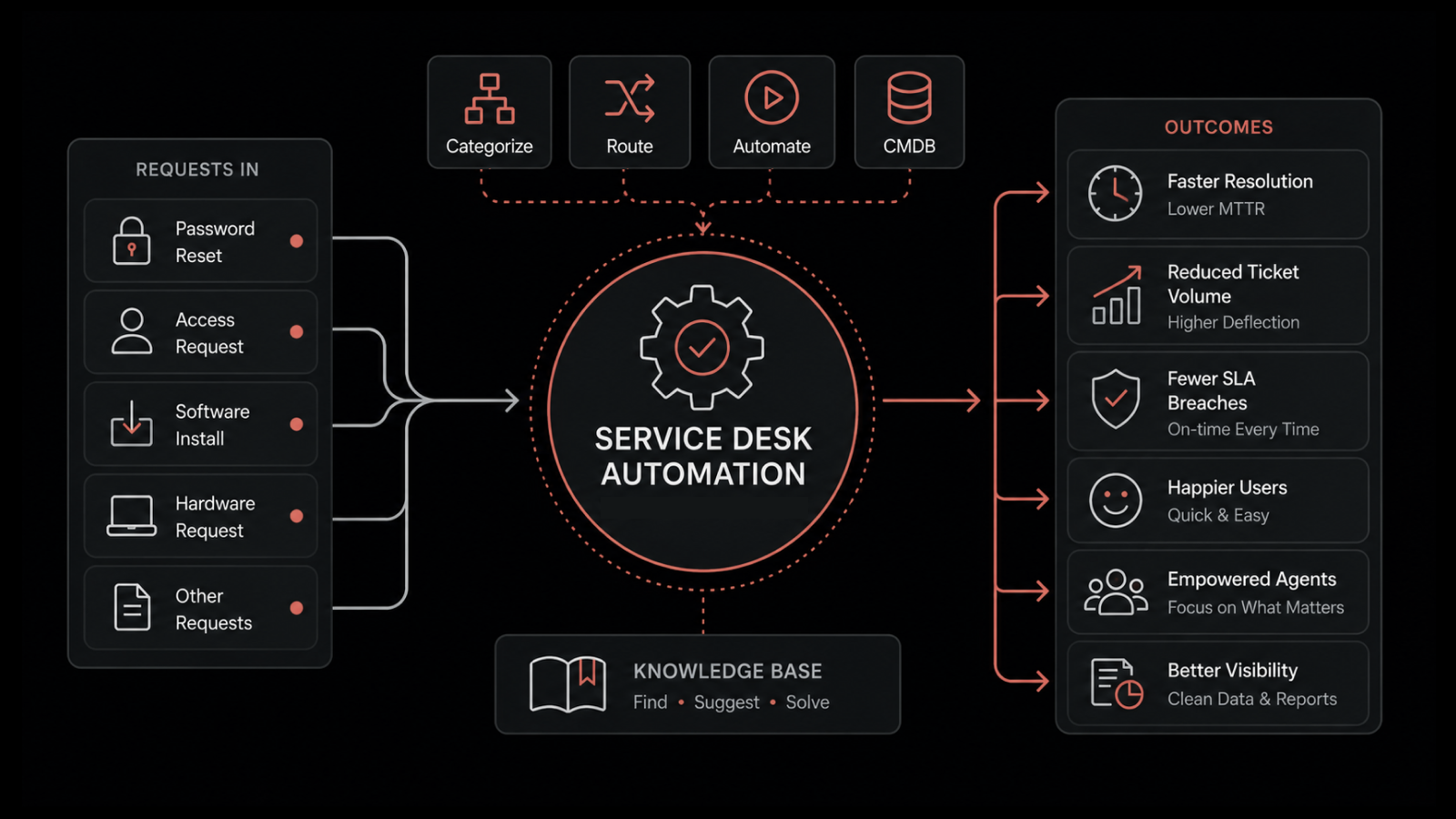
Ticket overload: Password resets and account lockouts consume help desk bandwidth that should go toward higher-value work. For ITSM teams managing hundreds or thousands of users, this is a constant drag on efficiency.
Security exposure: Verizon's Data Breach Investigations Report consistently finds that stolen or weak credentials drive the majority of breaches. When those credentials protect your ITSM platform or observability dashboards, the blast radius of a compromise expands dramatically.
Workflow friction: IT specialists and SRE teams who need rapid access to monitoring dashboards or incident management tools can't afford authentication delays. Yet strong password policies -- long strings, frequent rotation, no reuse -- create exactly that friction.
Passwordless authentication addresses all three problems simultaneously.
How Passwordless Authentication Strengthens ITSM
Integrating passwordless authentication into ITSM workflows delivers measurable improvements across several dimensions:
Reduced Ticket Volume and Faster Resolution
When employees authenticate with biometrics or hardware keys, password reset tickets disappear. IT service desk teams reclaim hours each week to focus on incident management, change requests, and strategic initiatives. The reduction in access-related tickets also improves mean time to resolution (MTTR) across the board.
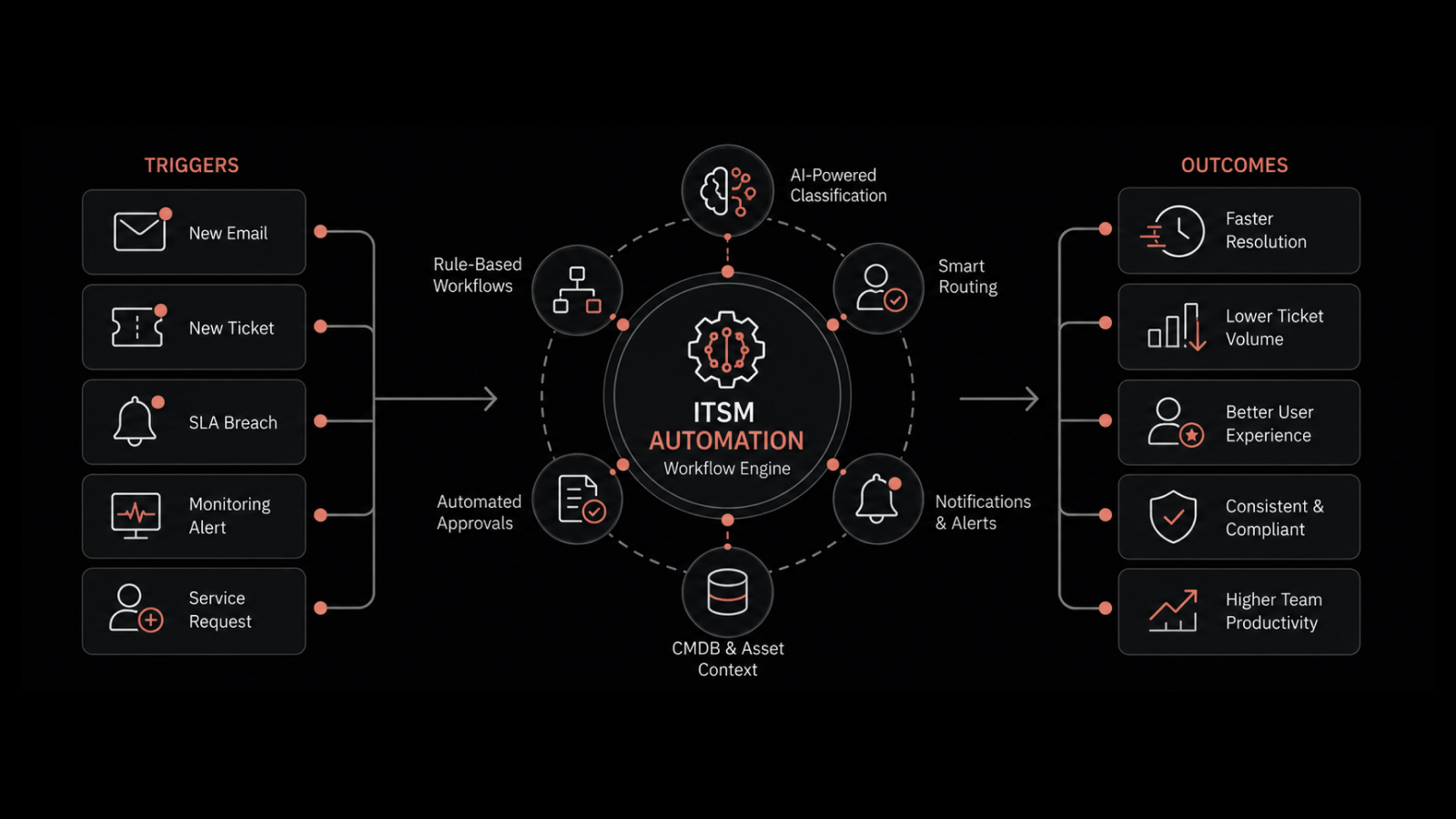
Streamlined Automation Workflows
Passwordless authentication pairs naturally with ITSM automation. Automated ticketing systems and access request workflows become more reliable when authentication is cryptographic rather than credential-based. Employees requesting access to critical resources get instantaneously authenticated through biometric scans or hardware tokens -- no manual approval bottleneck required.
Stronger Access Governance
Every authentication event in a passwordless system generates a cryptographic audit trail. ITSM platforms can log who accessed what, when, and from which device -- without the ambiguity that comes from shared or compromised passwords. This visibility supports compliance requirements and simplifies audit preparation.
Securing Observability Platforms with Passwordless Access
Observability solutions give teams visibility into infrastructure health, application performance, and security posture. They're also high-value targets. An attacker who gains access to your observability dashboards can suppress alerts, manipulate data, or map your infrastructure for deeper intrusion.
Locking Down Dashboard Access
Passwordless authentication ensures that only verified personnel reach sensitive monitoring interfaces. Device-based authentication ties access to managed endpoints, while biometric verification confirms the actual user -- not just someone who knows their password.
Supporting Zero Trust Architectures
Passwordless methods align with Zero Trust principles by verifying identity at every access request rather than relying on network-perimeter trust. For distributed observability deployments spanning cloud, on-premises, and edge environments, this approach provides consistent security without VPN dependencies.
Enabling Secure Collaboration
Distributed teams -- including remote SRE engineers, on-call responders, and third-party consultants -- need secure access to shared observability tools. Passwordless authentication lets them authenticate from any location using their registered device or biometric, maintaining security without geographical restrictions.
Behavioral Analytics: The Force Multiplier
Passwordless authentication becomes even more powerful when combined with behavioral analytics. Modern observability platforms can analyze access patterns -- login times, locations, device fingerprints, and usage behaviors -- to detect anomalies that static credentials would never catch.
For example, if a user typically accesses dashboards from a corporate laptop during business hours but suddenly authenticates from an unfamiliar device at 3 AM, the system can trigger step-up verification or block access entirely. This layered approach creates defense in depth that adapts to real-world threat patterns.
Implementation Roadmap for ITSM and Observability Teams
Rolling out passwordless authentication requires a structured approach:
Phase 1 -- Assess and Plan
Audit current authentication methods across ITSM and observability tools
Identify high-risk access points where passwords create the greatest exposure
Select passwordless methods that align with your infrastructure (FIDO2 keys, platform biometrics, or both)
Phase 2 -- Pilot and Validate
Deploy passwordless authentication for a subset of IT operations staff
Measure impact on ticket volume, authentication speed, and user satisfaction
Validate integration with existing ITSM platforms and observability tools
Phase 3 -- Scale and Optimize
Expand to all IT personnel, then to broader employee populations
Integrate with behavioral analytics for adaptive authentication
Establish policies for device registration, recovery flows, and exception handling
Phase 4 -- Monitor and Iterate
Track authentication success rates, security incident trends, and user feedback
Update policies based on evolving threat intelligence
Evaluate emerging standards and methods for continuous improvement
Future Trends Shaping Passwordless Authentication
The passwordless landscape continues to evolve rapidly:
Passkeys: Apple, Google, and Microsoft are pushing passkeys as the successor to passwords, enabling cross-device authentication with built-in phishing resistance
Continuous authentication: AI-driven systems that verify identity throughout a session based on behavioral signals, not just at login
Decentralized identity: Blockchain-based credential systems that give users control over their identity data while eliminating centralized credential stores
Adaptive MFA: Context-aware systems that adjust authentication requirements based on risk level, resource sensitivity, and real-time threat intelligence
These trends point toward a future where authentication is invisible, continuous, and deeply integrated into ITSM and observability workflows.
People Also Ask
Does passwordless authentication work with existing ITSM platforms?
Yes. Most modern ITSM platforms support SAML, OAuth 2.0, and OpenID Connect, which are the protocols passwordless solutions use for integration. Platforms like Motadata's ITSM suite support standards-based authentication that works with FIDO2 keys and biometric providers.
Is passwordless authentication more secure than MFA?
Passwordless authentication and MFA aren't mutually exclusive. Passwordless methods can serve as strong single factors (biometrics, hardware keys), and they can also combine with additional factors for high-security scenarios. The key advantage is eliminating the password itself, which removes the most commonly exploited attack vector.
What happens if a user loses their hardware security key?
Organizations establish recovery procedures during implementation -- typically involving a backup key, administrator-assisted re-enrollment, or temporary access through a verified alternative method. Proper planning ensures lost keys don't create access emergencies.
How does passwordless authentication reduce IT costs?
By eliminating password resets (which cost $50-70 per ticket on average), reducing breach-related expenses, and freeing help desk staff for higher-value work. Organizations typically see ROI within the first year of deployment.
Strengthen Your ITSM and Observability Security with Motadata
Motadata's AI-native platform brings unified observability and IT service management together on a single pane of glass. With support for modern authentication standards, automated workflows, and intelligent incident management, Motadata helps enterprises eliminate security friction while gaining deeper operational visibility.
Ready to modernize your IT operations? Explore Motadata's ITSM platform or discover unified observability to see how passwordless-ready infrastructure transforms your security posture.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.