DevOps Security: Why It Matters, Key Practices, and How to Get It Right
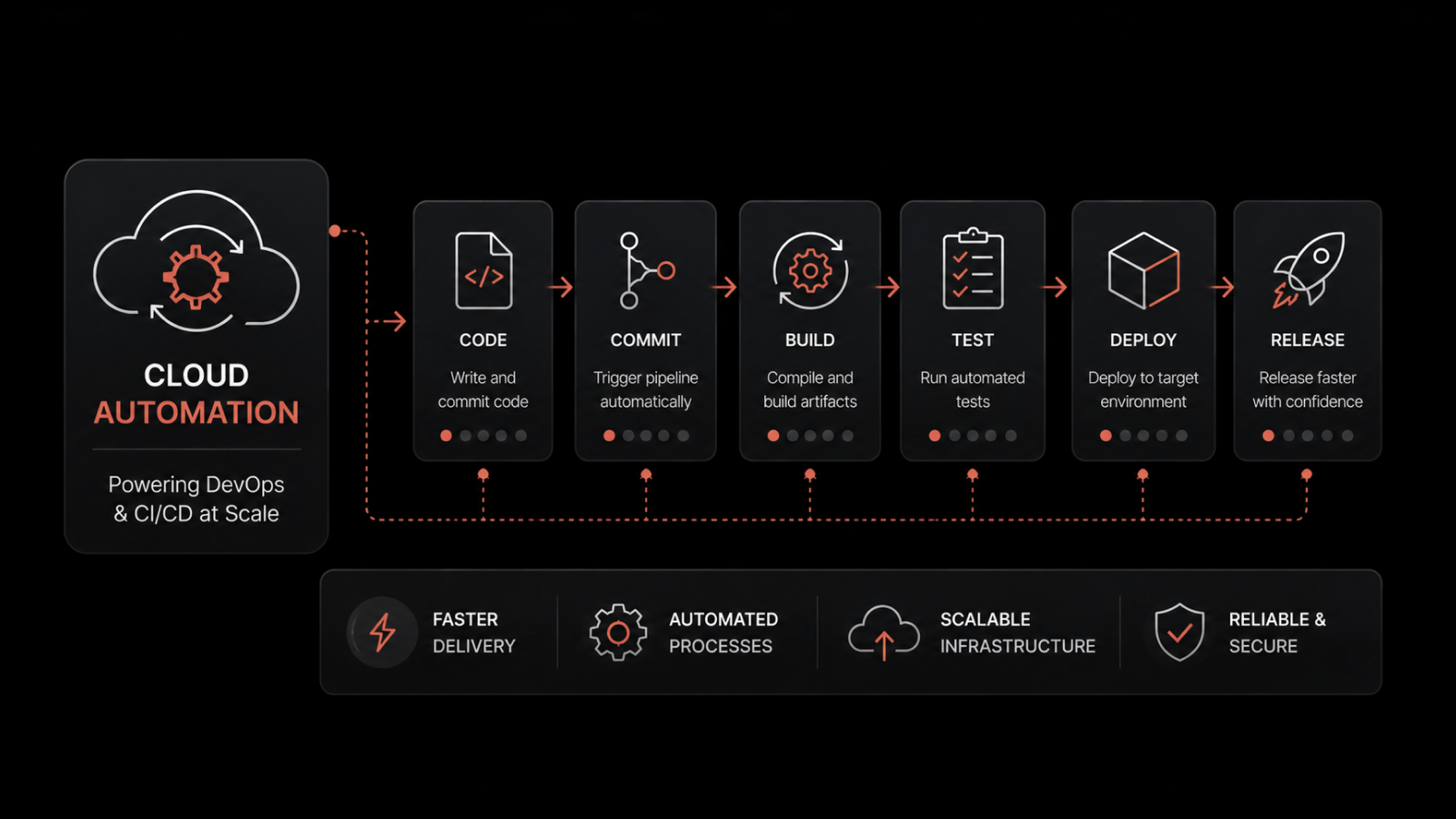
DevOps security is the practice of integrating security testing, controls, and policies directly into every stage of the software development lifecycle -- from code commit to production deployment -- rather than treating security as a separate, end-of-pipeline gate.
A development team ships 15 releases per week. They've automated testing, streamlined deployments, and cut lead time by 80%. But last quarter, a credential leak in a container image exposed customer payment data for 72 hours before anyone noticed.
Speed without security isn't velocity -- it's liability. That's the core argument for DevOps security: the faster you ship, the more important it becomes to embed security into the process itself rather than bolt it on afterward.
What Is DevOps Security?
DevOps security is about building security into your development and deployment workflows from the start. Instead of running security scans after code is written and deployed, you integrate automated security testing into every stage of your CI/CD pipeline.
This means vulnerability scanning happens during the build. Dependency checks run before code merges. Access controls are enforced through infrastructure as code. And security monitoring continues in production, catching threats that pre-deployment testing can't anticipate.
The underlying principle is straightforward: if your team deploys multiple times per day, you can't rely on periodic security reviews. Security has to move at the same speed as development, and the only way to achieve that is through automation and integration.
Why DevOps Security Matters
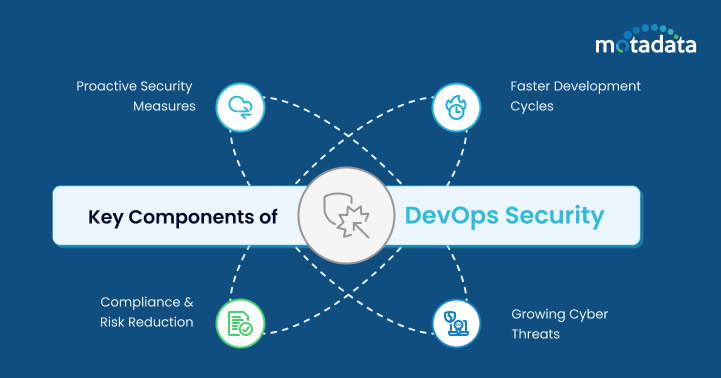
Faster Pipelines Create Bigger Attack Surfaces
Automation has compressed development cycles from months to days. That's a massive gain in delivery speed, but it also means vulnerabilities reach production faster. A coding flaw that would have been caught during a two-week manual QA cycle now ships to production in hours.
DevOps security addresses this by inserting automated security gates into the pipeline. Static analysis scans code for vulnerabilities during the build. Dynamic testing validates running applications during staging. The pipeline doesn't slow down -- it just doesn't let vulnerable code pass through.
The Cost of Late-Stage Security Fixes
Finding and fixing a vulnerability during development costs a fraction of what it costs in production. IBM's research consistently shows that production-stage fixes cost 6-15x more than fixes during development. When you add incident response costs, customer notification requirements, and potential regulatory fines, the economics of shift-left security become overwhelming.
Compliance Is a Continuous Requirement
Regulated industries can't treat compliance as a checkpoint. Standards like SOC 2, HIPAA, PCI DSS, and GDPR require evidence of ongoing security controls, not just point-in-time audits. Embedding compliance checks into your pipeline produces continuous compliance evidence and reduces the effort required for audits.
Threat Landscape Keeps Evolving
Cyber threats don't wait for your next security review cycle. New vulnerabilities are disclosed daily, supply chain attacks target development tools themselves, and attackers actively scan for the kinds of misconfigurations that fast-moving teams introduce. Proactive, automated security is the only approach that matches the pace of modern threats.
Core Security Practices for DevOps Teams
Shift-Left Security Testing
Shift-left means moving security testing as early as possible in the development lifecycle. The earlier you catch a vulnerability, the cheaper and faster it is to fix.
Static Application Security Testing (SAST): Analyzes source code for vulnerabilities without executing it. Catches SQL injection, insecure API calls, and hardcoded credentials during the build.
Dynamic Application Security Testing (DAST): Tests running applications for vulnerabilities like cross-site scripting (XSS), authentication flaws, and injection attacks during staging.
Interactive Application Security Testing (IAST): Combines SAST and DAST by instrumenting live applications to detect vulnerabilities in real time during testing.
Software Composition Analysis (SCA): Scans third-party dependencies and open-source libraries for known vulnerabilities and licensing issues.
Secure Coding Standards
Security starts with the code itself. Establish coding standards that address common vulnerabilities:
Input validation and output encoding to prevent injection attacks
Proper authentication and session management
Secure error handling that doesn't expose internal details
Parameterized queries instead of string concatenation for database access
Regular secure coding training keeps developers current on emerging vulnerability patterns and reinforces security as a development responsibility, not just a security team concern.
Secret Management
Hardcoded credentials in source code are one of the most common -- and most preventable -- security failures. Implement a secret management strategy that includes:
Centralized secret storage (HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault)
Environment variables for runtime secrets
Automated secret rotation
Pre-commit hooks that block credential commits
Role-based access controls that limit who can access which secrets
Infrastructure as Code (IaC) Security
When infrastructure is defined as code, it should be scanned like code. IaC security scanning catches misconfigurations -- open security groups, unencrypted storage, overly permissive IAM policies -- before they're deployed.
Tools like Checkov, tfsec, and AWS CloudFormation Guard validate infrastructure definitions against security policies automatically. This prevents the configuration drift that introduces vulnerabilities in production environments.
Pipeline Security
The CI/CD pipeline itself is an attack surface. If an attacker compromises your build system, they can inject malicious code into every deployment. Secure your pipeline by:
Enforcing signed commits and verified builds
Implementing least-privilege access for pipeline service accounts
Scanning container images for vulnerabilities before deployment
Validating software bill of materials (SBOM) for supply chain integrity
Isolating build environments from production infrastructure
Monitoring and Runtime Security
Pre-deployment testing catches known vulnerability patterns. Runtime security monitoring catches everything else -- zero-day exploits, configuration drift, unusual access patterns, and threats that only manifest in production.
Continuous Monitoring
Implement real-time monitoring across all production environments to detect:
Unauthorized access attempts
Unusual API call patterns
Configuration changes outside approved change windows
Resource consumption anomalies that may indicate cryptomining or data exfiltration
Network traffic to known malicious endpoints
Logging and Audit Trails
Comprehensive logging provides the forensic data you need to investigate incidents and demonstrate compliance. Log all authentication events, configuration changes, data access, and administrative actions. Store logs in tamper-proof, centralized systems with appropriate retention policies.
Identity and Access Management (IAM)
Implement least-privilege access across all environments. Use role-based access controls that grant team members only the permissions they need for their specific responsibilities. Enforce multi-factor authentication for all privileged accounts. Regularly audit access grants and revoke permissions that are no longer needed.
Common DevOps Security Challenges
Balancing Speed and Security
This is the defining tension of DevOps security. Development teams optimize for delivery speed; security teams optimize for risk reduction. The solution isn't compromise -- it's automation. When security tests run automatically in the pipeline, they don't slow development down. They just prevent insecure code from progressing.
Cultural Resistance to Shared Responsibility
DevSecOps requires developers, operations engineers, and security professionals to share responsibility for security. Some team members resist this shift, especially developers who view security as someone else's problem. Executive sponsorship, clear role definitions, and integrated tooling help drive cultural adoption.
Security Skill Gaps
Not every developer has deep security expertise, and not every security professional understands modern development workflows. Bridge this gap with:
Regular security training tailored to development teams
Security champions programs that embed security advocates within development teams
Automated tools that provide actionable remediation guidance, not just vulnerability reports
Securing Cloud-Native Environments
Containers, Kubernetes, serverless functions, and microservices introduce new security considerations that traditional security tools don't address. Container image scanning, runtime protection, network policy enforcement within Kubernetes clusters, and function-level access controls all require specialized approaches.
Supply Chain Security
The SolarWinds and Log4j incidents demonstrated that attackers increasingly target the software supply chain. Securing your pipeline, validating dependencies, generating and verifying SBOMs, and monitoring for compromised packages are now essential practices.
DevOps Security Tools
Category | Tools | Purpose |
|---|---|---|
SAST | SonarQube, Checkmarx, Semgrep | Static code analysis for vulnerabilities |
DAST | OWASP ZAP, Burp Suite | Runtime application vulnerability scanning |
SCA | Snyk, Dependabot, FOSSA | Open-source dependency vulnerability scanning |
IaC Scanning | Checkov, tfsec, Terrascan | Infrastructure-as-code security validation |
Secret Detection | GitLeaks, TruffleHog | Pre-commit credential scanning |
Container Security | Aqua Security, Trivy, Prisma Cloud | Container image and runtime scanning |
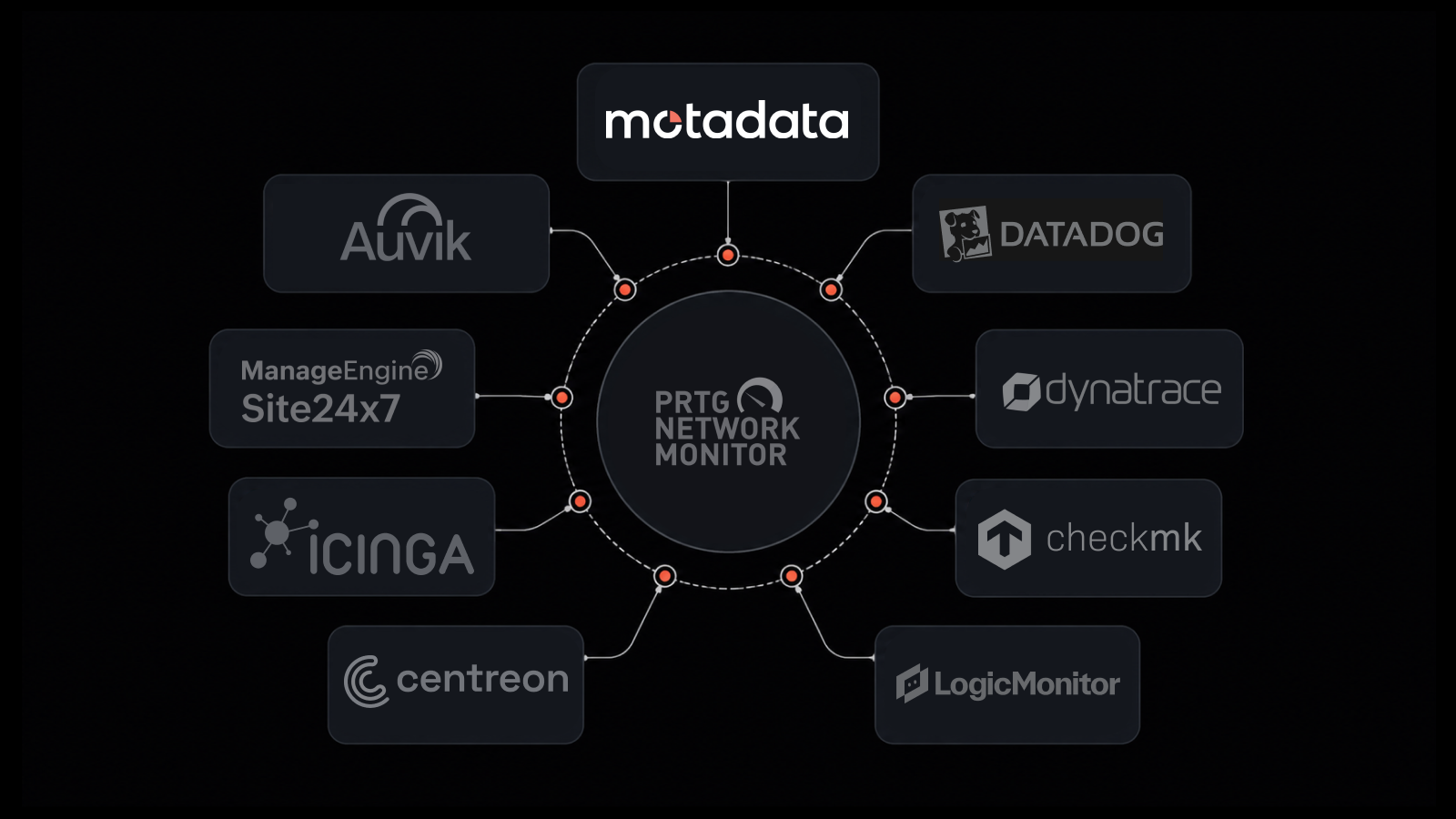
Monitoring | Motadata, Prometheus + Grafana | Runtime security monitoring and alerting |
People Also Ask: DevOps Security
What's the difference between DevOps and DevSecOps?
DevOps integrates development and operations to accelerate software delivery. DevSecOps adds security as a first-class concern throughout that process. In practice, DevSecOps means automated security testing in the pipeline, shared security responsibility across teams, and continuous security monitoring in production. It's not a separate practice -- it's DevOps done with security built in from the start.
What does "shift left" mean in DevOps security?
Shift left means moving security activities earlier in the development lifecycle -- from post-deployment testing to pre-commit scanning. The earlier you find a vulnerability, the less it costs to fix and the lower the risk of it reaching production. SAST, SCA, and pre-commit hooks are all shift-left practices.
How do you secure a CI/CD pipeline?
Secure your pipeline by enforcing signed commits, implementing least-privilege access for service accounts, scanning container images before deployment, validating dependencies against known vulnerability databases, isolating build environments, and maintaining audit logs of all pipeline activities. The pipeline is infrastructure -- treat it with the same security rigor as your production environment.
Can DevOps security work without slowing down development?
Yes, when security is automated. Automated SAST, DAST, and SCA tools run as pipeline stages that execute in seconds to minutes. They don't add manual delays -- they add automated quality gates. The key is tuning tools to minimize false positives so developers trust the results and don't start ignoring alerts.
How Motadata Supports DevOps Security
Shipping code fast is only half the equation. You also need continuous visibility into what's running in production, how it's behaving, and whether anything looks suspicious. Motadata's AI-native DevOps monitoring platform gives your team real-time observability across applications, infrastructure, containers, and network layers.
With intelligent alerting, automated anomaly detection, and deep integration with your deployment workflow, Motadata helps you catch security issues that pre-deployment testing misses. Monitor configuration changes, track access patterns, detect unusual traffic, and correlate events across your entire stack -- all from a unified platform.
Start a free trial to see how Motadata brings security observability to your DevOps pipeline.
FAQs
What is DevOps security?
DevOps security is the practice of embedding security testing, controls, and monitoring into every stage of the software development and deployment lifecycle. It replaces the traditional model of testing for security at the end of development with continuous, automated security validation throughout the pipeline.
Why is security important in DevOps?
Speed amplifies risk. The faster you deploy, the faster vulnerabilities reach production if you don't catch them in the pipeline. DevOps security ensures that increased deployment frequency doesn't come at the cost of increased exposure to threats.
What role do monitoring and logging play in DevOps security?
Monitoring provides real-time visibility into production security -- detecting unauthorized access, configuration drift, and anomalous behavior that pre-deployment testing can't catch. Logging creates the audit trail needed for incident investigation, compliance evidence, and post-incident analysis.
How does DevOps impact security?
DevOps increases deployment frequency, which creates more opportunities for vulnerabilities to reach production. But DevOps also enables automated security testing at every pipeline stage, faster patching cycles, and infrastructure-as-code security scanning -- practices that strengthen overall security posture when implemented correctly.
What role does DevSecOps play in DevOps security?
DevSecOps transforms security from an external review function into an integrated part of every team's workflow. It ensures that developers, operations engineers, and security professionals share ownership of security outcomes, and that security testing happens continuously rather than periodically.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.