Cloud Monitoring for Cybersecurity: Why It Matters in 2026
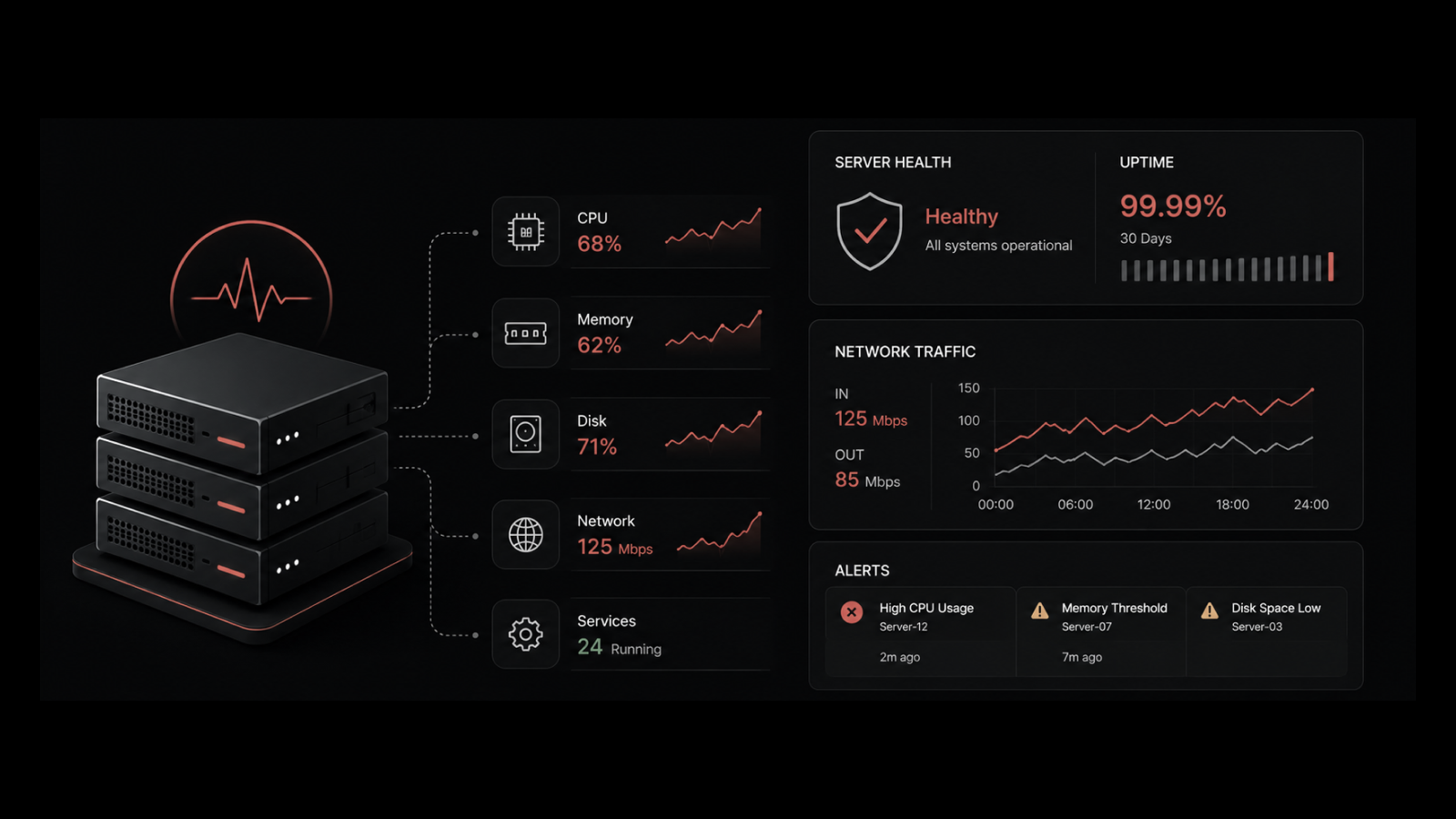
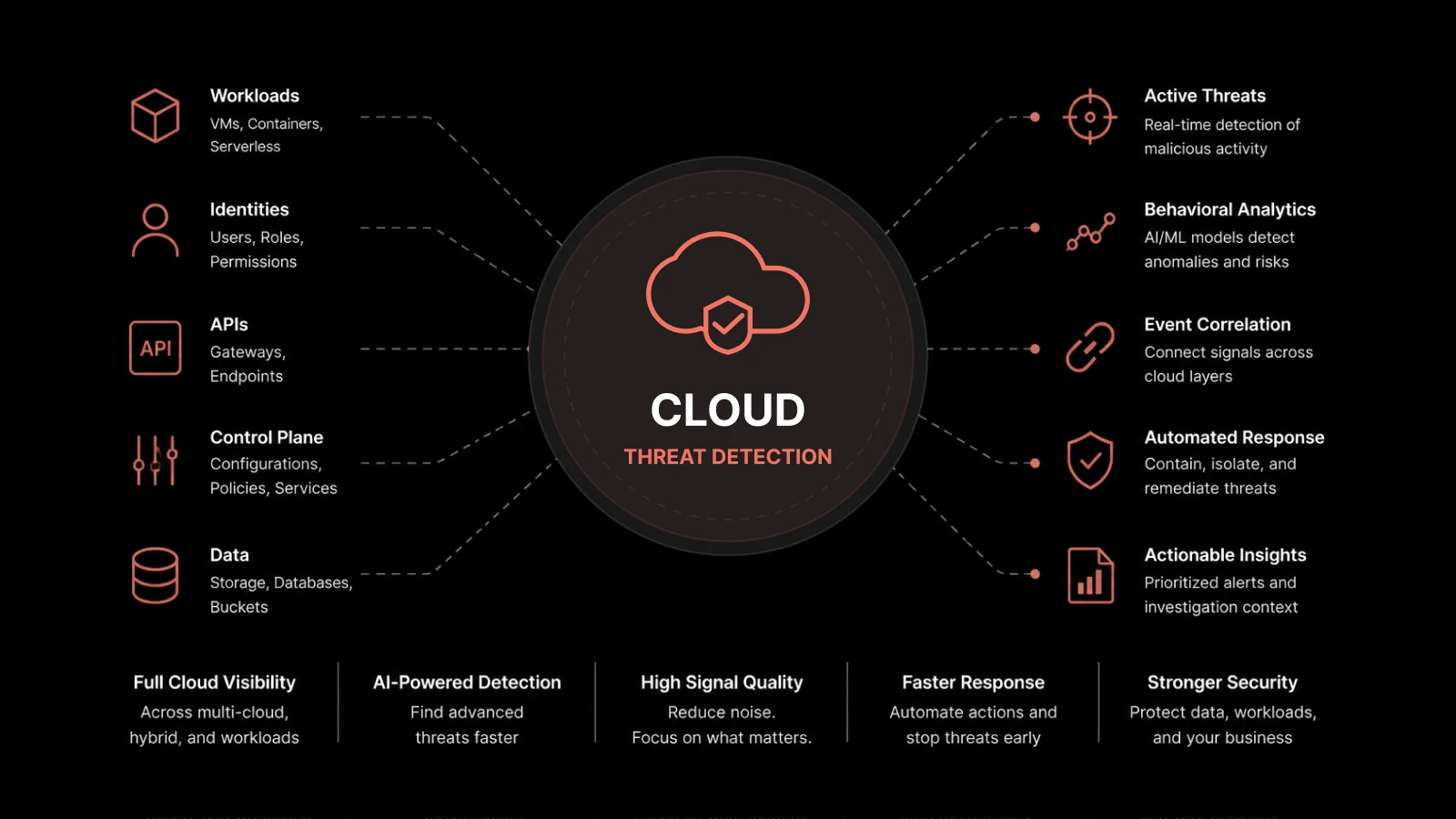
Cloud monitoring for cybersecurity is the continuous observation and analysis of cloud infrastructure, applications, and network activity to detect threats, prevent unauthorized access, and maintain compliance with security standards.
What You'll Learn
Why cloud monitoring has become a top cybersecurity priority
How real-time monitoring prevents breaches and reduces incident response times
The connection between cloud monitoring and business functions like operations and customer trust
How AI and automation are transforming cloud security monitoring
Practical steps to implement cloud monitoring in your organization
How Motadata's platform delivers the visibility your security team needs
Your Cloud Is Only as Secure as Your Visibility
Organizations across every industry are moving data, applications, and operations to the cloud. This migration delivers real benefits — better scalability, improved collaboration, and lower infrastructure costs. But it also creates new attack surfaces that didn't exist in traditional data center environments.
Hackers target cloud systems specifically because they're often repositories of sensitive customer data, financial information, and intellectual property. And the dynamic nature of cloud environments — where resources scale up and down constantly — makes it easy for misconfigurations, unauthorized access, and suspicious traffic to go undetected.
Cloud monitoring is what closes that gap. By continuously tracking cloud infrastructure, applications, and networks, organizations can catch abnormal activity, block intrusions, and prove compliance with regulatory requirements. Without it, you're operating with blind spots — and attackers are always looking for exactly those blind spots.
Why Cloud Monitoring Is Now a Business Priority
Traditional data centers are relatively static. Cloud environments are not. Resources scale automatically, new services spin up daily, and configurations change with every deployment. Each new virtual machine, container, or API endpoint is a potential access point.
Without real-time monitoring, companies can miss misconfigurations, unauthorized access attempts, or suspicious network traffic — sometimes for weeks or months before the damage surfaces.
On top of that, regulations like GDPR, HIPAA, and PCI-DSS require organizations to demonstrate control over cloud-stored data. Monitoring provides the transparency regulators demand: who accessed what data, when, and from where.
For these reasons, cloud monitoring has moved from an IT nice-to-have to a board-level priority. It's the foundation that the rest of your security strategy is built on.
How Cloud Monitoring Connects to Business Operations
Cloud security isn't isolated from the rest of your business. A compromised cloud environment can take down sales platforms, disrupt financial transactions, and expose customer communications.
Consider your customer-facing systems — CRM, email marketing tools, e-commerce platforms. If attackers gain access to these systems through a cloud vulnerability, they don't just steal data. They can impersonate your brand, damage customer relationships, and trigger regulatory penalties.
Cloud monitoring protects the infrastructure that these business tools depend on. By maintaining visibility into the health and security of your cloud environment, you're protecting not just IT systems but revenue, reputation, and customer trust.
Dealing with an Expanding Threat Environment
Cyber threats have grown more sophisticated alongside cloud adoption. Attackers use techniques like credential stuffing, ransomware, supply chain exploits, and advanced persistent threats to breach cloud environments.
Real-time monitoring provides a defense layer by:
Detecting abnormal traffic and user behavior before it causes damage
Spotting unauthorized access attempts and blocking them in real time
Tracking suspicious API calls or configuration changes that indicate compromise
Alerting security teams about potential malware or data exfiltration
This shifts your security posture from reactive to preventive. Instead of investigating breaches after they've happened, your team can catch and contain threats while they're still developing.
Cost Savings Through Proactive Protection
Cybersecurity spending often feels like a cost center — until you compare it to the price of a breach. Data loss, regulatory penalties, legal fees, and reputational damage can add up to millions. IBM's latest research puts the average breach cost at $4.45 million.
Proactive monitoring reduces this risk in measurable ways:
Early detection means smaller incidents with less damage
Automated alerting reduces the need for large 24/7 security teams
Resource optimization identifies wasteful or misconfigured cloud resources before they become liabilities
Compliance automation reduces the manual effort of audit preparation
Organizations that invest in prevention consistently spend less than those forced into recovery mode. The ROI of monitoring isn't theoretical — it shows up directly in avoided costs and operational efficiency.
Supporting Remote and Hybrid Work
Remote and hybrid work models have expanded cloud adoption dramatically. Employees access company data and applications from personal devices, home networks, and public Wi-Fi — each one a potential vulnerability.
Cloud monitoring gives security teams the visibility to manage this complexity:
Verify that access follows authorized patterns
Detect and flag unusual login activity (new locations, unusual hours, multiple simultaneous sessions)
Enforce consistent security policies across all environments, regardless of where users connect from
This approach keeps data secure without restricting the flexibility that remote workers need. You protect the perimeter without building walls that block productivity.
Faster Incident Response
Even with strong preventive measures, incidents happen. What separates resilient organizations from vulnerable ones is how quickly they detect and contain threats.
Cloud monitoring accelerates incident response by providing:
Detailed logs that trace the timeline of an incident
Real-time alerts that trigger as soon as anomalies are detected
Automated workflows that initiate containment procedures without waiting for manual intervention
When your security team can identify the root cause within minutes instead of hours, the damage stays contained. Faster response also sends a clear message to stakeholders, customers, and regulators that your organization takes security seriously.
Building Trust with Customers and Partners
Trust is a business asset. Customers need confidence that their data is protected. Partners need assurance that shared systems are secure. Inability to demonstrate strong security practices leads to lost business and damaged reputation.
Organizations with active cloud monitoring can demonstrate their commitment to data protection through:
Documented monitoring practices and incident response procedures
Compliance certifications backed by continuous audit evidence
Transparent security reporting to stakeholders
In data-sensitive industries — healthcare, finance, government — this trust is a competitive differentiator. Companies that can prove they monitor and protect their cloud environments win business over those that can't.
AI and Automation in Cloud Monitoring
AI and automation are transforming how cloud monitoring works. Modern monitoring tools can analyze thousands of events per second, spot patterns that humans would miss, and trigger response actions in real time.
For example, an AI system can:
Review thousands of access requests simultaneously to identify anomalous behavior — like a user logging in from two locations at once
Automatically trigger security measures such as account lockouts or system isolation
Learn from historical data to improve detection accuracy over time
Pairing AI with cloud monitoring gives your team a security capability that scales with your environment. As your cloud footprint grows, AI ensures your monitoring keeps pace without requiring proportional increases in headcount.
Preparing for What's Next
Multi-cloud and hybrid environments are becoming the norm, and the complexity of managing security across multiple providers, services, and integrations will only increase. Emerging technologies like edge computing, IoT, and 5G will add new layers of risk.
Cloud monitoring will evolve alongside these trends, delivering new capabilities for managing distributed infrastructure and securing endpoints at the edge. Organizations that build strong monitoring foundations today will be better positioned to adapt as the threat environment changes.
Get the Visibility Your Security Team Needs
Motadata's AI-native cloud monitoring platform gives your team real-time visibility across your entire cloud environment. With built-in anomaly detection, log analytics, automated alerting, and network monitoring, you can catch threats early, respond fast, and maintain compliance — without drowning in alerts. Pair it with Motadata ServiceOps for automated incident workflows and patch management, and you've got a monitoring-to-resolution pipeline that works at cloud speed.
Start Monitoring with Motadata →
FAQs
Why is cloud monitoring important for cybersecurity?
Cloud environments are dynamic — resources scale constantly, configurations change with every deployment, and users connect from anywhere. Without continuous monitoring, misconfigurations, unauthorized access, and suspicious activity can go undetected for weeks. Monitoring provides the real-time visibility that every other security control depends on.
How does real-time cloud monitoring reduce breach costs?
Early detection means smaller incidents. When monitoring catches a threat in its early stages, your team can contain it before data is exfiltrated, systems are encrypted, or operations are disrupted. Organizations with strong detection and response capabilities consistently report lower breach costs than those without.
What should you look for in a cloud monitoring tool?
Look for real-time alerting, support for multi-cloud environments, AI-powered anomaly detection, integration with your existing security stack, compliance reporting capabilities, and customizable dashboards. The tool should scale with your environment and reduce alert fatigue through intelligent filtering.
How does cloud monitoring support remote work security?
Cloud monitoring tracks access patterns, detects unusual login behavior, and enforces consistent security policies regardless of where users connect from. This gives security teams visibility into remote access without restricting employee flexibility.
What's the relationship between cloud monitoring and incident response?
Cloud monitoring is the foundation of incident response. It provides the real-time alerts that trigger response workflows, the detailed logs that help teams investigate root causes, and the historical data that supports post-incident analysis and prevention planning.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.