7 Benefits of Cloud SIEM Solutions (2026 Guide)
Definition
Cloud SIEM (Security Information and Event Management) is a cloud-hosted security platform that collects, correlates, and analyzes log data from across your IT environment — without requiring on-premises hardware. It provides real-time threat detection, incident response capabilities, and compliance reporting as a managed service.
Hook
Security teams are stretched thin. Threats are growing faster than headcounts, and budgets aren't keeping up. According to IBM's 2025 Cost of a Data Breach report, the average breach now costs $4.88 million — and organizations using security AI and automation save an average of $2.22 million per incident. Traditional on-premises SIEM promised to be the answer, but months-long deployments, hardware lock-in, and manual threat intelligence updates have turned many SIEM projects into resource drains. Cloud SIEM flips that equation. It delivers the same security intelligence without the infrastructure burden that holds teams back.
What Is Cloud SIEM and How Does It Work?
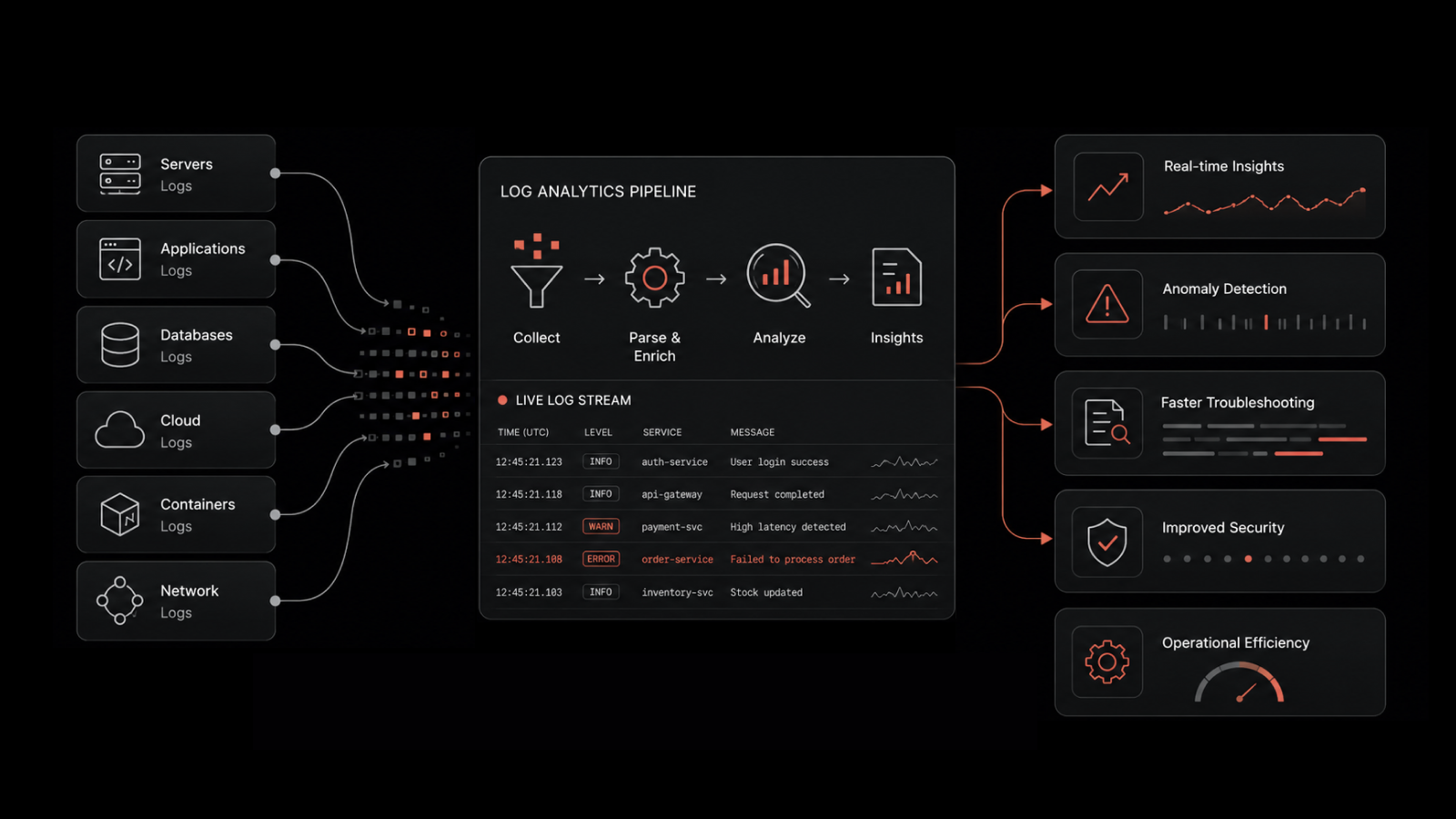
Cloud SIEM takes the core functions of traditional SIEM — log collection, event correlation, threat detection, and incident response — and delivers them from a cloud-hosted platform. Instead of deploying servers, storage arrays, and networking gear in your data center, you connect your log sources to the provider's infrastructure and start ingesting security data.
The architecture typically works like this: agents or API integrations forward logs from your firewalls, endpoints, identity providers, cloud workloads, and applications to the cloud SIEM platform. The platform normalizes, indexes, and correlates that data against threat intelligence feeds and detection rules. When it identifies suspicious patterns, it generates alerts and provides investigation workflows for your security team.
This model shifts the heavy lifting — hardware provisioning, software updates, scaling, and threat intelligence maintenance — to the provider. Your team focuses on what matters: detecting and responding to threats.
On-Premises SIEM vs. Cloud SIEM: Key Differences
Factor | On-Premises SIEM | Cloud SIEM |
|---|---|---|
Deployment Time | 3-6+ months | Days to weeks |
Cost Model | Large upfront CapEx + ongoing maintenance | Monthly/annual subscription (OpEx) |
Scaling | Manual hardware procurement and setup | Automatic, on-demand scaling |
Threat Intelligence | Manual rule updates by internal team | Provider-managed, continuous updates |
Infrastructure Management | Fully owned by your IT/security team | Managed by provider |
Remote Access | VPN-dependent, often slow | Browser-based, location-independent |
Integration Maintenance | Custom connectors require ongoing work | Pre-built integrations maintained by provider |
Understanding these differences makes the benefits of cloud SIEM concrete rather than abstract.
1. Faster Deployment Means Faster Protection
Traditional SIEM implementations take three to six months — sometimes longer. Between hardware procurement, data center setup, software configuration, and integration testing, security teams spend more time building infrastructure than analyzing threats.
Cloud SIEM compresses this timeline to days or weeks. The infrastructure already exists. You configure your log sources, connect them through pre-built integrations or lightweight agents, and start collecting security data.
This isn't just a convenience improvement. Every day without adequate security monitoring is a day of exposure. Threat actors don't pause while your SIEM project works through procurement cycles. Cloud SIEM lets security teams start detecting threats immediately instead of spending months on groundwork.
2. Predictable Costs Replace Capital Expenses
On-premises SIEM demands significant upfront investment. Hardware, software licenses, implementation services, and dedicated staff to manage it all can push initial costs into six or seven figures. Then come the surprises: unplanned storage expansions, hardware refreshes, and maintenance contract renewals.
Cloud SIEM operates on subscription pricing — monthly or annual, based on data volume or user count. Security spending becomes operational rather than capital, and it becomes predictable.
When log volumes grow, you don't scramble for emergency hardware purchases. The provider's infrastructure scales, and your costs adjust proportionally. Finance teams appreciate the predictability. Security teams appreciate not fighting for capital budget every time they need more capacity.
3. Auto-Scaling Handles Growth Without Manual Intervention
As organizations grow — more users, more applications, more cloud workloads — log volumes increase. On-premises SIEM hits capacity limits that require planning cycles, procurement, installation downtime, and configuration changes.
Cloud SIEM scales automatically. Need to ingest logs from 50 new SaaS applications after an acquisition? The platform absorbs the increase. Experiencing a spike in log volume during a security incident? Processing capacity expands without anyone filing a ticket.
This elasticity means security teams never have to choose between complete visibility and system performance. They get both, without capacity planning exercises or emergency hardware orders.
4. Always-Current Threat Intelligence
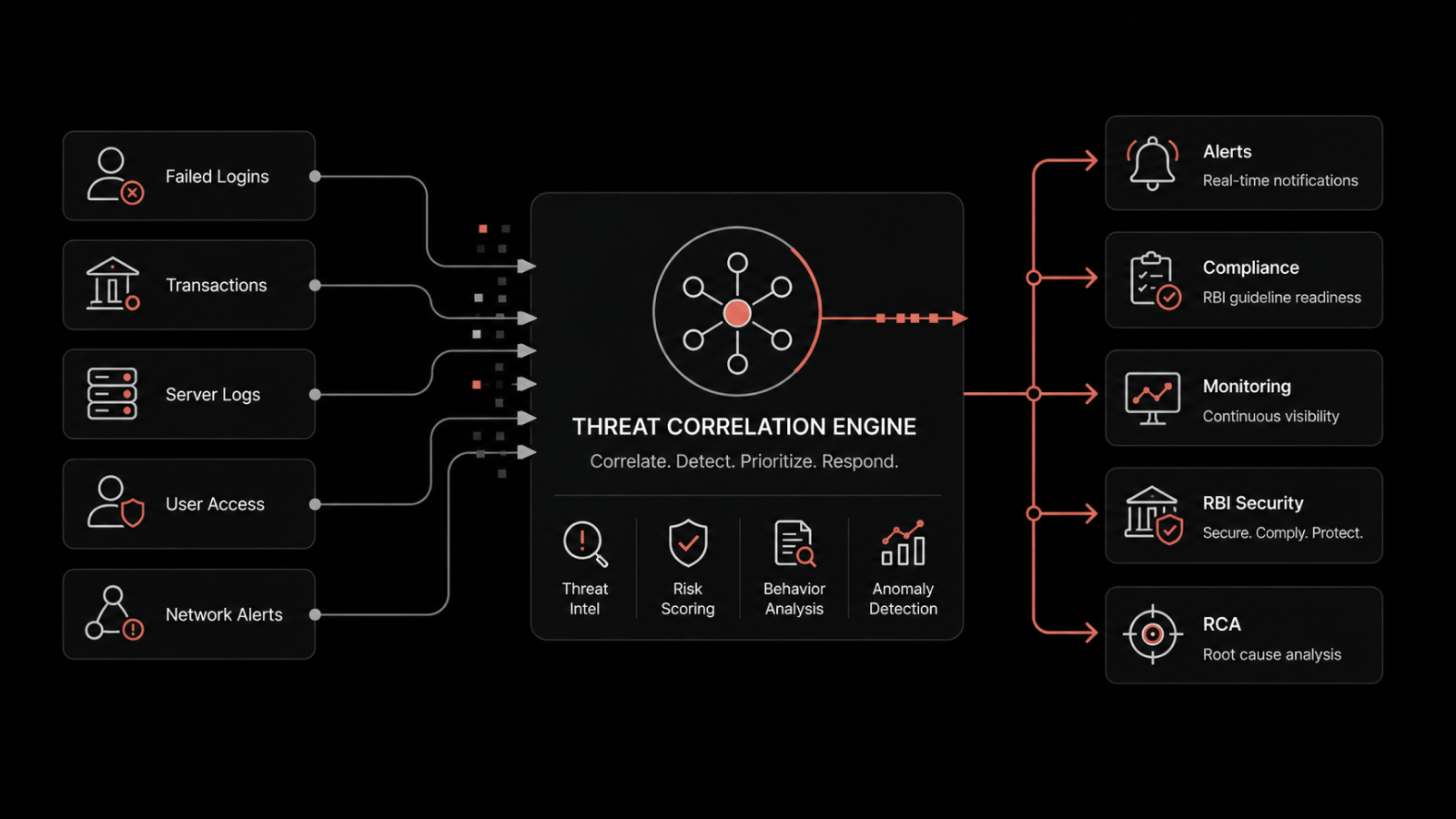
The threat environment changes daily. New attack techniques, new malware families, and new vulnerability exploits appear continuously. Detection rules that worked last month may miss today's threats.
With on-premises SIEM, keeping threat intelligence current falls on your security team. They need to research new threats, write detection rules, test them, and deploy updates. Most teams don't have the bandwidth to keep up.
Cloud SIEM providers maintain threat intelligence for all their customers simultaneously. When a new attack technique is identified, the provider builds detection logic and pushes it to every customer at once. Your SIEM benefits from threats detected across the provider's entire customer base — not just what your internal team has time to research.
This collective intelligence model means smaller security teams get access to threat detection capabilities that would otherwise require a dedicated threat research function.
5. Pre-Built Integrations With Your Security Stack
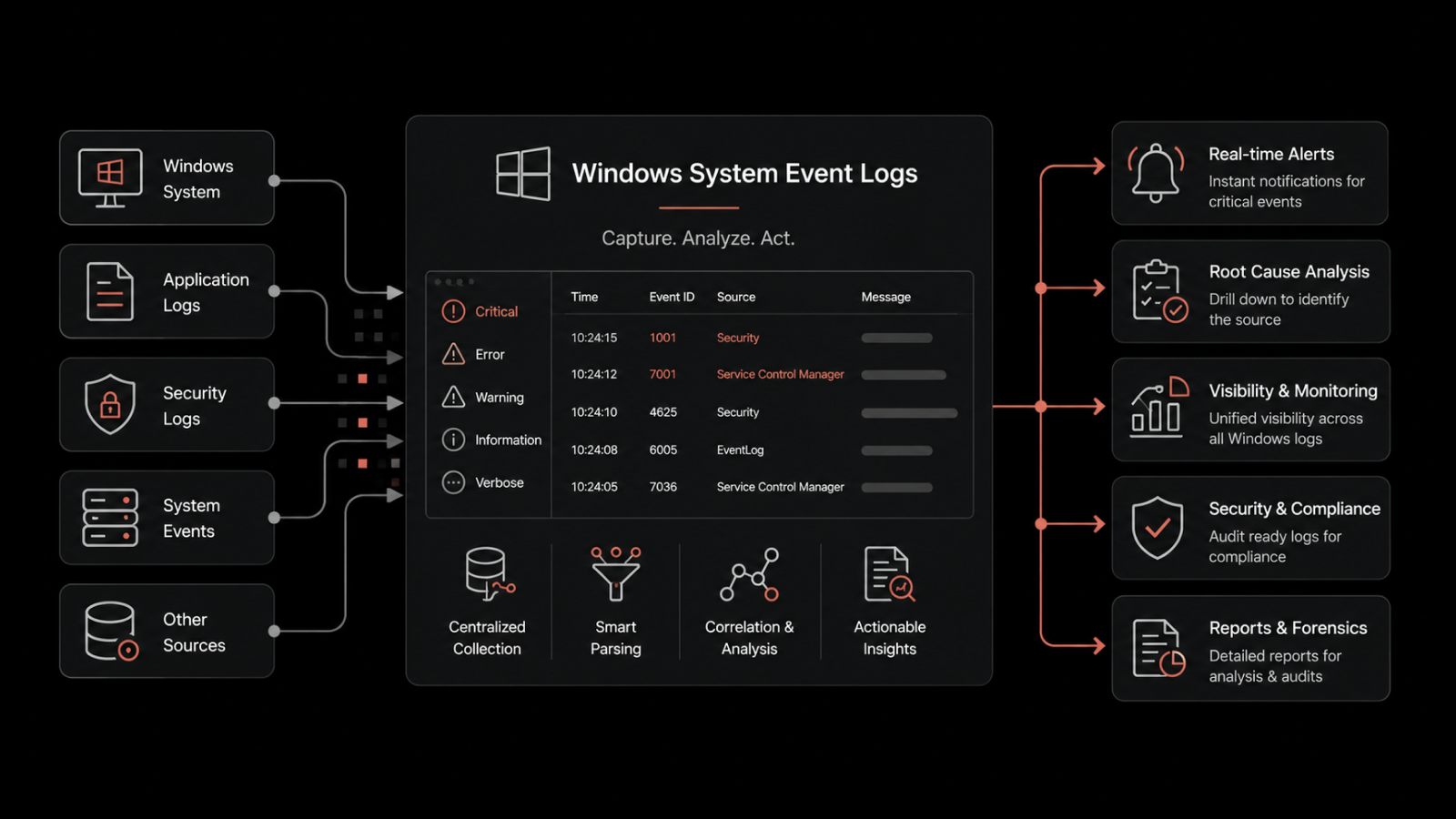
Security isn't a single tool — it's an ecosystem. Your SIEM needs to collect data from firewalls, endpoint protection platforms, identity providers, cloud platforms, email security gateways, and dozens of other sources.
Traditional SIEM integration meant custom connectors, API development, and constant maintenance as vendors updated their systems. Each integration was a mini-project.
Cloud SIEM providers maintain pre-built integrations with hundreds of security and IT tools. They handle API changes, data format updates, and authentication modifications. When you adopt a new security tool, there's a strong chance your cloud SIEM already supports it. If not, the provider adds support for all customers — you don't build a one-off connector.
6. Less Infrastructure Management, More Threat Analysis
On-premises SIEM requires dedicated staff for server management, storage maintenance, patching, backups, and performance tuning. These are IT infrastructure tasks, not security tasks — but they consume security team bandwidth.
Cloud SIEM eliminates this operational overhead. The provider manages servers, storage, databases, networking, and software updates. Your security analysts spend their time on threat detection, investigation, and response — the work that actually reduces organizational risk.
For organizations with lean security teams, this shift is significant. It lets a five-person team operate with the analytical capacity that previously required a much larger staff.
7. Secure Remote Access for Distributed Teams
Security operations run around the clock. Analysts need access to SIEM data from home offices, SOCs, satellite offices, or on-site during incident response — wherever they happen to be.
On-premises SIEM typically requires VPN connections and often suffers from poor remote performance. Dashboard loading times increase, query results lag, and the experience degrades analyst productivity.
Cloud SIEM provides secure, browser-based access from any location with an internet connection. Analysts across time zones monitor the same data in real time. Remote team members get the same experience as those in the office. As security teams adopt distributed work models, this accessibility becomes a force multiplier.
Who Should Consider Cloud SIEM?
Cloud SIEM is a strong fit for organizations that:
Lack dedicated SIEM infrastructure staff and want to redirect security resources toward threat analysis
Operate in hybrid or multi-cloud environments where log sources span on-premises and cloud infrastructure
Need to meet compliance requirements (SOC 2, HIPAA, PCI DSS, GDPR) with built-in reporting capabilities
Are scaling rapidly through growth or acquisition and need security monitoring that keeps pace
Have distributed security teams requiring consistent access regardless of location
Make the Move to AI-Driven Cloud Security With Motadata
Motadata's AI-native platform brings together security monitoring, log analytics, and infrastructure observability in a single, unified solution. Instead of managing separate tools for SIEM, network monitoring, and IT operations, you get correlated intelligence across your entire stack. Motadata's AIOps engine applies machine learning to detect anomalies, reduce alert noise, and surface the threats that matter — so your security team spends less time on infrastructure upkeep and more time protecting the business. Ready to see how it works? Request a demo and experience cloud-scale security monitoring built for modern IT environments.
FAQs
What are the main cost advantages of cloud SIEM over on-premises SIEM?
Cloud SIEM eliminates upfront capital expenses for hardware, software licenses, and implementation services. You pay a predictable monthly or annual subscription based on data volume. There are no surprise costs for storage expansions, hardware refreshes, or dedicated infrastructure staff. Most organizations see a 30-50% reduction in total cost of ownership over three years compared to on-premises deployments.
How does cloud SIEM handle compliance requirements like HIPAA or PCI DSS?
Cloud SIEM providers typically include built-in compliance reporting templates for major frameworks — HIPAA, PCI DSS, SOC 2, GDPR, and others. Log retention policies, access controls, encryption, and audit trails are managed at the platform level. This means your compliance posture is maintained continuously rather than assembled manually before audits.
Can cloud SIEM integrate with my existing security tools?
Yes. Cloud SIEM platforms maintain pre-built integrations with hundreds of security and IT tools, including firewalls, endpoint protection, identity providers, cloud platforms (AWS, Azure, GCP), and SaaS applications. The provider maintains these integrations and handles API changes, so your team doesn't need to build or maintain custom connectors.
What happens to cloud SIEM performance during a security incident with high log volumes?
Cloud SIEM auto-scales to handle volume spikes. During a security incident — when log volumes may increase 10x or more — the platform's processing and storage capacity expands automatically. There's no degradation in query performance or alert generation, and no need for manual capacity adjustments. You continue investigating and responding without worrying about infrastructure limits.
Is it difficult to migrate from on-premises SIEM to cloud SIEM?
Migration complexity depends on the number of log sources and custom detection rules you've built. Most cloud SIEM providers offer migration tools and professional services to help transition existing rules, dashboards, and integrations. A phased approach — running both systems in parallel during transition — is common and reduces risk. Typical migrations complete in four to eight weeks.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.