Agentless Network Monitoring: 7 Advantages of Using Native Protocols
Amartya Gupta
Every device you add to your network is another endpoint you need to monitor, and most IT teams don't have the bandwidth to install and maintain proprietary agents on every single one. That's where native protocol monitoring changes the game. By leveraging protocols already built into your infrastructure, you gain full visibility without the overhead of agent deployment.
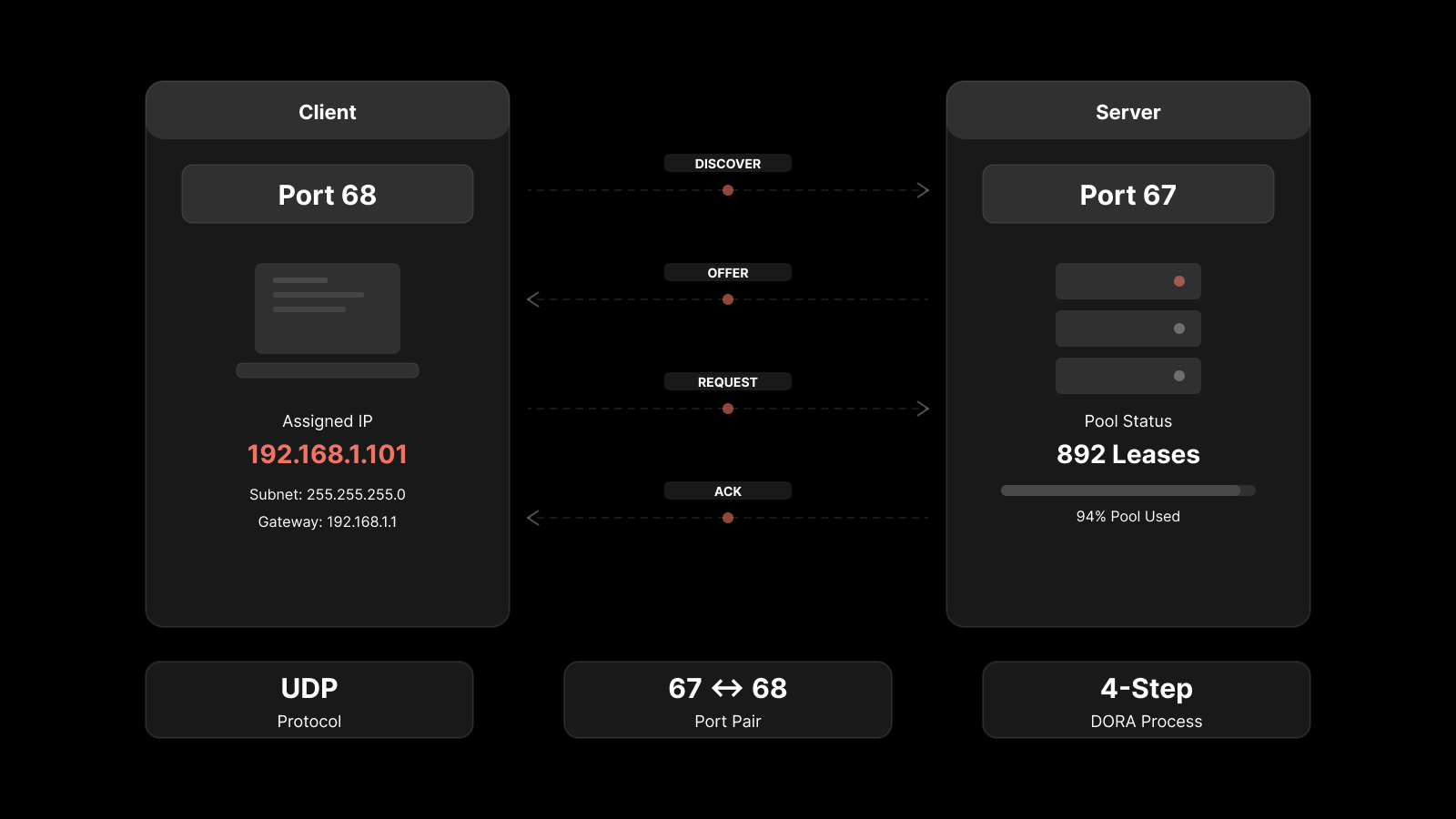
Agentless network monitoring is a method of tracking network health, performance, and availability by using protocols natively embedded in devices and operating systems -- such as SNMP, WMI, SSH, and PowerShell -- without installing any third-party software on monitored endpoints.
What Are Native Protocols in Network Monitoring?
Native protocols are communication standards embedded directly into network devices, servers, and operating systems. They allow monitoring platforms to collect performance data, health metrics, and event information without requiring any additional software installation on the target system.
Think of it this way: every router, switch, server, and firewall in your infrastructure already speaks a monitoring language. Native protocol monitoring simply taps into that existing capability.
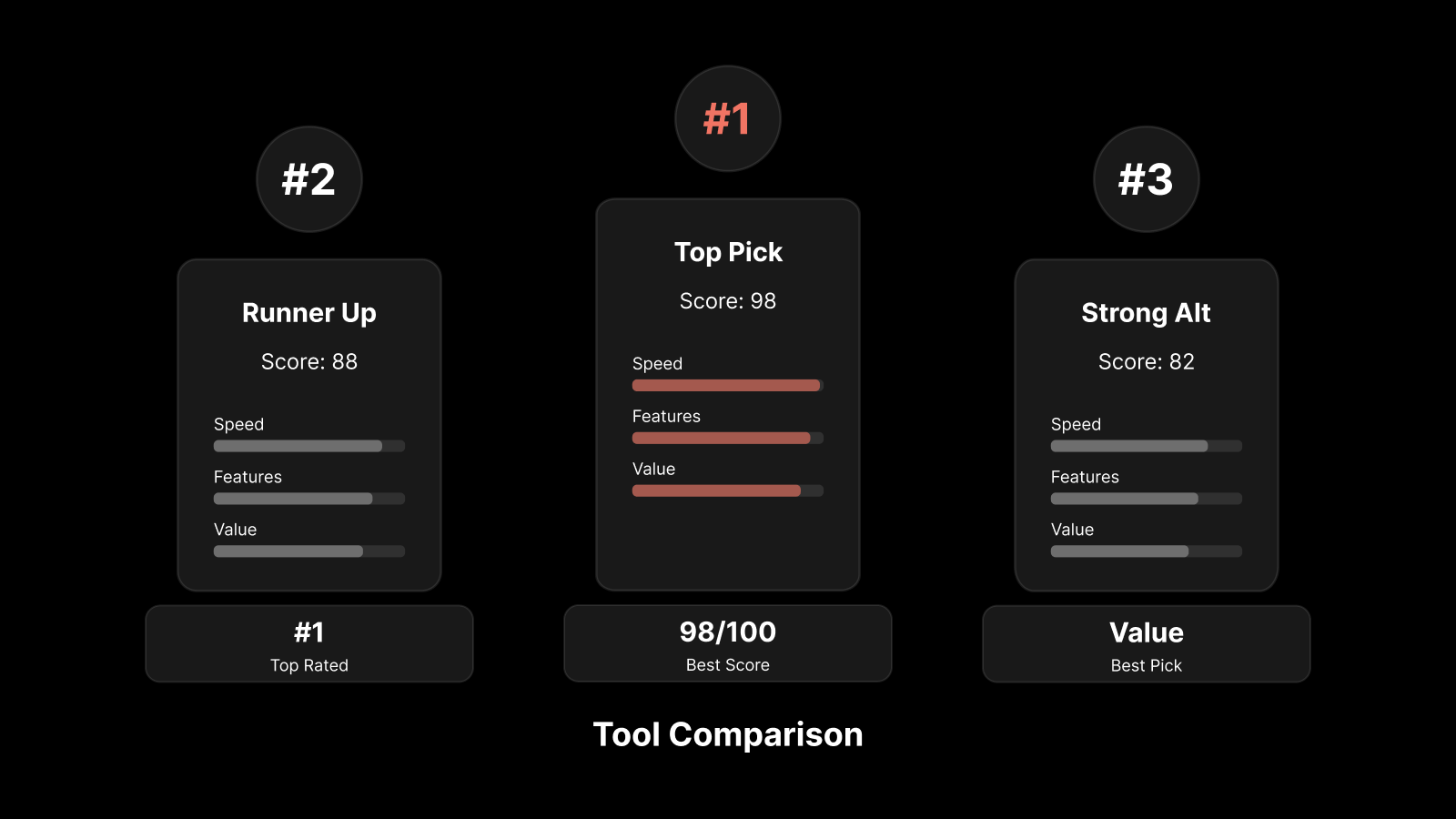
Here's a quick comparison of the most widely used native protocols:
Protocol | Full Name | Primary Use | Supported Platforms |
|---|---|---|---|
SNMP | Simple Network Management Protocol | Device health, interface stats, bandwidth | Routers, switches, firewalls, printers |
WMI | Windows Management Instrumentation | System metrics, process monitoring, events | Windows servers and workstations |
SSH | Secure Shell | Remote command execution, log retrieval | Linux/Unix servers, network appliances |
PowerShell | PowerShell Remoting | Advanced Windows monitoring, scripting | Windows environments |
JMX | Java Management Extensions | JVM monitoring, application metrics | Java-based applications |
JDBC | Java Database Connectivity | Database health, query performance | SQL/NoSQL databases |
HTTP/HTTPS | Hypertext Transfer Protocol | API monitoring, web service health | Web servers, REST APIs, cloud services |
Why Agentless Monitoring Outperforms Agent-Based Approaches
Before diving into the specific advantages, it's worth understanding the fundamental difference between these two approaches.
Agent-based monitoring requires you to install proprietary software on every device you want to monitor. That agent collects data locally and transmits it to a central server. While this approach has its place, it introduces complexity at every stage -- deployment, configuration, updates, and security management.
Agentless monitoring uses protocols your devices already support. The monitoring platform communicates directly with endpoints using standards like SNMP or WMI, pulling the data it needs without any footprint on the target system.
For most enterprise environments, agentless monitoring delivers the same visibility with far less operational burden.
1. Dramatic Cost Reduction Across the Board
When you use native protocols, you're leveraging what's already built into your IT environment. There's no additional licensing for agent software, no per-endpoint fees, and no hidden costs that creep up as your infrastructure scales.
The cost savings extend beyond software licensing:
Zero deployment labor -- No technician time spent installing agents on hundreds or thousands of endpoints.
No maintenance overhead -- Agents require updates, patches, and compatibility testing with every OS upgrade. Native protocols don't.
Reduced training costs -- IT teams already understand SNMP and WMI. They don't need vendor-specific agent training.
Industry data shows that organizations using agentless monitoring approaches reduce their total monitoring cost of ownership by 30-45% compared to fully agent-based solutions. For a mid-size enterprise with 2,000+ endpoints, that translates to significant annual savings.
2. Simplified Deployment and Management
Agent-based tools demand a multi-step rollout: package the agent, test compatibility, schedule maintenance windows, deploy to each server, configure collection parameters, and verify connectivity. Multiply that by every server in your environment.
With native protocols, the math is straightforward. You point your network monitoring tool at your network segments, and it discovers devices using protocols they already support. There's no installation queue, no compatibility matrix, and no deployment failures to troubleshoot.
This simplicity matters most in three scenarios:
Rapid scaling -- When you add 50 new servers in a week, agentless monitoring covers them immediately through discovery scans.
M&A integration -- Acquiring another company's infrastructure? Agentless monitoring gives you visibility on day one, without touching their systems.
Multi-vendor environments -- SNMP works across Cisco, Juniper, Palo Alto, and virtually every other network vendor. One protocol, universal coverage.
3. Stronger Security Posture
Every agent you install on a production system introduces risk. Here's why agentless monitoring keeps your security posture intact:
No open ports -- Agent-based tools typically require a dedicated port for communication. Each open port is a potential attack vector. Native protocols use existing, well-secured communication channels.
No third-party code on critical systems -- Installing an agent means trusting the vendor's development practices, update pipeline, and vulnerability management. With agentless monitoring, your security depends on your own standards.
No privilege escalation risks -- Agents often require administrative or root-level access to function. That level of access on every endpoint multiplies your attack surface.
Firewall rule simplicity -- SNMP, WMI, and SSH use well-known ports with established security best practices. Your firewall team doesn't need to create custom rules for proprietary agent traffic.
In an era where ransomware attacks and supply chain compromises are constant threats, minimizing the software footprint on your infrastructure isn't just convenient -- it's a security imperative.
4. Broad Coverage Across Multi-Vendor Environments
Modern enterprise networks aren't single-vendor. You've likely got Cisco switches alongside Juniper routers, Dell servers running Windows, Linux boxes from various OEMs, and cloud workloads across AWS, Azure, or GCP.
Native protocols are vendor-agnostic by design. SNMP is supported by virtually every network device manufactured in the last two decades. WMI covers the entire Windows ecosystem. SSH handles every Linux and Unix variant.
This universality means your monitoring platform provides a single pane of glass across your entire infrastructure -- without maintaining a dozen different agent packages for different OS versions and device types.
5. Zero Performance Impact on Monitored Systems
Agents consume CPU, memory, and disk I/O on the systems they monitor. In performance-sensitive environments -- database servers, real-time transaction processing systems, or latency-critical applications -- that overhead matters.
Native protocol monitoring operates through lightweight queries that place negligible load on target systems. An SNMP poll consumes a fraction of the resources that a full monitoring agent would, and it completes in milliseconds.
This is particularly important for:
Production databases where every CPU cycle affects query performance
Edge devices with limited compute resources (IoT gateways, embedded systems)
High-frequency trading or real-time processing platforms where microsecond latency impacts matter
6. Cloud and Hybrid Infrastructure Compatibility
The argument that agentless monitoring is limited to on-premises environments is outdated. Modern native protocol monitoring works seamlessly across cloud and hybrid architectures:
Cloud APIs serve as native protocols for cloud resources, providing metrics without installing agents on cloud instances.
SSH and SNMP work across VPN tunnels and private cloud networks, extending monitoring to remote sites.
Container and Kubernetes environments expose metrics through native endpoints (Prometheus, cAdvisor) that agentless platforms consume directly.
For organizations running hybrid infrastructure -- which, according to Flexera's 2025 State of the Cloud Report, includes 87% of enterprises -- agentless monitoring provides unified visibility without managing separate agent deployments for on-premises and cloud workloads.
7. Faster Time to Value and Reduced Operational Friction
The cumulative effect of all these advantages is a dramatically shorter path from purchase to full operational monitoring. While agent-based deployments can take weeks or months to fully roll out across a large environment, agentless monitoring platforms deliver visibility within hours.
This accelerated time-to-value means:
Faster incident detection from day one of deployment
Immediate compliance reporting capability without waiting for full agent rollout
Quicker ROI realization as the monitoring platform starts delivering value immediately
Reduced change management burden since no software is being installed on production systems
When to Consider Agent-Based Monitoring
Native protocols handle the vast majority of monitoring use cases, but there are scenarios where agent-based approaches add value:
Deep application-level tracing that requires code-level instrumentation
Offline or air-gapped systems that can't be reached over the network
Custom metric collection from proprietary applications with no native protocol support
Most mature organizations use a hybrid approach -- agentless monitoring for 80-90% of their infrastructure, supplemented by targeted agent deployment where native protocols can't reach. The key is choosing a monitoring platform that supports both approaches seamlessly.
How Motadata Delivers AI-Powered Agentless Monitoring
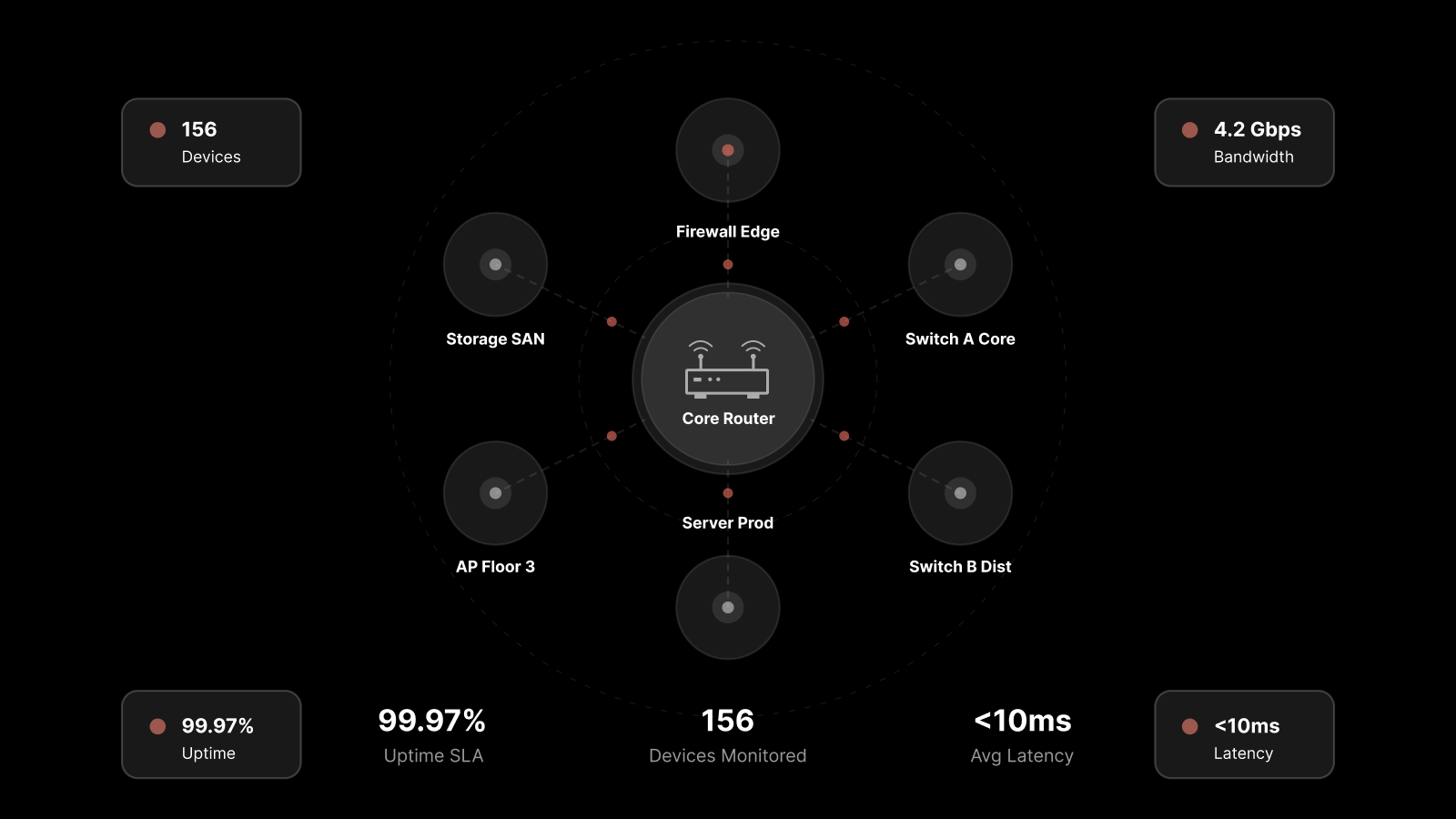
Motadata combines the simplicity of agentless monitoring with the intelligence of an AI-native platform. Its auto-discovery engine identifies every device on your network and begins collecting metrics through native protocols within minutes.
What sets Motadata apart:
AI-driven anomaly detection that learns your network's normal behavior and flags deviations before they cause outages
Support for SNMP, WMI, SSH, PowerShell, JMX, JDBC, and REST APIs -- covering your entire multi-vendor infrastructure
Unified dashboard for on-premises, cloud, and hybrid environments
Smart alerting that correlates events across devices to reduce noise and surface actionable insights
Predictive analytics that forecast capacity issues and performance degradation before they impact users
Start a free trial to see how Motadata's agentless monitoring gives you complete network visibility without the agent overhead. Or schedule a demo to explore how our AI-native platform transforms your monitoring operations.
FAQs
What is the difference between agentless and agent-based network monitoring?
Agentless monitoring uses protocols already built into devices (SNMP, WMI, SSH) to collect performance data remotely. Agent-based monitoring requires installing proprietary software on each monitored endpoint. Agentless is simpler to deploy, more secure, and less costly to maintain, while agent-based provides deeper application-level visibility in specific use cases.
Which native protocols are most commonly used for network monitoring?
SNMP (Simple Network Management Protocol) is the most widely used, supported by virtually all network devices. WMI handles Windows environments, SSH covers Linux/Unix systems, JMX monitors Java applications, and PowerShell enables advanced Windows scripting. Most organizations use a combination of these protocols for comprehensive coverage.
Is agentless monitoring suitable for cloud environments?
Yes. Modern agentless monitoring platforms collect cloud metrics through native APIs provided by AWS, Azure, and GCP. Combined with SSH and SNMP over VPN tunnels, agentless approaches provide unified visibility across on-premises, cloud, and hybrid environments without deploying agents on cloud instances.
Does agentless monitoring provide the same level of detail as agent-based?
For infrastructure and network monitoring, agentless protocols provide equivalent detail -- device health, performance metrics, bandwidth utilization, and event data. Agent-based monitoring offers advantages only for deep application-level tracing and code-level instrumentation, which represents a small percentage of overall monitoring needs.
How does agentless monitoring improve network security?
By eliminating the need for third-party software on monitored systems, agentless monitoring reduces the attack surface. There are no additional open ports, no third-party code running with elevated privileges, and no agent update pipeline that could be compromised in a supply chain attack.