The Role of Automation in Incident Management: Faster Response, Better Accuracy
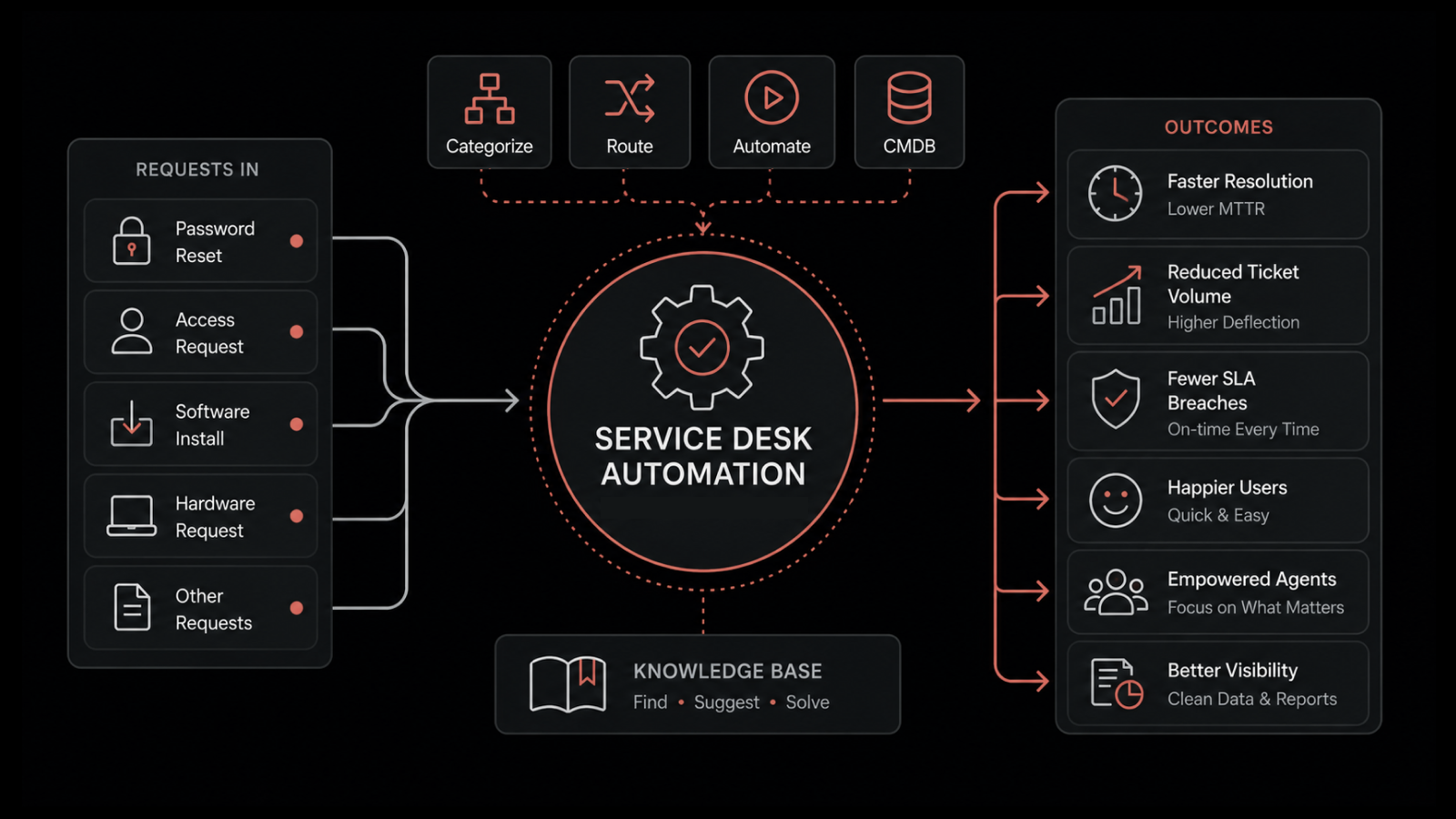
Incident management automation is the use of AI, machine learning, and rule-based systems to detect, categorize, prioritize, and route IT incidents -- reducing manual effort and accelerating resolution times.
Your monitoring dashboards light up with 100+ alerts before lunch. Half are duplicates. A quarter are false positives. Somewhere in the noise, a production database is silently degrading. By the time your team triages the real issue, users have already noticed.
This scenario plays out daily in IT organizations worldwide. According to industry research, nearly 70% of organizations receive more than 100 incident alerts every day, yet most investigate fewer than 20. The math doesn't work -- and throwing more people at the problem doesn't scale.
Automation changes that equation. It handles the repetitive, high-volume work of detection, categorization, and routing so your incident response teams can focus on what actually requires human judgment: diagnosing complex issues and restoring services.
What Is Incident Management and Why Does It Matter?
Incident management is the process organizations use to identify, analyze, and resolve events that disrupt or threaten IT services. It typically follows these stages:
Detection -- Monitoring systems flag anomalies, errors, or threshold breaches
Logging -- The incident is recorded with relevant context (timestamp, affected systems, severity)
Categorization -- The incident is classified by type (hardware, software, network, security)
Prioritization -- Severity and business impact determine response urgency
Response and Resolution -- The appropriate team investigates, diagnoses, and fixes the issue
In modern IT environments with distributed architectures, cloud workloads, and interconnected services, the volume and complexity of incidents have outpaced what manual processes can handle. Teams face alert fatigue, inconsistent triage, and slow escalations -- all of which extend outages and increase business impact.
A structured incident management process backed by automation addresses these challenges at their root.
Why Manual Incident Management Can't Keep Up
Before diving into automation types, it's worth understanding exactly where manual processes break down.
Alert Overload and Fatigue
When teams receive hundreds of alerts daily, they develop alert fatigue. Real incidents get lost in the noise of false positives, duplicate alerts, and low-priority notifications. Studies show that alert fatigue is a contributing factor in delayed response to major incidents across industries.
Inconsistent Triage
Without automation, incident categorization and prioritization depend on whoever's on call. Different team members apply different judgment, leading to inconsistent severity assignments, misrouted tickets, and delayed escalations.
Slow Escalation Chains
Manual escalation requires someone to recognize an incident's severity, identify the right team, and initiate a handoff. Each step adds minutes or hours. For production-impacting incidents, those delays translate directly to lost revenue and degraded user experience.
Knowledge Gaps
Experienced engineers know which alerts matter and which are noise. When they're unavailable (vacation, turnover, shift changes), institutional knowledge walks out with them. Manual processes don't capture and codify this expertise.
How Automation Transforms Incident Management
Automation addresses each of these failure points. Here's how it improves the incident lifecycle from detection through resolution.
Faster Detection and Response
Automated monitoring and alerting systems continuously analyze infrastructure metrics, logs, and events. When anomalies are detected, they trigger immediate alerts without waiting for a human to notice a dashboard change.
AI-driven correlation engines go further by connecting related events across systems. Instead of generating 50 separate alerts for symptoms of the same root cause, they surface a single, enriched incident with full context. This cuts mean time to detect (MTTD) from hours to minutes.
More Accurate Categorization and Prioritization
Machine learning models trained on historical incident data can categorize and prioritize new incidents with higher accuracy and consistency than manual triage. They apply the same criteria every time, regardless of who's on call or how busy the team is.
This eliminates the "it depends on who's working" problem and ensures that critical incidents are escalated immediately while low-priority issues are queued appropriately.
Intelligent Routing and Escalation
Automated routing sends incidents directly to the team or individual best equipped to handle them, based on category, severity, affected systems, and current workload. If an incident isn't acknowledged within a defined timeframe, automatic escalation kicks in.
No more incidents sitting unnoticed in a shared queue. No more manual handoffs that add 30 minutes to resolution time.
Reduced Alert Fatigue Through Noise Suppression
Automation tools deduplicate alerts, suppress known false positives, and correlate related events before they reach your team. Instead of wading through 100 alerts to find the 5 that matter, your engineers see a prioritized, contextual feed of real incidents.
This isn't just an efficiency gain -- it's a quality-of-work improvement that directly affects retention and team morale.
Consistent Documentation and Audit Trails
Every automated action is logged: detection timestamps, categorization decisions, routing paths, escalation triggers, resolution steps. This creates a complete audit trail without anyone having to manually update a ticket.
The result is better post-incident analysis, more accurate reporting, and compliance documentation that generates itself.
Types of Automation in Incident Management
Different automation approaches solve different parts of the problem. Most mature organizations use a combination of all four.
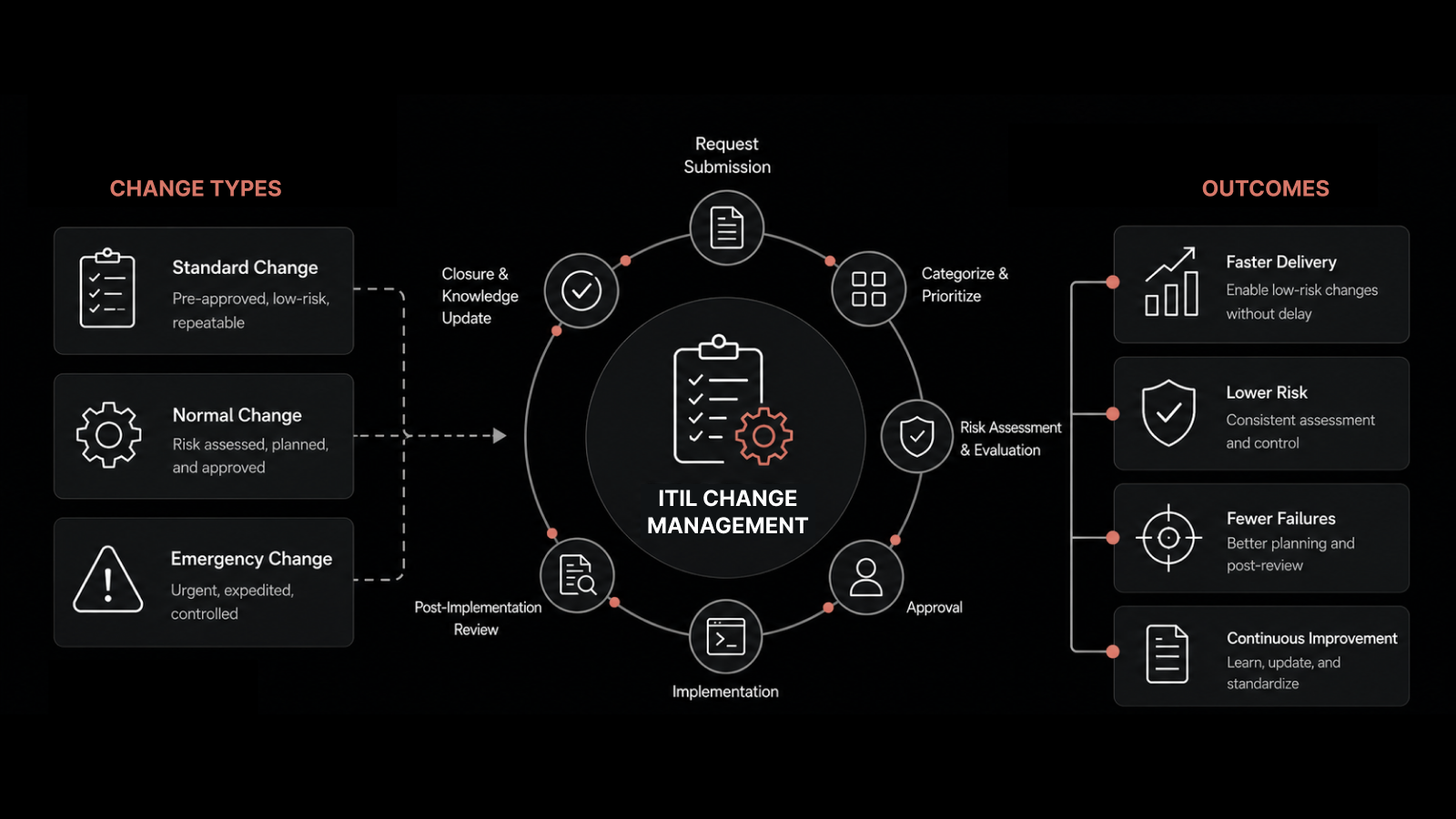
Rule-Based Automation
Rule-based systems apply predefined logic: "If alert type = X and severity = critical, then route to Team A and set priority P1." These rules codify your team's institutional knowledge into repeatable, consistent actions.
Best for: Categorization, prioritization, initial routing, SLA enforcement
Example: All disk-space alerts above 90% on production database servers automatically create a P2 incident and route to the DBA team.
Machine Learning-Based Automation
ML models analyze historical incident data to identify patterns, predict incident severity, detect anomalies, and recommend resolution steps. They improve over time as they process more data.
Best for: Anomaly detection, predictive alerting, root cause analysis, pattern recognition across large datasets
Example: An ML model detects that a specific combination of CPU spikes and network latency patterns has preceded database failures 85% of the time, and proactively alerts the team before the failure occurs.
Workflow-Based Automation
Workflow automation defines end-to-end processes for handling specific incident types. When a trigger event occurs, the workflow executes a sequence of steps: notify stakeholders, run diagnostic scripts, collect logs, create a war room channel, assign responders.
Best for: Standardizing response procedures for known incident types (security breaches, service outages, performance degradation)
Example: A security alert triggers an automated workflow that isolates the affected endpoint, captures forensic data, notifies the security team, and creates an incident timeline -- all within 60 seconds of detection.
Chatbots and Virtual Assistants
AI-powered chatbots serve as first-line support for end users and L1 technicians. They handle common requests (password resets, VPN issues, access requests), gather diagnostic information, and create properly categorized tickets when human intervention is needed.
Best for: High-volume, repetitive service requests; initial information gathering; guided troubleshooting
Example: An employee reports slow application performance through a chatbot. The bot collects browser version, network details, and application name, runs basic connectivity tests, and either resolves the issue with a cache-clear instruction or escalates a fully documented ticket to L2 support.
Best Practices for Automating Incident Management
Start with Your Highest-Volume, Lowest-Complexity Incidents
Don't try to automate everything at once. Identify the incident types that consume the most team time but follow predictable patterns. Password resets, disk space alerts, certificate expirations, and service restarts are common starting points that deliver quick wins.
Map Your Current Process Before Automating It
Automation amplifies whatever process you give it. If your current incident workflow is inconsistent or poorly defined, automate it and you'll get fast, consistent chaos. Document your process, identify bottlenecks, and fix them before building automation around them.
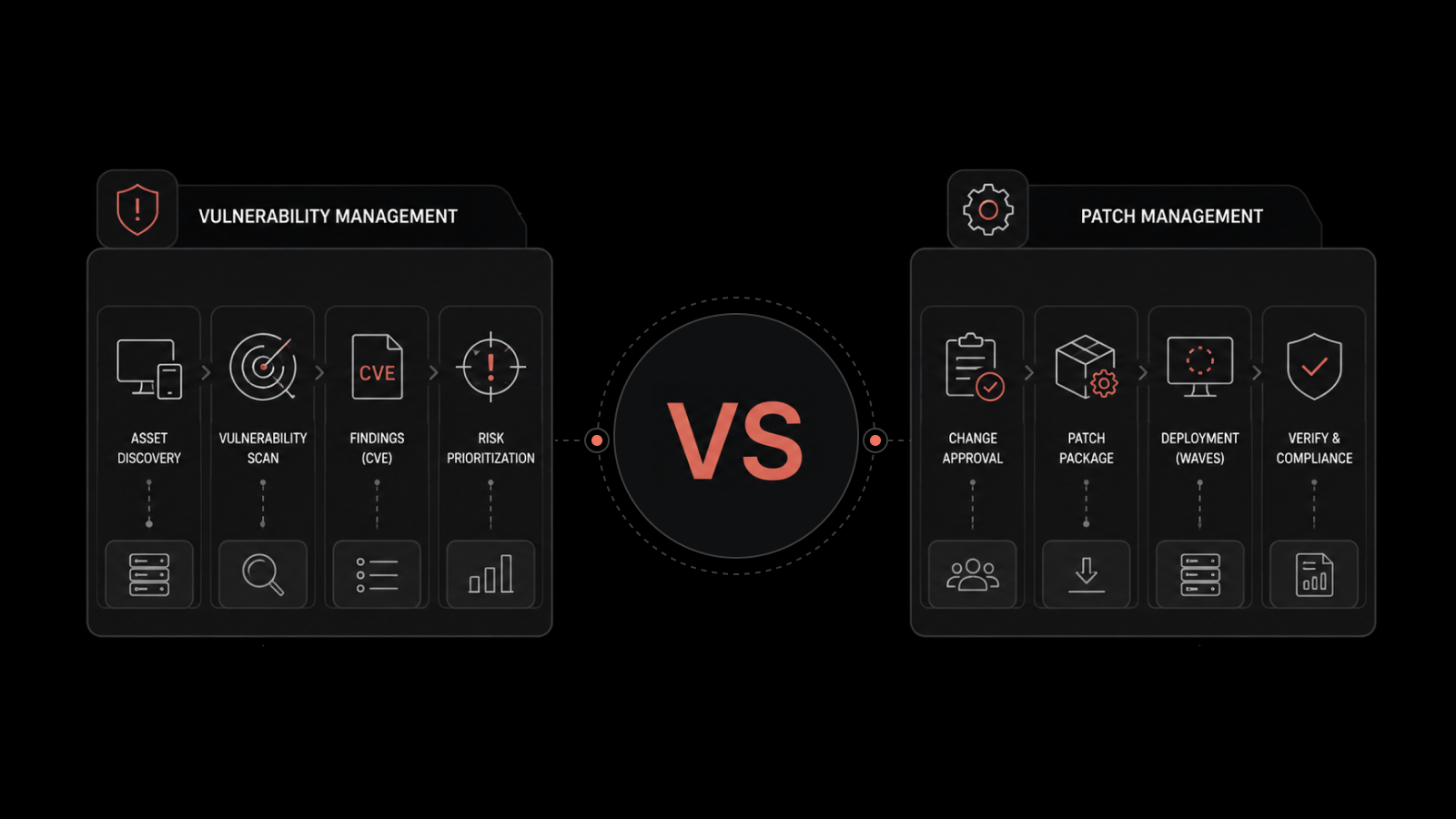
Connect Automation to Your Data Sources
Effective incident automation pulls data from multiple sources: network monitoring tools, application performance monitors, log aggregators, CMDB, and user-reported tickets. The more context your automation has, the better its categorization and routing decisions.
Build Feedback Loops for Continuous Improvement
Track how your automated rules and ML models perform. Are incidents being miscategorized? Are escalations happening too late -- or too early? Use post-incident reviews to refine your automation rules and retrain ML models with new data.
Maintain Human Oversight for High-Severity Incidents
Automation handles triage and initial response. Humans handle judgment calls: Is this a security breach or a misconfiguration? Should we fail over or troubleshoot in place? Design your automation to surface these decisions to experienced engineers, not to make them autonomously.
Real-World Impact: Emirates Healthcare Case Study
Emirates Healthcare needed to solve three specific problems:
Location-based ticket classification: Network-related tickets needed automatic routing based on physical site
Email-to-ticket integration: Required compatibility with current Microsoft Exchange infrastructure
Automated ticket lifecycle: Tickets needed automatic routing and closure for resolved issues
The ITSM solution they implemented delivered:
ITIL-compliant incident and service request handling with multi-level classification for better ticket organization and prioritization
Email-to-ticket automation that eliminated manual ticket creation from support emails
Workflow automation that handled repetitive routing tasks and auto-closed resolved tickets
Improved asset management through barcode scanning and WMI/SSH protocol integration
The result: faster ticket resolution, reduced manual effort for the IT team, and consistent incident handling across all locations.
Measuring Automation's Impact on Incident Management
Track these KPIs to quantify the value your automation delivers:
KPI | What It Measures | Typical Improvement |
|---|---|---|
Mean Time to Detect (MTTD) | Time from incident occurrence to detection | 50-70% reduction |
Mean Time to Acknowledge (MTTA) | Time from detection to team acknowledgment | 60-80% reduction |
Mean Time to Resolve (MTTR) | Total time from detection to resolution | 30-50% reduction |
First-Contact Resolution Rate | Incidents resolved without escalation | 20-40% improvement |
Alert-to-Incident Ratio | How many alerts result in actual incidents | Noise reduction of 60-80% |
Incidents per Technician | Workload distribution and efficiency | 2-3x throughput increase |
SLA Compliance Rate | Percentage of incidents resolved within SLA | 90%+ target |
Build Faster, Smarter Incident Response with Motadata
Alert fatigue, slow escalations, and inconsistent triage don't have to be the norm. Motadata ServiceOps brings AI-powered automation to every stage of incident management -- from intelligent alert correlation and automated categorization to workflow-driven response and real-time reporting.
Whether you're handling 50 incidents a day or 500, Motadata gives your team the tools to respond faster, resolve sooner, and spend their expertise where it matters most.
Request a Demo and see how Motadata ServiceOps transforms incident management from reactive firefighting into a proactive, automated operation.
FAQs
What components of incident management can be automated?
Most stages benefit from automation: detection (monitoring and alerting), logging (automatic ticket creation), categorization (ML-based classification), prioritization (rule-based severity assignment), routing (skill-based assignment), and initial response (automated runbooks). Complex diagnosis and final resolution decisions typically remain with human engineers.
How does automation reduce false positives in incident management?
ML models trained on historical data learn to distinguish real incidents from noise. Alert correlation engines group related events and suppress duplicates. Rule-based filters catch known false-positive patterns. Together, these reduce the alerts your team sees by 60-80%, letting them focus on genuine issues.s.
Can automation handle major incidents or just routine ones?
Automation excels at the initial stages of any incident: detection, triage, escalation, and stakeholder notification. For major incidents, it handles the "mechanics" (creating war rooms, paging on-call engineers, collecting diagnostic data) so your team can focus entirely on diagnosis and resolution. It doesn't replace human judgment for complex, high-impact decisions.
What's the difference between AIOps and incident management automation?
AIOps is a broader discipline that applies AI and ML across all IT operations -- capacity planning, change impact analysis, performance optimization, and incident management. Incident management automation is one component of an AIOps strategy, focused specifically on the incident lifecycle from detection to resolution.
Author
Motadata Team
Content Team
Articles produced collaboratively by our engineering and editorial teams bear the collective authorship of Motadata Team.