Advanced Persistent Threats (APTs): How to Detect, Identify, and Defend Against Them
Arpit Sharma
An advanced persistent threat (APT) is a prolonged, targeted cyberattack in which an unauthorized actor gains access to a network and remains undetected for an extended period -- often months or years -- with the goal of stealing sensitive data, conducting espionage, or sabotaging critical systems.
A nation-state hacking group breaches your network through a spear phishing email sent to a mid-level finance employee. They don't trigger any alarms. They don't encrypt your files or demand ransom. Instead, they sit quietly inside your infrastructure for 197 days -- moving laterally across systems, escalating privileges, and exfiltrating intellectual property one small batch at a time.
That's not a hypothetical. The median dwell time for APTs is still measured in months, not minutes. And the damage they cause -- stolen trade secrets, compromised customer data, regulatory penalties -- compounds every day they go undetected.
This guide covers what APTs are, how they operate, how to detect them, and what defense strategies actually work.
Understanding Advanced Persistent Threats
APTs differ from conventional cyberattacks in almost every dimension. While most attacks -- ransomware, phishing campaigns, DDoS -- aim for quick results, APTs play the long game. They're designed to infiltrate, persist, and extract value over extended periods without triggering detection.
Three characteristics define an APT:
Advanced: Attackers use sophisticated techniques including custom malware, zero-day exploits, and social engineering tailored to specific targets.
Persistent: The attack is sustained over months or years. Even if one access point is discovered and closed, attackers maintain multiple footholds.
Threat: The actors behind APTs are well-resourced -- nation-states, state-sponsored groups, or organized crime syndicates with specific strategic objectives.
APTs don't target random victims. They select targets based on the intelligence, data, or strategic value the organization holds. Government agencies, defense contractors, financial institutions, healthcare organizations, and technology companies are the most common targets.
The APT Kill Chain: How Attacks Unfold
Understanding the APT lifecycle is the first step toward detection. Every APT follows a variation of this attack chain:
Stage 1: Reconnaissance
Attackers research the target organization extensively -- identifying key personnel, mapping technology infrastructure, and finding potential entry points. They study organizational charts, social media profiles, and publicly exposed systems.
Stage 2: Initial Access
The most common entry vector is spear phishing -- highly targeted emails crafted to trick specific individuals into clicking malicious links or opening weaponized attachments. Other access methods include exploiting unpatched vulnerabilities in public-facing applications, compromising third-party vendors, and watering hole attacks against websites the target's employees frequently visit.
Stage 3: Establishing a Foothold
Once inside, attackers install backdoors, remote access tools (RATs), or custom malware that maintains persistent access even if the initial entry point is discovered. They often hide in legitimate system processes to avoid detection.
Stage 4: Lateral Movement
Attackers move across the network, escalating privileges and compromising additional systems. They target domain controllers, authentication servers, and systems with access to high-value data. This stage is where attackers build the access they need to reach their ultimate objective.
Stage 5: Data Collection and Exfiltration
The attackers identify and collect the data they're after -- intellectual property, customer records, financial data, classified information. Data is exfiltrated in small batches through encrypted channels designed to blend in with normal outbound traffic.
Stage 6: Maintaining Persistence
APT actors don't leave after one exfiltration. They maintain multiple access paths, plant additional backdoors, and continue operating inside the network indefinitely. Removing an APT requires identifying and closing every access point -- not just the one you found first.
Real-World APT Examples
Understanding named APT groups helps contextualize the threat:
APT Group | Attribution | Notable Operations |
|---|---|---|
APT28 (Fancy Bear) | Russian military intelligence (GRU) | 2016 DNC breach, European government targeting |
APT29 (Cozy Bear) | Russian foreign intelligence (SVR) | SolarWinds supply chain attack (2020) |
Lazarus Group | North Korea | Sony Pictures hack (2014), WannaCry ransomware, cryptocurrency theft |
APT41 (Double Dragon) | China | Combined espionage and financially motivated attacks across healthcare, telecom, gaming |
APT10 (Stone Panda) | China | Managed service provider compromise campaign targeting global enterprises |
The SolarWinds attack is a defining example: APT29 compromised the software supply chain, embedding malicious code in a trusted software update that was distributed to 18,000 organizations. Attackers then selectively targeted high-value victims among those organizations, remaining undetected for months.
How to Detect Advanced Persistent Threats
APTs are designed to evade conventional security tools. Detecting them requires layered monitoring, behavioral analysis, and correlation across multiple data sources.
Indicators of Compromise (IOCs)
These are the observable signs that an APT may be operating in your environment:
Unusual outbound data transfers -- especially to unfamiliar IP addresses or during off-hours
Abnormal login patterns -- logins at unusual times, from unexpected locations, or using dormant accounts
Unexpected privilege escalations -- user accounts suddenly gaining administrative access
Anomalous DNS queries -- DNS requests to suspicious or newly registered domains
Large data staging -- accumulation of data in unusual locations before exfiltration
Unexplained system changes -- new services, scheduled tasks, or registry modifications that don't match change records
Lateral movement patterns -- one compromised account accessing multiple systems in rapid succession
SIEM and Log Correlation
Security Information and Event Management (SIEM) platforms aggregate logs from across your infrastructure and correlate events to identify patterns that no single data source would reveal. For APT detection, SIEM is essential because:
It correlates authentication logs, network flow data, endpoint telemetry, and application logs to surface multi-stage attack patterns
Automated correlation rules flag combinations of events that match known APT tactics, techniques, and procedures (TTPs)
Historical log analysis can retroactively identify APT activity that occurred before detection rules were in place
User and Entity Behavior Analytics (UEBA)
UEBA tools establish behavioral baselines for users and systems, then flag deviations. This is particularly effective against APTs because:
Legitimate credentials used at unusual times or from unusual locations trigger alerts
Gradual privilege escalation -- a hallmark of APT lateral movement -- surfaces as behavioral anomalies
Data access patterns that deviate from a user's established baseline indicate potential compromise
Network Traffic Analysis
Continuous network monitoring reveals APT activity that endpoint tools miss:
Encrypted connections to command-and-control (C2) servers
Data exfiltration disguised as normal traffic patterns
Lateral movement across network segments
DNS tunneling used for covert communication
Defending Against Advanced Persistent Threats
Detection is half the battle. A comprehensive defense strategy makes it harder for APTs to succeed at every stage of the kill chain.
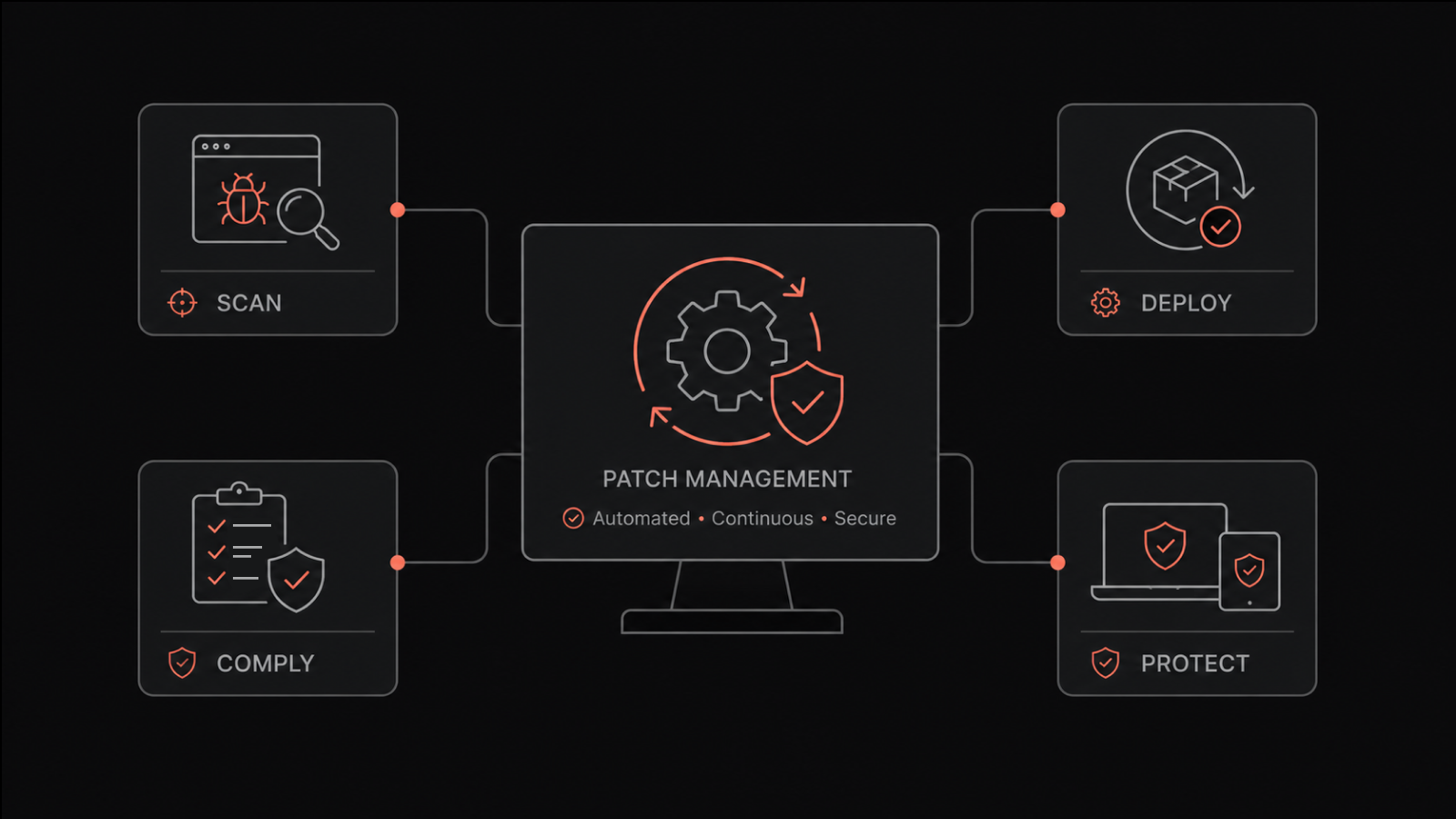
Strong Cyber Hygiene
The basics matter. Enforce multi-factor authentication on all accounts. Maintain a rigorous patching cadence for operating systems, applications, and firmware. Implement email authentication protocols (DMARC, DKIM, SPF) to reduce spear phishing effectiveness. Train employees to recognize social engineering attempts -- not with annual checkbox training, but with regular, realistic simulations.
Network Segmentation and Zero Trust
Segmenting your network into isolated zones limits an attacker's ability to move laterally. If they compromise one segment, they can't automatically reach others. Zero Trust architecture takes this further by requiring continuous authentication and authorization for every access request -- no implicit trust based on network location.
Regular Security Assessments
Penetration testing and red team exercises simulate APT tactics against your environment. They reveal vulnerabilities before real attackers find them. These assessments should include your entire attack surface -- not just perimeter systems, but internal networks, cloud environments, and third-party integrations.
Threat Intelligence Integration
Stay informed about active APT campaigns, new TTPs, and emerging indicators of compromise. Threat intelligence feeds integrated into your SIEM and monitoring tools enable automated detection of known APT infrastructure and techniques.
Proactive monitoring that combines threat intelligence with real-time network analysis gives your team the earliest possible warning of APT activity.
Incident Response Planning for APTs
APT incidents require a different response playbook than standard security events. Your APT response plan should include:
Procedures for investigating the full scope of compromise before taking remediation action (premature remediation tips off attackers)
Coordination protocols with law enforcement and intelligence agencies
Evidence preservation procedures for potential legal proceedings
Communication plans for stakeholders, customers, and regulators
Full infrastructure rebuild procedures for worst-case scenarios
APTs and Industry-Specific Risks
The vulnerability to APTs varies by industry based on the type and value of data an organization holds:
Government and defense: Primary targets for nation-state espionage. Classified information, intelligence data, and critical infrastructure details make these organizations high-value targets.
Healthcare: Patient records, research data, and pharmaceutical intellectual property attract both state-sponsored and financially motivated APT groups.
Financial services: Financial institutions hold data that enables direct monetary theft and large-scale fraud. APT groups targeting this sector often aim for payment systems and trading platforms.
Technology and manufacturing: Intellectual property theft -- product designs, source code, trade secrets -- is the primary APT objective in these sectors.
Energy and critical infrastructure: APTs targeting energy grids, water systems, and transportation networks may aim for sabotage rather than data theft.
People Also Ask: Advanced Persistent Threats
What are the signs of an APT attack?
The most common signs include unusual outbound network traffic (especially to unfamiliar destinations), abnormal login activity, unexplained privilege escalations, unexpected changes to system configurations, and data being staged in unusual locations. Because APTs are designed for stealth, these indicators are often subtle and require correlation across multiple data sources to identify.
How long do APTs go undetected?
Industry reports consistently show median dwell times of 100-200+ days. Some APTs have operated inside networks for years before discovery. This extended dwell time is what makes APTs so damaging -- every day they remain undetected, more data is compromised and more access points are established.
What's the difference between an APT and regular malware?
Regular malware is typically automated, opportunistic, and designed for immediate impact (encryption, theft, disruption). APTs are targeted, human-operated, and designed for long-term stealth. APT actors adapt their tactics in real time, use custom tools, and persist through remediation attempts. Malware is a tool; an APT is a sustained campaign.
Can small businesses be targeted by APTs?
Yes, though typically as a vector to reach a larger target rather than as the primary objective. APT groups frequently compromise smaller companies in a target's supply chain -- managed service providers, software vendors, and business partners -- to gain access to the ultimate target's network.
How does Zero Trust help against APTs?
Zero Trust eliminates the implicit trust that APTs exploit during lateral movement. Instead of trusting devices and users based on network location, Zero Trust requires continuous verification of identity, device health, and access authorization. This means a compromised credential in one system doesn't automatically grant access to other systems -- significantly limiting an attacker's ability to move through the network.
How Motadata Helps You Detect APT Activity
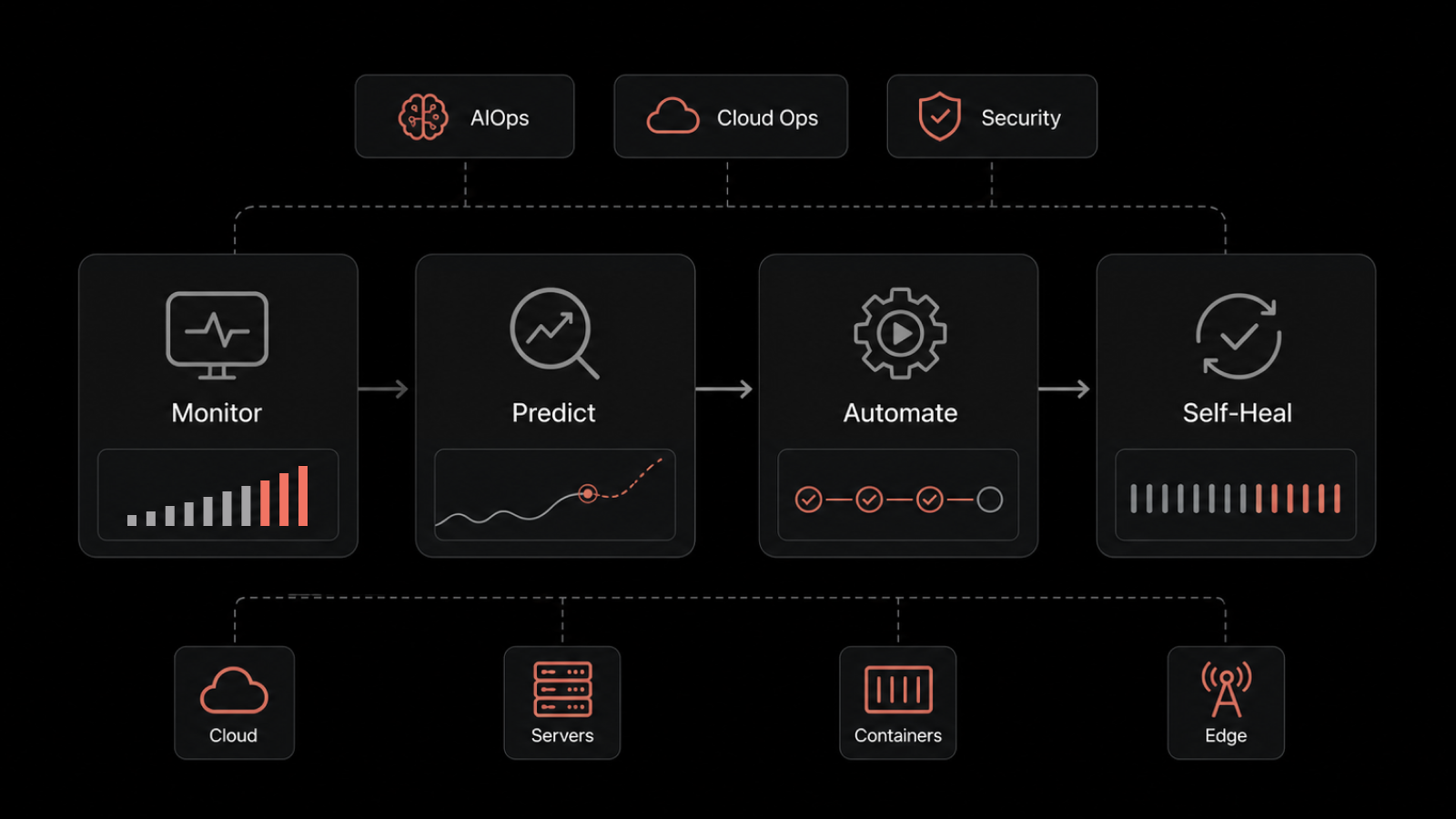
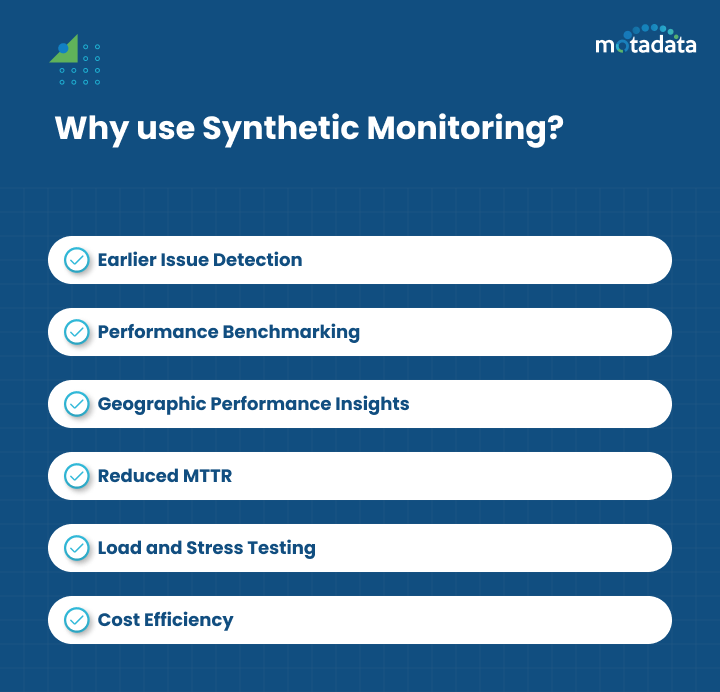
APT detection depends on visibility. If you can't see what's happening across your network, you can't spot the subtle indicators that distinguish APT activity from normal operations. Motadata's AI-native network monitoring and log analytics platform provides the continuous, infrastructure-wide visibility that APT detection demands.
With intelligent anomaly detection, real-time log correlation, and automated alerting, Motadata helps your security team identify unusual traffic patterns, abnormal access behaviors, and data exfiltration attempts before attackers achieve their objectives. The platform's AI-driven analytics surface threats that rule-based tools miss by establishing behavioral baselines and flagging deviations automatically.
Start a free trial to see how Motadata brings AI-powered threat visibility to your infrastructure.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.