Log Data Analysis for Security: How to Detect Threats, Meet Compliance, and Accelerate Incident Response
Amartya Gupta
Modern infrastructure generates log data at a pace that no human team can match. With cloud-native architectures, containerized workloads, and ephemeral environments spinning up and tearing down in seconds, the volume of machine data has grown exponentially. The old approach of manually reviewing log files on a weekly or monthly schedule simply doesn't work anymore. If your security posture depends on periodic log reviews, you're already behind.
Log data analysis is the practice of collecting, parsing, correlating, and interpreting machine-generated log records to extract security insights, identify threats, and maintain compliance. It turns raw system output into structured intelligence that security teams can act on immediately.
The challenge isn't a shortage of data. It's the opposite: organizations drown in logs without the tools to extract meaning from them. AI and machine learning have become essential for making log data analysis actionable at enterprise scale. Without intelligent automation, the sheer complexity of modern log environments renders manual approaches ineffective.
What Is Log Data Analysis?
Log data analysis is the systematic process of collecting, normalizing, and examining log records generated by applications, operating systems, network devices, security tools, and cloud services to identify security threats, performance issues, compliance violations, and operational anomalies.
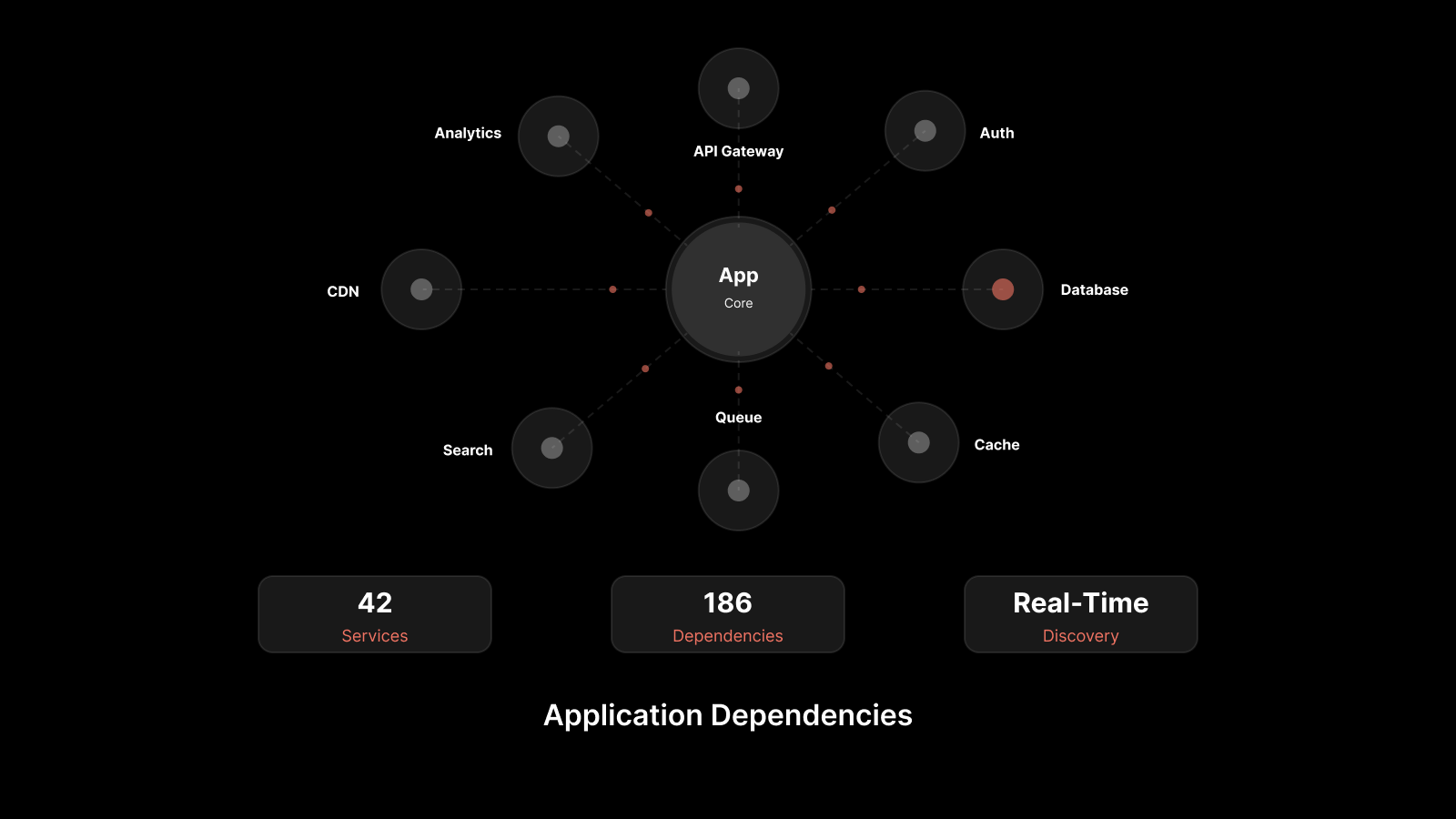
Every component in your IT stack produces logs — servers, firewalls, load balancers, databases, containers, APIs, cloud services, and endpoints. Log data analysis brings these disparate data streams together, correlates events across sources, and surfaces the patterns that matter.
The goal isn't just to store logs. It's to turn them into a continuous security feedback loop that detects threats early, accelerates root-cause analysis, and proves compliance to auditors.
Types of Log Data Sources
Understanding where your log data comes from is the first step toward building a comprehensive security analytics strategy. Here are the primary log source categories:
System logs: Operating system events, authentication records, kernel messages, and system state changes.
Application logs: Errors, transactions, user actions, and performance metrics generated by business applications.
Security logs: Firewall events, intrusion detection/prevention system (IDS/IPS) alerts, antivirus findings, and access control records.
Network logs: Traffic flows, DNS queries, proxy logs, and packet captures that reveal communication patterns.
Cloud logs: AWS CloudTrail, Azure Monitor, GCP Cloud Logging, and cloud-native service events that track API calls, configuration changes, and resource provisioning.
Container and orchestration logs: Kubernetes pod events, Docker daemon logs, and orchestration platform audit trails.
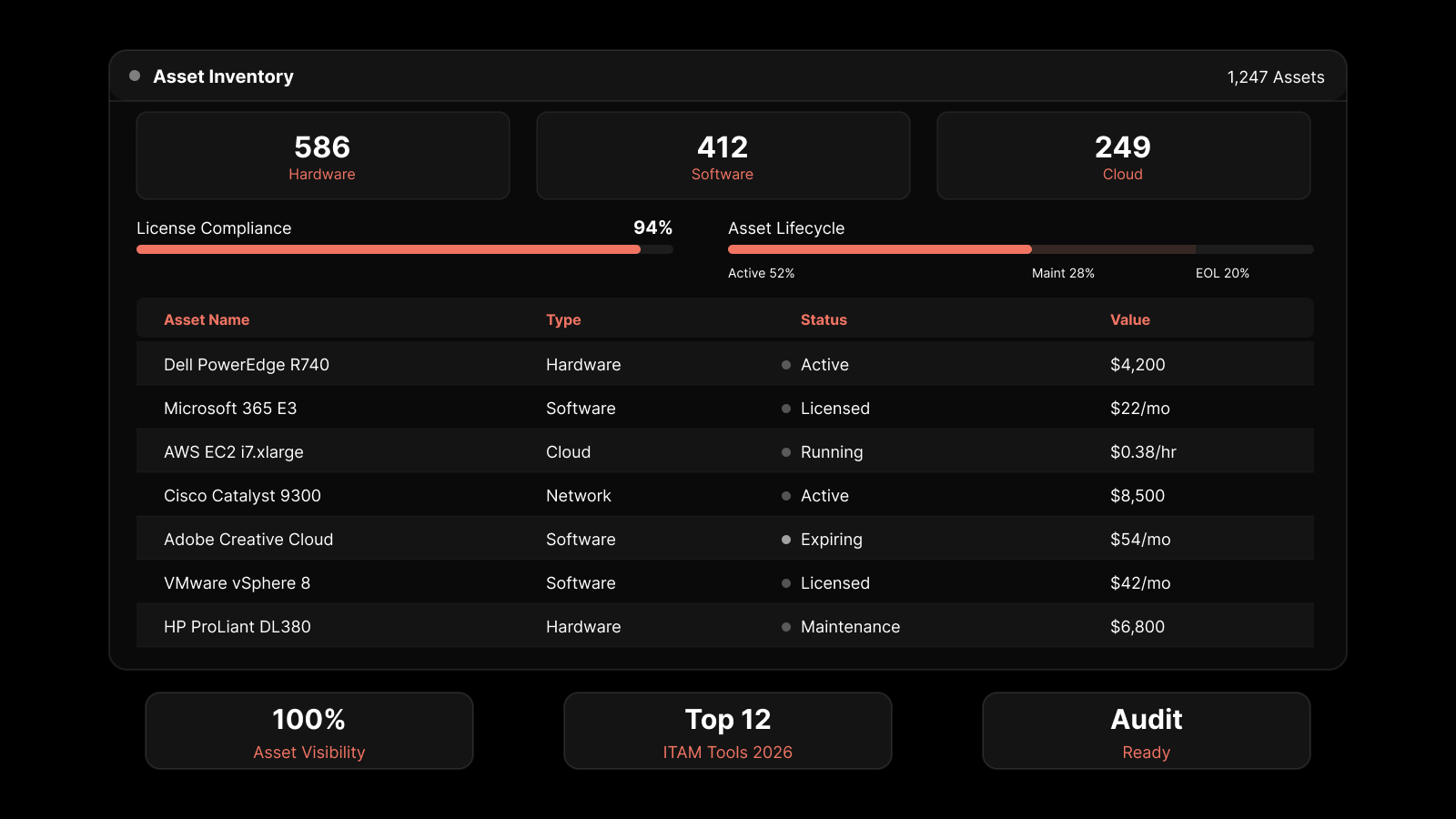
A mature log management strategy collects from all these sources, normalizes the data into a consistent format, and feeds it into a centralized analytics platform.
How Log Data Analysis Strengthens Security
Real-Time Threat Detection
The most critical capability of modern log analytics is real-time threat detection. Instead of discovering a breach days or weeks after the fact, AI-driven log management platforms analyze events as they occur. They apply behavioral baselines, statistical models, and threat intelligence feeds to identify anomalous patterns the moment they emerge.
Real-time log analysis catches:
Brute-force authentication attempts across multiple systems
Lateral movement patterns that indicate an active compromise
Unusual data exfiltration volumes during off-hours
Privilege escalation events that deviate from normal behavior
Configuration changes that weaken security controls
Root-Cause Performance and Security Analysis
Discovering performance bottlenecks and security issues requires an all-inclusive log management solution that works with data from every source in your environment. A strong platform analyzes log data to identify threats, surface trends, and help you meet compliance standards such as HIPAA, PCI DSS, FISMA, SOX, and GDPR.
Security analytics built on log data protect private information, prevent unauthorized access to files and folders, and detect breaches before they escalate. Modern solutions integrate SIEM capabilities, file integrity monitoring, host-based intrusion detection (HIDS), and anomaly detection to identify abnormalities swiftly.
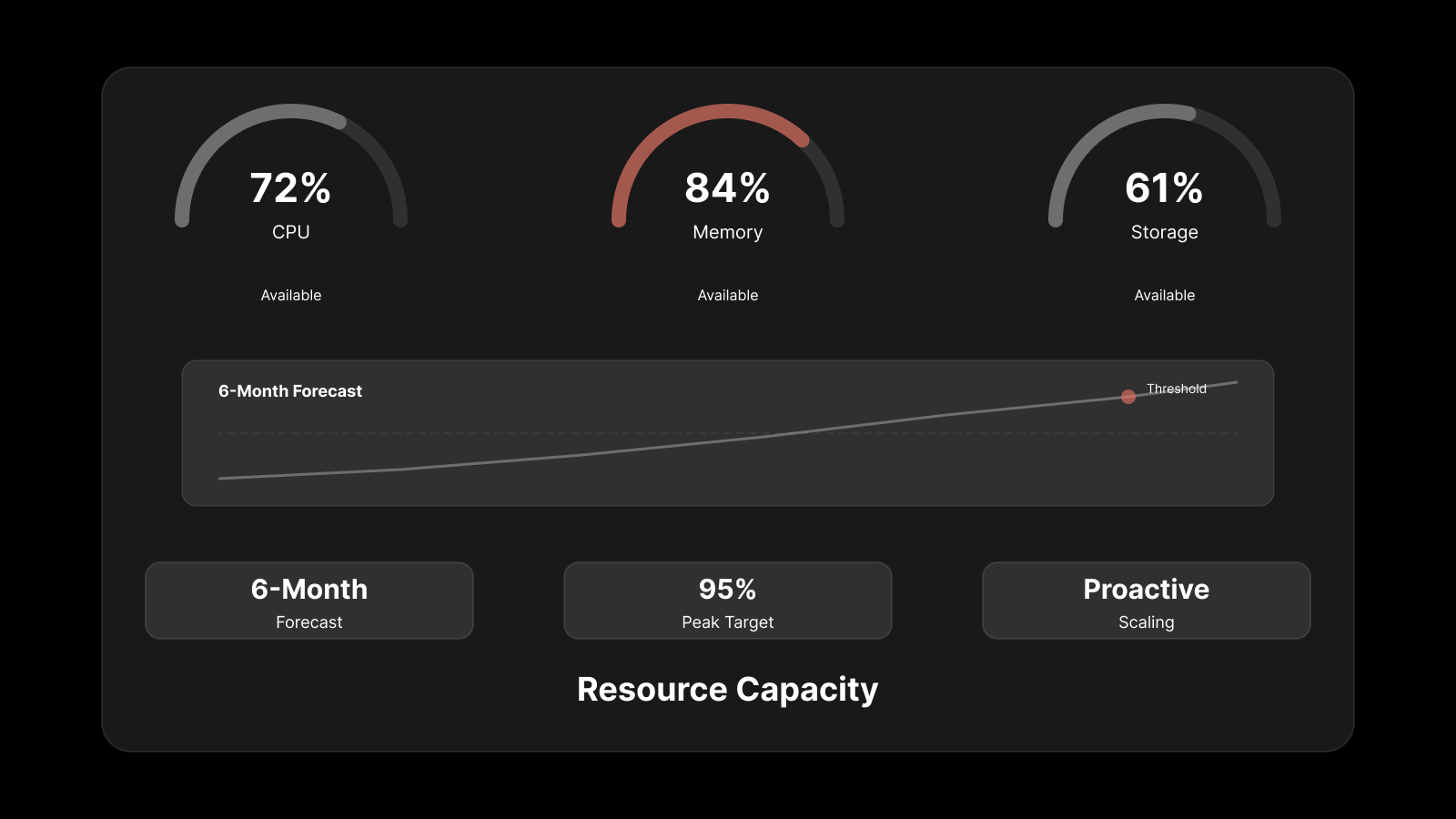
IT teams that rely solely on system metrics like CPU utilization, memory consumption, and storage miss crucial diagnostic information stored in log files. Log data analysis fills that gap by providing context that raw metrics can't.
Intrusion Monitoring and Management
Advanced log data analysis identifies anomalous activities and generates automated alerts in real time. Traditional manual log review consistently fails to extract insights related to emerging performance and security concerns. Automated log analysis frees IT administrators from monotonous review tasks while preventing data breaches through enhanced visibility into infrastructure operations.
Incident Containment and Response
Real-time alert configurations help identify and isolate underperforming or compromised elements before they cause broader infrastructure damage. Log data analysis identifies causal links between performance degradation and independent outages, spotting them before they escalate into full-blown incidents.
When an incident does occur, centralized log data dramatically reduces mean time to resolution (MTTR). Security teams can reconstruct the attack timeline, identify the blast radius, and contain the threat — all from a single analytics console.
Log Data Analysis for Compliance Management
Audit Trails and Forensics
Connecting log data across systems lets you trace suspected intrusions, investigate data loss events, and maintain compliance with stringent security regulations. Log data analytics is essential for dynamic provisioning, high-performance environments, and security hardening.
With centralized log analysis, you can:
Verify required data retention volumes and time periods
Monitor machine performance and availability
Assess data center and virtual network health
Identify security gaps and probable weak spots
Meeting Compliance Frameworks
Framework | Log Requirements | How Log Analysis Helps |
|---|---|---|
PCI DSS | Track access to cardholder data environments | Centralized log collection with tamper-proof audit trails |
HIPAA | Monitor access to protected health information | Automated alerts on unauthorized PHI access attempts |
SOX | Maintain audit trails for financial system changes | Change tracking with user attribution and timestamps |
GDPR | Log data processing activities and access events | Comprehensive access logging with retention policies |
FISMA | Continuous monitoring of federal information systems | Real-time event correlation and compliance dashboards |
Analyzing machine data helps you find trends and uncover hidden insights through event correlation analytics. You can set thresholds for critical events and receive notifications the moment something demands attention.
AI and Machine Learning in Log Analytics
Manual log analysis doesn't scale. As infrastructure complexity grows, AI-driven log analytics becomes the only viable approach for extracting security value from machine data. Here's how AI transforms log data analysis:
Behavioral baselining: ML models learn what "normal" looks like for every system, user, and process — then flag deviations automatically.
Pattern recognition: AI identifies attack patterns across millions of log entries that human analysts would never catch.
Automated correlation: AI connects events across disparate log sources to surface multi-stage attacks.
Predictive analytics: Models forecast potential failures and security risks before they materialize.
Natural language querying: AI-powered interfaces let analysts search logs using plain language instead of complex query syntax.
The shift from rule-based to AI-driven log analysis is one of the most significant advances in modern security operations.
Manual Log Review vs. AI-Driven Log Analysis
Capability | Manual Log Review | AI-Driven Log Analysis |
|---|---|---|
Speed | Hours to days | Real-time |
Scalability | Limited by team size | Scales with infrastructure |
Accuracy | Prone to human error | Consistent, pattern-based |
Threat detection | Reactive — after the fact | Proactive — as events occur |
Correlation | Single-source, manual | Multi-source, automated |
Compliance | Periodic, audit-driven | Continuous, automated |
Cost | High labor cost | Lower TCO at scale |
Infrastructure Optimization Through Log Analytics
Active network log management enables IT decision-makers to design infrastructure that meets evolving and diverse business demands. Log analysis provides insights into:
Machine provisioning and lifecycle: In advanced data centers, virtual machines move between physical hosts dynamically. Historical reporting on VM provisioning, moves, and decommissioning helps teams identify where process optimization is needed.
Virtual environment scaling: Log analysis equips decision-makers with precise visibility into VM efficiencies for planning provisioning, scaling, and operations across VMware, Hyper-V, Xen, AWS, and Azure environments.
Cloud resource optimization: Cloud log analysis tracks auto-scaling events, resource utilization patterns, and cost drivers — enabling teams to right-size their cloud spend while maintaining performance SLOs.
Strengthen Your Security With Motadata Log Analytics
Motadata empowers IT teams with real-time access to security analytics across their entire infrastructure. Our AI-native platform delivers:
Unified log collection from cloud, on-premises, hybrid, and containerized environments
Intelligent event correlation that connects the dots across disparate log sources
AI-powered anomaly detection that identifies threats before they escalate
Customizable dashboards with real-time visibility into security posture
Compliance-ready reporting for PCI DSS, HIPAA, SOX, GDPR, and FISMA
Threats constantly evolve. Maintaining visibility into traffic patterns, system behaviors, and log data helps you measure and improve security in real time. With Motadata's correlated analytics platform, advance your decision-making with actionable data insights.
Explore Motadata's unified observability platform and see how AI-driven log analytics transforms your security operations.
FAQs
What types of log data should I collect for security monitoring?
Collect system logs, application logs, security logs (firewall, IDS/IPS, AV), network traffic logs, cloud service logs (CloudTrail, Azure Monitor), and container/orchestration logs. Prioritize sources that handle sensitive data and critical infrastructure first.
How does log analysis help with incident response?
Log analysis provides a forensic timeline of events leading up to, during, and after a security incident. It helps teams identify the initial compromise, track lateral movement, assess the blast radius, and verify that containment measures are effective.
What's the difference between structured and unstructured logs?
Structured logs follow a consistent format (JSON, key-value pairs) that's easy to parse and query. Unstructured logs are free-text entries that require parsing and normalization before analysis. Modern log platforms handle both, transforming unstructured data into queryable fields.
How do I reduce alert fatigue in log monitoring?
Use AI-driven baselining to suppress expected events, whitelist approved changes, correlate alerts with change tickets, tune detection rules based on your environment, and implement tiered alerting that escalates only high-confidence, high-impact findings.
Can cloud-native environments benefit from log data analysis?
Absolutely. Cloud-native environments generate massive log volumes from microservices, containers, APIs, and serverless functions. Centralized log analysis is essential for maintaining security visibility, debugging distributed systems, and meeting cloud compliance requirements.